
Wright State University
2017 CUSTOMER SATISFACTION SURVEY
Computing and Telecommunications Services
1
Table of Contents
Please select your primary role:
......................................................................................... 2
What college/area are you affiliated with (Staff)?
............................................................... 3
What college/area are you affiliated with (Faculty)?
........................................................... 5
Overall, please rate your level of satisfaction with the quality of service you receive from
CaTS. ............................................................................................................................... 6
Please specify why you are dissatisfied with the quality of services:
..................................... 7
Overall, please rate your level of satisfaction with the timeliness of
service you receive from CaTS.
9
Please specify why you are dissatisfied with the timeliness of services:
........................... 10
Overall, please rate your level of satisfaction with the variety of services
currently offered by
CaTS.
.............................................................................................................................. 11
Please specify why you are dissatisfied with the variety of services:
......................... 12
How satisfied are you with the timeliness and quality of communications
coming from CaTS for
scheduled and unexpected service disruptions?
.................................................................... 13
What is your primary piece of technology used while on campus?
..................................... 15
How often do you utilize the computers available in the computer labs?
............................ 17
What services would you like to see training offered for?
.................................................. 19
Please select the following services you are aware of that are available
to Students:
....... 25
If CaTS provided access to high performance computing (HPC) capabilities at no charge
to you, how likely would you be to utilize that service? .................................................. 27
I find value in notifications from CaTS regarding phishing scams.
....................................... 28
I find more value in checking a website for updates about current
phishing scams than receiving
email notifications from CaTS.
............................................................................................ 29
I find value in the monthly IT Security Newsletter:
............................................................ 30
Please provide feedback on activities and services that you feel CaTS
performs well (maximum of
500 characters):
............................................................................................................... 31
Please provide feedback on activities and services you feel CaTS could
improve (maximum of 500
characters):
.................................................................................................................... 46
Please provide any additional comments (maximum of 500
characters) ................................... 53

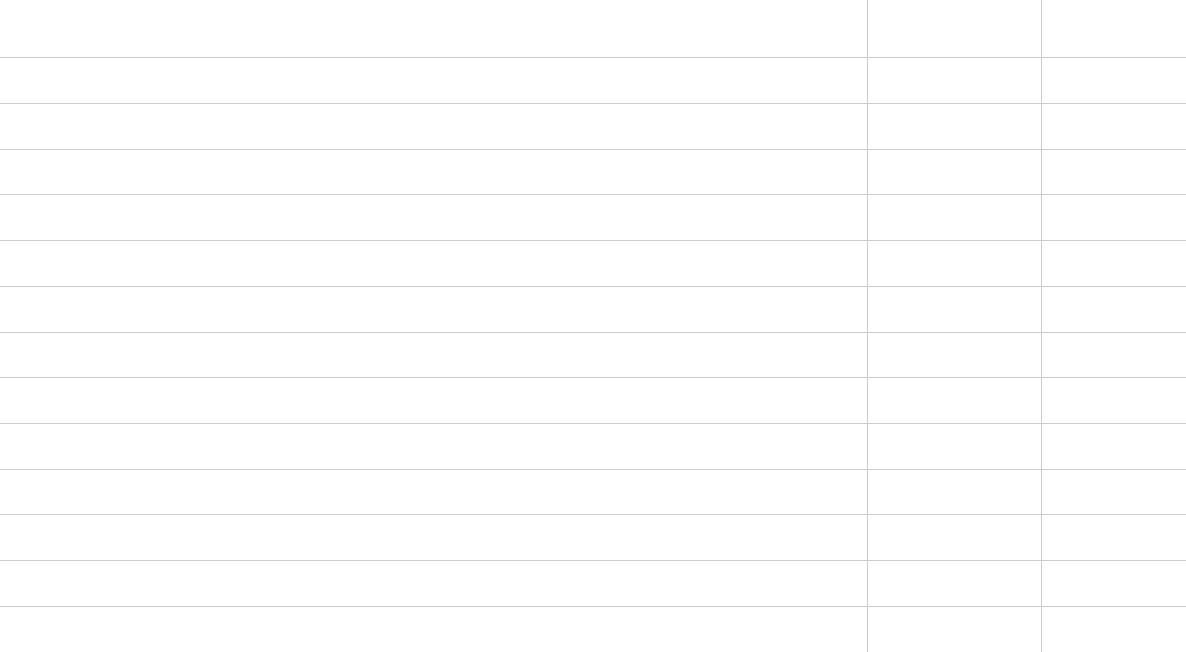
2
CaTS Customer Satisfaction Survey 2017
Please select your primary role:
Answer
%
Response
Faculty
16.42%
147
Staff
28.60%
256
Student
41.68%
373
Alumni
6.82%
61
Other
6.48%
58
Total
100%
895
Faculty Staff Student Alumni Other

3
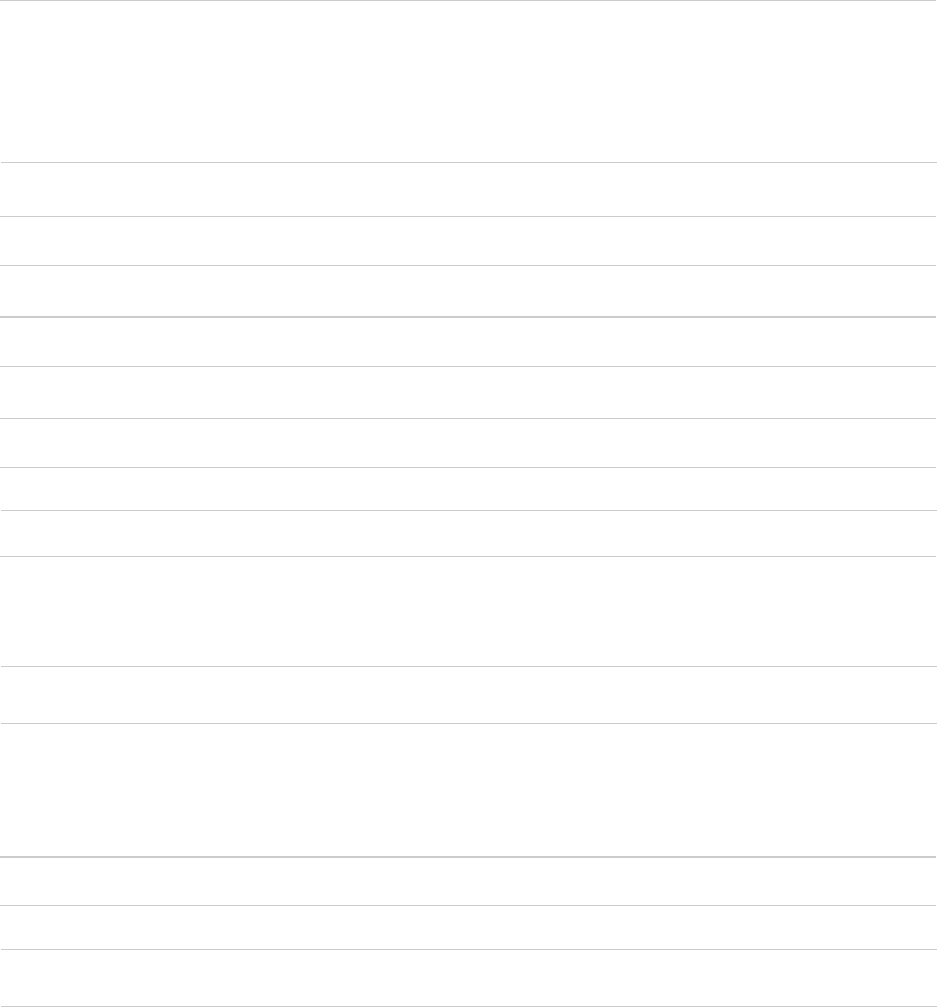
What college/area are you affiliated with (Staff)?
Answer
%
Count
Academic Affairs, Division of
1.96%
5
Advancement
2.75%
7
Alumni Association
0.78%
2
Board of Trustees
0.00%
0
Boonshoft School of Medicine
16.08%
41
Business and Finance, Division of
5.49%
14
Campus Auxiliary and Business Services
0.00%
0
CaTS
8.24%
21
Communications and Marketing
1.57%
4
Compliance, Office of
0.39%
1
CTL
1.18%
3
Education and Human Services, College of
2.75%
7
Engineering and Computer Science, College of
3.53%
9
Enrollment Management
3.14%
8
Executive Vice President for Planning
0.39%
1
Facilities Management and Services
1.96%
5
Faculty and Staff Affairs
0.00%
0
Financial and Business Operations
0.00%
0
General Counsel
0.39%
1
Graduate School
0.00%
0
Human Resources
2.35%
6
International Education, University Center for
0.78%
2
Lake Campus
3.14%
8
Liberal Arts, College of
2.35%
6
Libraries
6.27%
16

4
Multicultural Affairs and Civic Engagement
0.00%
0
Nursing and Health, College of
1.57%
4
Nutter Center
0.39%
1
Physical Plant
1.57%
4
President, Office of the
2.75%
7
Professional Psychology, School of
2.75%
7
Provost, Office of the
2.35%
6
RaiderConnect
0.00%
0
Raj Soin College of Business
3.92%
10
Research, Office of the Vice President for
2.75%
7
Residence Life and Housing
0.39%
1
Science and Mathematics, College of
3.53%
9
Student Affairs
7.06%
18
University College
1.57%
4
University Police
0.39%
1
WSRI
1.57%
4
Other
1.96%
5
Total
100%
255
5
What college/area are you affiliated with (Faculty)?
Answer
%
Count
Administrative Office
0.00%
0
Boonshoft School of Medicine
15.65%
23
Education and Human Services, College of
14.97%
22
Engineering and Computer Science, College of
8.16%
12
Lake Campus
2.04%
3
Liberal Arts, College of
23.13%
34
Nursing and Health, College of
6.80%
10
Professional Psychology, School of
2.72%
4
Raj Soin College of Business
6.12%
9
Science and Mathematics, College of
19.73%
29
University College
0.00%
0
Other
0.68%
1
Total
100%
147

6
Overall, please rate your level of satisfaction with the quality of
service you receive from CaTS.
#
Answer
%
Count
1
Very Dissatisfied
1%
7
2
Dissatisfied
2%
17
3
Neutral
12%
86
4
Satisfied
34%
250
5
Very Satisfied
50.95%
374
Total
100%
734

7
Please specify why you are dissatisfied with the quality of services:
•
Connection issuespeed and throttling
•
Could never get anyone to repair computer and printer despite multiple calls
•
The Wi-Fi is very slow. Maybe if you guys didn't update your firewall every week, we would
not have as many issues.
•
Website down all the time, network down all the time.
•
Wifi pales in comparison of other colleges.
•
Not very efficient and make so many mistakes
•
I'm out of state and have had to call twice for help with syncing my email to my phone. Was
put on hold both times and the second call I was transferred multiple times.
•
They are rude unhelpful and take forever to help just one person
•
The Wi-Fi issues continue.
•
CATS needs to stop instituting security policies that decrease my security. 1) Your password
policy sets a *maximum* password length. I cannot overstate how stupid that is. Consider
these three ways of generating a password: For the first, we randomly select 7 letters, then
end it with a random digit. This approach is permitted by your policy (and is the one most
likely to be used by the sort of naive users who necessitate the existence of password policies
in the first place). It has an entropy of 36.2. For the second, let's assume that we just choose
4 words out of the 20,000 most common words. This violates three distinct rules of your
policy: 8-14 characters, at least one special character, and no common words. And yet, its
entropy is 57.2. Which is to say, it's *2 million* times harder to brute force than the one you
allow (and that assumes the attacker knows exactly what dictionary we used). Easy to
remember, too. Finally, we have a generation method that creates passwords that are
reasonably secure (but not as secure as the one you disallow), somewhat easy to remember
(albeit not as easy as 4 common words would be), and that actually fit in 14 characters: We
alternate consonants and vowels for 12 characters, then append 2 digits on the end. It'll be
pronounceable, it not meaningful, and we only need to remember 6 syllables and one
number, instead of 14 arbitrary characters. Its entropy is about 46.9, so only 1000 times
worse than the approach you ban. Probably the best compromise solution, given the
constraints. But if you would allow arbitrarily long passwords, we wouldn't *need* to
compromise. I'd like to point you at Stanford's policy as an example of a password policy
designed by people who know what they're doing:
https://uit.stanford.edu/service/accounts/passwords/quickguide. They have the standard
requirements on what types of characters must be included when the password is too short
to be especially secure (e.g. 8-14 characters long or so), but when the password is a
reasonable length, they neither have nor *need* additional restrictions: with enough length,
a password is almost impossible to brute force even if it's all lowercase. 2) You automatically
replace all links in email with a link to a third party service that checks if they're dangerous.
This both breaks my spam filter, which would otherwise be able to identify links where the url
doesn't match the text as likely scams, and also means that any link with secret information

8
(e.g. any sort of multifactor authentication that uses email) is being shared with a third party.
This service at least has some benefit, unlike the maximum password length, but there needs
to be a way to opt out of this for those of us who would be more secure without it.
•
Have requested CATS to repair my printer 3 times without success. Computer also is not
working correctly. Problems still unresolved.
•
My wings express password worked just fine one every device besides the computers in a
computer lab where I have a class. When I called I was told I had to change the password to
get it to work at the computer labs. This makes no sense to me as the password was good. I
was given a a random new password which I know have to use. I can now log into the
computer lab just fine but it still seems like there should have been a different fix.
•
The problem wasn't fixed
•
The person I talked to was somewhat rude
•
Constant throttling and intermittent signals. The network cannot handle the number of
devices on campus properly
•
It seems like there are more internet outages and loss of access to certain applications like
email than I've experienced at other institutions. This is compounded by the fact that I live on
campus and all campus buildings use the same internet. As I spend the majority of my time at
school or at my house, a internet outage affects my ability to study since nearly all of our
coursework is stored and accessed online.
•
1.Only one scanning machine is always broken in the basement lab of Rike. It has to be
checked frequently or add second and third scanners. 2. Often printing is impossible after
11:00 pm in the same room
•
Wifi sucks in campus housing...
•
Wifi always been in trouble to connect, some time can't open web or can't deliver message,
email.
•
First: this is a survey about CaTS. I'm not 100% sure what CaTS even is. Are you responsible for
all tech on campus? Perhaps define yourself before asking my opinion about you. Passwords
are confusing and change across platforms. Further, using a "w", "U" number, or email
address as your login name, depending on the site, is ridiculous.
•
Have had a major issue with pilot and have contacted cats on several occasions. The problem
is yet to be resolved and every time I call the issue is escalated and I'm promised a response
and a fix which is yet to happen. I have followed up multiple times and the only response I get
is another ticket is created with no follow through. Also, every agent I talk to seems totally at
a loss to help me because I have a Mac computer. There is simply no excuse for their lack of
knowledge about a mainstream brand of computer.

9
Overall, please rate your level of satisfaction with the timeliness of
service you receive from CaTS.
#
Answer
%
Count
1
Very Dissatisfied
0.68%
5
2
Dissatisfied
1.77%
13
3
Neutral
12.81%
94
4
Satisfied
33.92%
249
5
Very Satisfied
50.82%
373
Total
100%
734

10
Please specify why you are dissatisfied with the timeliness of services:
•
Every time I want to use CaTS I have to login, which is obviously necessary, but I always have
trouble because the passwords must change every few months, so I can never get used to a
password. The passwords are made worse by all of the Requirements and criteria. This makes
it very hard to keep any semblance of your original password, so you can't even memorize
some of it. Also this box does not have any spell check, which would be nice to have. (I would
use google surveys, not this).
•
Never came when promised
•
See above
•
It takes a long time to fix one computer. ....
•
Why does it take forever to create accounts (usernames/passwords) for people? Why does
the form need to be inked signed? This process needs work
•
I was late to class, it took forever
•
took too long to get someone out to my office
•
Sometimes it takes half a day to restore internet connectivity.
•
its slow
•
over-promised and underdelivered
•
It has taken multiple days to receive a response to an emailed issue.
•
If password reset options aren't available online, then tech support should be available
24/365 without sitting on hold.
•
There has been ZERO follow through on my issue. It's been over a month and nothing.

11
Overall, please rate your level of satisfaction with the variety of services
currently offered by CaTS.
#
Answer
%
Count
1
Very Dissatisfied
0.68%
5
2
Dissatisfied
1.50%
11
3
Neutral
16.08%
118
4
Satisfied
34.88%
256
5
Very Satisfied
46.87%
344
Total
100%
734

12
Please specify why you are dissatisfied with the variety of services:
•
Same
•
Because the wifi is terrible.
•
Slow server times delay electronic quizzing in SSC classrooms. It can take weeks for a single
laptop to be replaced in SSC. Synchronous sessions via Pilot Live sometimes experience
technical difficulties when the instructor is moderating the course from a campus computer.
There are sometimes problems connecting to WSU-Secure.
•
There are no computer labs designated as "No Talking."
•
I like to use an email program called Incredimail. This program is not supported by CATS.
•
Internet quality needs improvement in University buildings such as the Student Union
•
I have no idea what services you offer, other than emails about disruptions and password
resets.

13
How satisfied are you with the timeliness and quality of communications
coming from CaTS for scheduled and unexpected service disruptions?
#
Answer
%
Count
1
Very Dissatisfied
0.95%
7
2
Dissatisfied
1.77%
13
3
Neutral
13.90%
102
4
Satisfied
36.38%
267
5
Very Satisfied
47.00%
345
Total
100%
734

14
Please specify why you are dissatisfied with the timeliness and quality of
communications:
•
When the service of my PC was delayed, I was not notified.
•
It took weeks for the wifi to be fixed
•
Sometimes we're never told!
•
Are you offering trainings? I never see any announcements for training session except when
they are affiliated with A-Team or Staff Development Day.
•
We used to get informed about lapses in service, they no longer take place so I don't know if
they are aware or not of lapses.
•
Internet doesn't work half the time I'm on campus...
•
The wifi never works
•
9/10 times I'm already aware that the network is down for over an hour before the notice is
out
•
I feel like service disruptions are common and only partly notified about
•
Too many emails
•
I have wifi issues at least once a week on campus. It's wonderful that CaTS responds so quickly
to the problems, but, of course, no one can predict how long the issues last or when they are
coming up. It's just annoying that the wifi always has issues when I have a ton of work to do
and the wifi has issues.
•
I've been fortunate to attend multiple institutions, and the number of disruptions (and emails
about disruptions) at Wright State dwarfs all the others combined.

15
What is your primary piece of technology used while on campus?
#
Answer
%
Count
1
Personally Owned Device (laptop, tablet, mobile device, etc)
90.91%
20
2
General Labs, Library, ERC, Open Computer Lab
0.00%
0
3
Laptops2Go Computers
0.00%
0
4
Other (Please Specify):
9.09%
2
Total
100%
22

16
Other (Please Specify):
school computers
Work computer

17
How often do you utilize the computers available in the computer labs?
#
Answer
%
Count
1
Never
19.28%
48
2
Rarely
24.10%
60
3
Occasionally
30.52%
76
4
Frequently
21.69%
54
5
Always
4.42%
11
Total
100%
249

18
What additional training do you need to better integrate technology in
your job/position?
•
More timely notice about workshops on technology
•
Need to keep updated on the technologies most commonly used in the k-12 settings
•
none
•
Would like to be able to meet with CaTS staff maybe 1-2x/term to "toss around ideas" for
enhancing content delivery. I have ideas on what I would like to do however I lack practical
experience with emerging technologies that help students from remote locations learn
content. CaTS could also learn what faculty are doing during these working sessions, and both
grps. could perhaps form partnerships or at minimum gain ideas and support. Also, since my
college (CEHS) has opted not to replace computers/laptops and won't do so again for the
coming 2017-18 academic yr. it would be helpful for CaTS to reach out and provide support
such as (idea): Invite faculty to meet with CaTS reps. on 2-3 diff. dates/times re. maintaining
our existing computers and troubleshooting issues. If you could provide help on the spot (as
much as is possible) that would encourage faculty to work with CaTS. I know of a colleague
whose laptop is so slow she can't use it for publishing or data collection.
•
No additional training needed.
•
Make it easier to access items under Pilot.
•
Ways to assist students in seeing the value of technology in the workplace.
•
I just use PowerPoint and the Elmo in the classroom. I would love to be able to use the
SmartBoard.
•
I need to take advantage of more CTL workshops so I am more comfortable with advanced
Pilot functions and learn how to use Panopto. It is possible to offer workshops during the
summer?

19
What services would you like to see training offered for?
CaTS is in the process of developing training for the following services:
•
Banner
•
Email/Calendar
•
SharePoint Sites
•
Skype for Business
•
OneDrive for Business
What other services would you like to see training offered for?
•
MS Office Cognos
•
Pilot Google Document and/or Dropbox --- Particularly utilizing live document
viewing/editing in classroom situations TurningPoint
•
Pilot Access
•
None
•
Online education is my major concern--it is vital that WSU grow enrollment in this arena and
the need for tech support for course delivery (as well as development) is critical. As you know
we lost Fernando Smith in RSCOB and he provided great value supporting my online MBA
class. I am worried that we will drop the ball in this area--FYI--University of Dayton will launch
an online MBA in fall semester. We (WSU) should also be leading the way in undergrad
online programs--it's one way we can save ourselves from the demographic trends that will
continue to be "in the wrong direction" in Ohio. Our budget deficit needs it!!!!!
•
None
•
None
•
Skype for Business, Banner
•
N/A
•
Skype
•
Excel, Microsoft Access, IT skills for managers
•
None needed at this time.
•
N/A
•
Software upgrades (eg new windows platform)
•
Salesforce
•
Nothing outside above courses.

20
•
All of the above
•
onedrive
•
I would like HR to have videos available for training and information gathering.
•
Adobe forms, photoshop and other adobe software, Drupal, creating webforms using drupal
(maybe partner with Com and Marketing for these sessions),
•
One Note
•
Task Stream
•
Don't end a sentence (or question with a preposition). For what other services would you like
to have training offered?
•
Microsoft Access
•
N/A
•
COGNOS
•
More on Excel. I know the basics but would like to be able to do more with Excel.
•
I do not use Pilot to its full capacity. I would like to learn more about how to maximize the
service.
•
Ways existing WSU licensed tools can be used to increase efficiency and address needs or
problems within the university. Perhaps work with CTL to offer workshops targeting staff and
non-academic uses of tools they manage (Pilot for online training, clickers for staff and
department use, etc)
•
The list above will be very helpful...Thank you
•
Banner; Banner Finance
•
Wright Buy
•
n/a
•
Reports, queries, and journal voucher submission on the Finance tab in Wings Self-Service
•
That's a good list - thanks!
•
Adobe software products
•
Tegrity/Panopto
•
Cognos Report training
•
I just don't understand how to navigate the "cloud". I would like to remove stuff, but it never
goes away...
•
n/a
•
Microsoft Office training

21
•
none
•
unsure
•
Please make sure it is Banner academic, not Banner Finance. I've been skunked on that one a
couple of times.
•
cyber security basic computer "maintenance" and trouble shooting for the home (updating,
backups, virus protection, disk scanning, cookie cleaning, security settings) How to use the
cloud (setting up devices, why the cloud makes sense, organization, security, sharing) working
with digital and audio files
•
High performance computing (HPC). After accessing the link provided I still do not understand
what this is.
•
Microsoft Office Specialist Certification Training/Testing, IC3 Internet and Computing Core
Certification
•
Blackboard Collaborate Ultra
•
Any and all of the above would be helpful. Please consider training sessions (or make the
sessions available online) for Lake Campus.
•
N/A. I'm excited to take training in SharePoint!
•
Some type of online FERPA training?
•
Other than the ones already listed, none that I can think of.
•
Collaboration software for group work with students in class
•
PL/SQL
•
Adobe products
•
Microsoft Project Autodesk Revit
•
It would be helpful to have beginner, immediate, and advanced levels offered as I, II, III.
Ideally, a proficiency "test" would be available to help user choose/identify their level.
•
BIM software, Adobe Creative Cloud
•
No other services.
•
My students submit videos to me via Panopto - it has been a struggle for some. I don't know
it well enough from that perspective to help them or give them better instructions.
•
Not sure at this time.
•
Qualtrics Microsoft Excel or other related software to assist with data analysis
•
Can't think of any
•
Clickers
•
Skype for Business, Sharepoint sites, One Drive
•
More than adequate coverage exists. An additional option for training would be to provide
training regarding an introduction to how a staff member or faculty might use the various

22
services in combination. In other words a day long workshop discussing the convergence of
available services/resources across the multiple needs of a staff or administrators job roles
(marketing, recruitment, student outcome, etc.).
•
None that I can think of, but I am a pretty low-level user; I mostly use word processing,
Powerpoint, and Excel.
•
Task Stream
•
Every software or platform we use and/or have available. Training is not provided by
departments.
•
More Service Now training geared towards the need of the individual.
•
Creative Cloud/Adobe
•
Word; Excel; Outlook
•
Computer security. Mobile security. Email and text security. I use all of these for WSU work. Is
there a checklist to see if your computer is secure? I know you have virus protection but it's
not clear which one to pick. I also do work on a home laptop and am unclear if the virus
protection is up to date and if it is the right one. I guess I could call Help Desk, but a checklist
or reminders/info would be helpful. Maybe this is in your newsletter... Sorry I must be
overlooking a monthly security newsletter. Maybe I get it and just don't realize it. I get so
much stuff.
•
Making documents accessible to those with disabilities
•
Pilot Live.
•
Excel
•
Microsoft products for intermediate and advanced people.
•
Intermediate sql using Banner tables
•
I really don't have time for any more classes unless it's about something new.
•
MS Office - be more productive with tools such as format painter, formulas, etc.
•
Auditorium AV setup and use. Skype for Business, Protecting Sensitive information (HIPAA,
FOUO, ITAR, EAR).
•
Office 365 (with a comparison to the client version of Microsoft Office)
•
For newer employees, specialized training in COGNOS and other Banner segments would be
helpful. Faculty could benefit from training for effort reporting.
•
N/A
•
SmartBoard
•
Microsoft Office apps (Outlook and Calendar online as well as Outlook and Excel on a desktop)
Drupal
•
Adobe Acrobat
•
Banner Admin.

23
•
Pilot and Lockdown Browser Troubleshooting
•
Skype for Business One Drive for Business
•
Ways to become proficient at Power Point Presentations
•
Excel
•
CRM and Marketing Clout
•
Panopto
•
None
•
I think this list covers most of the training needs for campus.
•
WingsExpress
•
If possible COGNOS?
•
I would like to see training on the services mentioned above (Home Base/Atomic
Learning/ProPlus/Equipment Checkout and Classroom Equipment Training. Although I am
familiar with the ones checked off, I can find value in a refresher course, or even further
information on the areas not checked.
•
Would LOVE Banner training!
•
N/A.
•
One drive working more consistently with large files... :P
•
Excel; I'll teach it!
•
n/a
•
Email best practices and email system/processes, i.e. how best to manage email, how to set
up an email "communication" tracking system that's workable. I work with a lot of external
3rd party partners (i.e. vendors and publishers) and therefore need to retain emails as "proof"
of what they said they would do etc. How does one EFFICIENTLY manage 100+ email folders
so that things on MY end don't fall through the cracks? [And please don't refer me to the
Libraries' program as that doesn't help]. I basically need something like Service Now for
external partners.
•
If you could figure out how to get Pilot to work smoothly for grading and teacher/TA
evaluation, that would be great.
•
When Patrick Kucharchek (sp) was here in '07-'10ish (I forget when he left), he often offered
basic-intermediate sessions on Word, PowerPoint, Excel, etc. It was good to go to those for
brushing up on skill sets or finding out there was yet another icon that you didn't know
existed or that it existed but didn't know how to use.
•
COGNOS (non-advising)
•
you offer more things than i can use now!

24
•
Excited about banner training.... sooner the better please social media: include twitter,
instagram etc.....blogging, youtube, and now pinterist
•
WorkFlow Management. Specifically, what products are in use now if any and what
recommendations for upgrade or implementation. To include do
•
N/A
•
N/A
•
Xerox printer training for FACULTY

25
Please select the following services you are aware of that are available
to Students:
#
Answer
%
Count
1
Laptops2Go
78.80%
171
2
Home Base
43.78%
95
3
Atomic Learning
10.60%
23
4
ProPlus (Free Microsoft Office)
60.37%
131
Total
100%
217

26
Please select the following services you are aware of that are available
to Faculty and Staff:
#
Answer
%
Count
1
Home Base
69.39%
229
2
Atomic Learning
41.21%
136
3
ProPlus (Free Microsoft Office)
53.64%
177
4
Equipment Checkout from CaTS
71.52%
236
5
Classroom Equipment Training
60.00%
198
Total
100%
330

27
If CaTS provided access to high performance computing (HPC)
capabilities at no charge to you, how likely would you be to utilize that
service?
#
Answer
%
Count
1
Not Likely
40.60%
54
2
Somewhat Likely
42.86%
57
3
Very Likely
16.54%
22
Total
100%
133

28
I find value in notifications from CaTS regarding phishing scams.
#
Answer
%
Count
1
Strongly Disagree
1.24%
9
2
Disagree
1.65%
12
3
Neither Agree or Disagree
13.89%
101
4
Agree
36.73%
267
5
Strongly Agree
46.49%
338
Total
100%
727

29
I find more value in checking a website for updates about current
phishing scams than receiving email notifications from CaTS.
#
Answer
%
Count
1
Strongly Disagree
14.78%
17
2
Disagree
13.91%
16
4
Neither agree nor disagree
56.52%
65
6
Agree
11.30%
13
7
Strongly agree
3.48%
4
Total
100%
115

30
I find value in the monthly IT Security Newsletter:
#
Answer
%
Count
1
Strongly Disagree
4.43%
28
2
Disagree
7.44%
47
3
Neither Agree or Disagree
42.72%
270
4
Agree
32.75%
207
5
Strongly Agree
12.66%
80
Total
100%
632

31
Please provide feedback on activities and services that you feel CaTS
performs well (maximum of 500 characters):
•
I called and you were very friendly.
•
Helpdesk response, love the Bomgard feature. Most times they are able to pop in, resolve
and I'm on my way.
•
The help desk staff members are always extremely helpful, courteous and informative.
•
Assisting with computer issues. I have used them just a few times where they remotely
accessed my computer to find a lost paper. These few times have been Invaluable!
•
electronic classroom support
•
Help Line usually is very helpful in resolving my issues quickly.
•
CaTS does very well with being timely with their messaging (on a personal and University
level). They have lots of access hours, too, and good people. Their computer labs are well-
maintained as well.
•
Getting wifi fixed. Alerting me of scams.
•
I found they troubleshot on-camplus problems real well.
•
I am a retired staff member. I have rarely had to call the Help Desk for a question but when I
have called I have always been treated with respect and have always had my question/issue
resolved. You definitely have hired skilled, knowledgeable, helpful, respectful individuals -
and I thank you !!
•
Troubleshooting
•
I have just set up accounts etc. In my mind, this is way too difficult. I have been sitting here
for 2.5 hours & just finished wings, wings express, setting up my email acct and email to my
smart phone and I had to call support to figure out that I had to log on to Wright. Force first
which is nowhere in any paper that was received from WSU. This really needs to be
streamlined
•
solving every problem that comes up... one way or antoher
•
I believe that CaTS performs maintenance of the campus Wi-Fi service well.
•
I have been very fortunate to receive quick responses to issues encountered with either my
office computer or computer programs used in my area. Please keep this same service if
possible dependent upon the university financial issue.
•
I have always appreciated CATS for their help in whatever areas I have needed with my
computer operation and it's programs. The staff have always been so wonderful,

32
understanding and have never made me feel like I should know how to do something etc. I
am proud of the fact that WSU provides this service to the entire campus ( including staff like
myself). I appreciate each and evrey one of the technicians who have helped me over the
years. Go CATS!! Sincerely, Melanie Miller BSOM/SATC
•
customer service. They're always nice and very informative.
•
CaTS is always prompt and helpful.
•
This is the most helpful office on campus. Knowledgeable, friendly service delivered
promptly. Staff delivers excellent customer service. Laptops2go is essential to my success
this semester. Thank you to a great team.
•
Short- notice focused assistance with nuisance problems that I can't fix - but are simple
matters for an IT pro.
•
Help desk does a good job of trouble shooting computer problems. Good support from
Debbie W. and Classroom Technology. Very positive interactions with Mike Natale on
security issues. Darrin has been proactive in responding to our needs. Michael Stankas and
Craig Woolley provided invaluable assistance with the selection of our new electronic health
record system. Staff indicate that there is good communication with CaTS.
•
Overall I am happy with the computer support that I receive from CATS in both my office and
the classroom.
•
I am satisfied overall with all the services CaTS provides.
•
I have contacted CaTS about Pilot quiz and drop box issues, they have always been helpful
•
Virus protection
•
love the help desk folks.
•
Friendliness of staff when calling and seeking assistance. Both times I have called the staff
were wonderful
•
My email account works as I expect
•
I appreciate timely notices about maintenance and phishing scams. Even if I'm not affected by
the service interruption and am careful about my email, the CaTS notices provide peace of
mind.
•
Help Desk services are excellent, particularly Virginia. Jeff Bowman does an amazing job of
processing account apps for our incoming trainees. On-site services (computer repair) are
excellent. They usually get to us in a timely manner, are cognizant of true emergencies, and
provide excellent instruction/guidance/support.

33
•
I appreciate the free laptop service and the ability to borrow laptops if anything happens to
my personal device. Service is friendly and effective!
•
If I call Cats to report a problem I am having and they answer in a timely manner and fix the
problem that I have called about, that is in itself good enough for me. I'm not real hard to
please.
•
Love the help desk!
•
Several internet connection issues that have cause me and several others to be able to work
at a sufficient time.
•
Offering great deals on technology available for purchase
•
I think CaTS is really great about letting us know when there are going to be issues with our
service.
•
I don't even know how you guys help to be honest. Wifi is worse here than at home.
•
Troubleshooting issues on the computer. Installation.
•
Great and fast classroom response when I call with an issue.
•
Anytime I have an issue with my system, a representative takes remote control over my
system to thoroughly understand my issue. This is truly appreciated because it allows me to
talk them through while they are looking at my system, instead of me explaining, them blindly
trying to understand, then possibly gaining remote access. Everyone is always very
professional and knowledgeable.
•
I am not aware of IT security newsletter and i am interested in getting it. CaTS does good in
terms of service, but i guess can improve in providing partnerships with manufactures.
•
Keeping the network on lab computers working well. Having the ability to wipe a computer
when you log off. The ability to download office to my laptop.
•
The Help desk is always very well helpful when I call. My support through CaTS in Banner
keeps my database up to date by a daily feed. The support for Touchnet- MarketPlace and
Upay is instrumental in accomplishing our sales.
•
Notification of outages or issues
•
Help desk services
•
Home base/fix-it operations. Helping with account issues.
•
Great service and people!
•
CaTS does a fantastic job responding to issues in the classrooms. Hopefully, with the budget
crisis, this rapid response will not be removed.

34
•
The variety of knowledge is so helpful
•
I appreciate the knowledge, professionalism, ability to problem solve, and patience when
educating me about an issue or question whenever I call the CaTS help desk. I also appreciate
the assistance I've received when my office computer was evaluated for initial problems when
I was first hired.
•
The email services for Alumni work very well, it's a great service to have.
•
Help Desk
•
Helping with classroom computing problems quickly. This is very important.
•
Helping with "operator error" issues.
•
Responsiveness to faculty requestsshould
•
Computer help.
•
All the specialized personnel is excellent.
•
I've been assisted numerous times over the phone which has been very helpful. The times
someone has had to come to my office the problem is usually bigger but they have always
been able to fix it.
•
servicing wifi outages
•
CATS, STAC, and ERC Media Center personnel are amazing!!! Helpful, friendly, and patient
with this old student. Thank you to all of them.
•
laptops need to be run faster in computer lab 026 in basement of dunbar. it takes too long to
get on to home screen.
•
Helpdesk service is stellar!
•
As a retiree my schedule is flexible enough that service interruptions are not an issue, though
I appreciate receiving notice of scheduled ones. My main reason for calling CaTS is access
issues--password problems, etc. These are usually resolved quickly without complication.
Staff is well informed and resourceful.
•
Service is always great with CaTS employees. In general, everyone is helpful, polite, and
friendly.
•
Computer support
•
Help desk staff are great, very professional and helpful. I can only say good things about
them.
•
I have worked at WSU for almost 15 years and seen many technology fads/phases come &
go, but the level of service and commitment to customer service continues to be an asset to

35
our institution. No, not any venture is perfect, but I believe the folks at CaTS always do their
best to mitigate situations as quickly as possible while offering nuggets of wisdom for free!
Your organization is one of the few constants I can depend on here supporting the entire
enterprise with excellence and a smile.
•
Resolving any technical issues associated with WSU Applications.
•
CaTs always addresses issues swiftly. Most of my issues are for Xerox. They always call back
and sometimes can find the problem remotely. Kudos to everyone for their knowledge and
awesome customer service.
•
I received assistance over the phone which was huge because I didn't have to drive 40 miles
to have my issue fixed… I am so thankful that the IT team is wise and helpful over the phone!
•
Folks are prompt, helpful and resolve issues. Thanks!
•
Problem solving
•
Larry has been a great help this year.
•
Help desk (any chance of working with the university to develop a common help system like
the Help Desk beyond technical help and needs(not make the IT staff manage non IT support
issues but utilize the trouble ticket system across the university for all needs.) Perhaps
provide live chat support for IT as well as for other needs by users across campus(again, have
this for IT but use a common help system for other student, staff, faculty and facility needs...)
•
Troubleshooting, they have been very helpful. As a new employee they have helped with set
up and issues with software.
•
The CTL classes offered are good
•
Assistance by phone
•
The only interaction I have with CaTS is when something goes wrong. They are able to solve
the problems most of the time, but not always.
•
Desktop help
•
Provide fast service
•
Almost everything!!
•
My experience is limited to HelpDesk and setting up computers and computer accounts, and I
think CaTS does these things well.
•
The Help Desk is very valuable resource. Quick service, good information, and very patient
and kind.
•
I feel you always answer my questions/resolve my problems in a timely manner.

36
•
Don't still do much with it, but it's nice to have.
•
Over the phone troubleshooting is excellent.
•
Find CaTs very responsive.
•
CaTS is wonderful . . I had an issue with my login and called CaTS and they were extremely
efficient and we got my problem fixed right away.
•
Classroom Equipment, software programs, SPSS, and providing space for exams. It is hard to
single out, since I have never had any problems with requests. I would just say that they are
excellent at what they do. I look forward to using any new services offered.
•
Assistance with equipment set-up Assistance with computer/technical problems Answering
software inquiries
•
Good customer service. Prompt responses to problems
•
The service from both the students and the staff is great. Everyone is extremely helpful and
supportive. When calling in with a problem, the person at CaTS works to find an answer or
get you to the correct person. I never feel like I am a burden to them when I call.
•
Service for office computers is always fast, efficient, and very courteous. I've never been
disappointed.
•
Maintaining technical equipment, fixing technological issues when necessary, being available
for faculty and students to access, and timeliness in fulfilling requests or issues.
•
I think that CaTS performs well on all activities and services.
•
I am a retired staff member so I don't use Cats services as often as before, but I have been
very pleased with their services whenever needed. I am very pleased that I've been able to
continue with my account after retiring.
•
Best department on campus. Efficient,competent ,ready to help,friendly
•
I like their knowledge of computers, and their helpfulness to students/staff who need it.
•
I have had no issues with my account this past year. therefore i rated your supported as
satisfied.
•
Help Desk is superb!
•
I really appreciate the assistance with troubleshooting via tapping into my system remotely. I
also love that you'll assist me with my cell phone questions. Your techs are knowledgeable
and friendly -- I'm not afraid to call and let you what not so smart thing I just accepted onto
my computer. (I'm working on paying more attention to what I download -- I've only done it a
few times, but...)

37
•
When I have a technology problem, I can go to CATS and they always help me.
•
They perform well in all.
•
I believe that WSU's CaTS Team is WSU's conduit. Without the ongoing efforts of each CaTS
team member--and I am learning that each team serves a special & unique professional role--
WSU could not operate on a day-to-day basis. Also, WSU could not offer regularly upgraded
classroom resources relevant to 21st Century student learning. There is NO OFFICE ON
CAMPUS that does not rely on CaTS: I am continually impressed by the innovative & adaptive
spirit of each person I've had the pleasure to meet.
•
Resolving issues
•
Desktop support (very quick response time and very effective solving problems and issues)
•
I have never personally needed CaTS assistance, but when help is needed in the classroom
they come to the class quickly, and fix the problem in minutes.
•
As a retiree, my interaction with CaTS is mainly the help desk on the rare occasions I have
questions about email services. I recently interacted with Jeff Bowman about my account and
received very timely response and useful advice about my questions.
•
I mostly only interact with CaTS if I need my wright.edu password reset but I seldom have
difficulty
•
They answer right away and are able to take you step by step on how to fix your problem!
•
Helpdesk assistance! If they cannot figure it out in the 5-10 minute phone call, they will call
you back with the solution w/i a couple hours.
•
I appreciate the job done by the help desk. When you have a problem they can immediately
get on your computer and fix that problem. That part certainly helps from having downtuime
waiting for someone to come to your office.
•
very responsive to my needs when I have computer problems or need help with a software
program.
•
Providing us with wi-fi, fixing problems, doing computer scans/fixing personal laptop
problems in the home base.
•
Service/Help desk is great. They are always friendly, and always can either find a solution or
connect me with someone who can find a solution.
•
Excellent at responding to helpdesk issues: quick, knowledgeable, and willing to think outside
the box. Good on you!!!
•
Tech Support: Always patient and responsive to questions. Makes sure that when a problem
is fixed, it truly is resolved so as not to reoccur when the tech leaves or signs off. Spends as
much time as needed to address the issue. Willing to search or ask other tech staff when the

38
answer is not readily apparent. Installation: keeps appointments, prompt, helpful Hopefully
the budget cuts will not impact the service level or wait time for the help desk.
•
CaTS is awesome when responding to requests for help re. desktop issues. Having remote
access to our work computers saves time. Also, CaTS staff has been extremely helpful during
my transition to teaching in an IVDL room. I learned how to operate controls one day during
summer, and staff was present on my first day of class to help assure things went smoothly.
They also have shown up a couple of times to follow up on how this technology is working,
and to obtain feedback from students and me.
•
In my experience, the general computer lab computers have worked well enough that I never
consider it a gamble to use them.
•
Security and maintenance.
•
hi, nice service providing. good work. hard working. Polite staff . I went so many times to
CATS.
•
I have always been satisfied with new computer installations, re-imaging, trouble shooting.
CaTs staff also manages one of our servers and assists us with software. I have also received
good customer support if I have a questions I don't understand (from both the help desk and
technicians)
•
I am teaching and IVDL class. The gentlemen who have been helping me were outstanding!!
•
electronics lost and found in the basement computer labs
•
quick response when issues in classroom, Quick help at help desk.
•
I never have been dissatisfied as a faculty member with CaTS.
•
Assisting in the classroom! You get priority if you phone from a classroom, or if there's a
classroom issue which needs to be addressed!
•
My main direct experience is with the Help Desk. I have received helpful service from them.
•
Home base Atomic Learning
•
The Help desk (over the phone, remote access) is extremely helpful for addressing urgent
issues.
•
I like that CaTS has laptops to go and that the Home Base is able to diagnose student devices.
•
Very helpful in helping to resolve personal computer issues.
•
The training that is offered is fine and generally works well.
•
Quick response to report and appworx change requests.

39
•
The IT department area in opinion, outstanding. Thanks
•
I feel as if the help desk does an exceptional job. I am very appreciative of their work. Thank
you!
•
My login expired and I needed help getting my password reset. Via phone I received accurate
and helpful advice and my password was reset. I also received guidance for extending my
alumni activation. After I submitted my activation request form, I received a phone call stating
that the process was complete. I am very satisfied with the assistance I received and I wish all
technical help was as good as the help from cats.
•
Thank you for helping with my issue over the phone (as I do not live close to campus!)
•
They are very quick at responding to problems with Wright State computers.
•
Service for software, hardware, and trouble shooting.
•
Desktop support and customer service are fantastic. All staff are incredibly knowledgeable.
The infrastructure on campus is completely invisible - which means they have to be doing an
amazing job.
•
Virus scans/computer checkups
•
I have only called CaTS once or twice. Both times the phone was answered quickly and the
technician was polite and helpful. One time my issue was resolved and the other time it was
not because the problem was the result of a system-wide Pilot Live Ultra failure. It was
resolved soon by the server host.
•
You are very helpful when I call for outstanding questions. You also communicate well via
email, and have a well designed Wings Express page.
•
Providing support when I have trouble. It has always been patient and helpful
•
I do not feel I utilize them enough to give feedback here. But when I have used them they
were very knowledgeable and welcoming.
•
classroom assistance office computer troubleshooting software update instruction
•
Response to classroom problems is phenominal!
•
I think CaTS generally does a good job with every service they provide.
•
The technicians are always helpful when I call.
•
Frank is amazing. I was having issues with an old piece of equipment my professor wanted to
use. I specifically requested Frank since he has worked with the equipment before (and when
I have not specified in the past, the person that came had to call Frank). As always, quick,
efficient, cordial!!! Made me look good for my professor, lol.

40
•
CaTS provides a top notch help desk. CaTS also provides a wide range of applications and
other technologies to empower the classroom. WSU is fortunate to have such an extensive
portfolio of technologies and services provided by CaTS.
•
When I call the help desk, I rarely need to wait for service. Typically, I am only on the phone a
few minutes before I am able to speak with a technician and when I do talk with them, they
are often friendly and helpful.
•
Our internet access is outstanding; wired and wireless. Thank you for maintaining quick
speeds and near perfect connections. Guest accounts are critical to provide full library service.
I appreciate you maintaining these accounts for us.
•
I have been very impressed with the level and timeliness of support compared to previous
workplaces.
•
Very customer service oriented and explains things in a clear way without making me feel like
a computer-illiterate person.
•
When I was a PC user I constantly needed CaTS to de-bug my computer for me. Now that I
have a MacBook I needed CaTS to install Microsoft Office for me and they did that. Anytime I
call, tweet, or stop in with an issue they are quick to act and solve the issue. I am not kidding
when I say this, if it weren't for the helpful young men at CaTS, I would have dropped out of
college already.
•
Whoever answers the help desk is a GIFT! As sometimes I can't articulate IT problems but
they probablem solve it EVERY time and with patience!
•
Very responsive. Customer friendly. WSU has an awesome IT team. Thanks!
•
Timeliness
•
LOVE the free laptop assistance!! My laptop froze up last fall, and I was afraid it was dying the
same death as my last one, but CaTS fixed it for me!! I had it back, good as new (a little
better, actually) within 48 hours!
•
they respond very quickly
•
I feel like CATS is performing very well in all aspects of the university needs that has been
tasked with. I Have been especially impressed with CATS and it's leadership and
responsiveness under Dr. Woolley's tenure.
•
Help desk techs are professional and knowledgeable. They provide excellent customer
service. I also appreciate services to help me log into VPN at home and get software programs
to use for work, ex, Word and PowerPoint
•
Everything

41
•
After purchasing a new laptop, they were tremendous help with the initial set up and
recommended applications needed for medical school.
•
Great support for a retired professor.
•
Warning students of scams, helping students with computer repairs
•
Installed a new hard drive on computer. They did well with that.
•
I have taken my personal computer in before when I've had problems, and everyone has been
very friendly and efficient
•
I appreciate the help they have given me to coordinate my phone and computer.
•
When I called CaTS, they gave me the info I needed. They were friendly and helpful in a timely
manner.
•
1) They never make fun of me when I have a problem that is easily corrected. By them. 2)
They always respond super quickly to an SOS called in from a classroom. 3) They have been
super-helpful regarding my new (last year) laptop. Robert in particular returned again and
again to straighten things out, and was very pleasant to work with! 4) Love the Home Base
thing - I can do it, they can help.
•
Helping with computer problems.
•
The Help Desk has always been very responsive when I call with a question.
•
The Home Base is amazing! They are always so helpful! Ben has been helpful to me on
multiple occasions with my laptop.
•
Nice. Polite. Responsive. Help desk.
•
As IT experts, CaTS fills this role very well.
•
All my interactions and tickets have received very timely support. I have had interactions at
different levels in CaTS-- all have been very responsive. Keep up!
•
Outstanding response to class room problems and very rapidly. Excellent response on
computer problems.
•
They do repair technology actually really well and in a timely fashion. And the notifications
aren't too much. I've worked with them closely because my laptop has needed many repairs.
•
Very good customer service, communication, and timeliness of answering requests/questions
•
Troubleshooting and support for software packages and applications.
•
I like about the service they provide for the computers, They fix it well even before we know
there was an issue with it

42
•
fix system downs in timely manner
•
Responding to questions/HelpDesk tickets, providing web site materials, project support.
•
Help desk reps are always knowledgeable and courteous. I really appreciate them being there,
even after hours!
•
Typically a quick response to my issues
•
I find the students at the Help Desk very helpful and very professional.
•
Help Desk is awesome.
•
Staff is extremely helpful and prompt.
•
Very responsive to requests for service
•
Working with functional constituents to fulfill Banner requests.
•
People on phone calls are very helpful, polite and usually solve our problems.
•
Help Desk--I've always gotten very good help in a timely manner when calling the Help Desk
•
every time that I have called the CATS helpdesk, the people are always very professional and I
get my issue resolved very quickly.
•
Typically fixing internet issues is very fast, and other services provided by home base are
great!
•
I called to ask about removing deepfreeze from some computers in our lab, and the techs
were polite, swift, and professional.
•
Help desk service is quick, well communicated and resolves most issues the first time.
•
HelpDesk--I always receive courteous assistance. If the staff member answering the phone
can't fix the issue, s/he routes the call to someone who can. Server Support--this group (John
Meyers and Rich Hadden in particular) are exceedingly helpful and go above and beyond to
assist when needed.
•
People have always given me accurate advice, great customer service and I really appreciate
that.
•
They are very responsive and helpful - with product recommendations and providing as much
help as possible. I think they are the easiest service line to work with on campus.
•
CATS always contacts the students to tell us that there's a problem and is always immediately
fixing the problem after it's issued.
•
I think it would be helpful to better gauge the length of the workshops, when they go half an
hour over it seems rude to leave early, but other appointments have to be attended as well.

43
•
From the desktop services to technicians coming out to serve on-site, I have had nothing but
the best experiences with the staff in CaTS. You consistently provide excellent service and
advise at a reasonable response pace and it is greatly appreciated.
•
Good communications with students regarding wifi and downtimes.
•
Responding to questions and fixing a problem when I call. I have been very pleased.
•
There are several, most people do not know all of the services that CaTS provide or help to
deliver.
•
I find the website fairly well organized and easy to use.
•
Enjoyed the training at Staff Development Day
•
It seems that calls to the help desk yield quicker results than at some times in the past.
Always helpful, always friendly service from the help desk and from in person visits from
technicians.
•
Being available to come out to an offsite location to fix computer problems.
•
Quick response time Very knowledgeable
•
You guys keep the wifi up and running, and have greatly improved over the past few years.
•
Their staff is very helpful and knowledgeable and if there are ways they can help you improve
on a class listing in Pilot they will assist.
•
Timely response to emergency IT issues
•
Assistance with regards to understanding issues and tech solutions
•
OMG GIVE CHRIS, CHRIS and BRYAN a raise....they are awesome folks....can't live without
them!!!
•
The new ticketing system is great. A++
•
troubleshooting
•
I always receive excellent and expeditious help when calling the Help desk. In the 8 years I
have worked here, I have never had a complaint towards the CaTS Help desk or for that
matter, any CaTS employees.
•
CaTS always has friendly, patient staff/students. (I don't know how you do it, but keep it up!)
•
They are responsive whenever we call.
•
All interaction that I have had with CaTS has been wonderful.
•
Friendly on the phone. Walking me through a problem

44
•
Those CaTS employees who are helpful are extremely helpful and quite patient. Providing
customer service is not an easy task and those who do it well there do it VERY well.
•
Help Desk with Bomgar gets straight to the challenge/point.
•
I am very appreciative of the staff's very timely response to requests. I am very appreciative
of the knowledge and expertise various CAT representatives (Josh, Robert, Jeff and others)
exhibit. They know their product(s), they know their area(s) of service--if they don't, they will
direct you to a live "person" -- not place you on hold or send you to a line and it is busy. They
make sure that you speak with someone. All my experiences with CaTS/personnel has been
great! Thank you!
•
I feel that the CaTS staff are very helpful in resolving large and small IT issues. They also help
to understand what was done, and make themselves available for any other issues that may
arise. I also like that they allow troubleshooting on home computers/laptops. Very helpful.
•
I've called a few times and everyone is very friendly, helpful and timely.
•
Answering the phone!!!! With a real person!!!! giving great answers to routine questions, very
promptly!
•
Everything. Every time I need help, the response is quick and helpful. Everyone seems very
knowledgeable; however, if they are not sure, they find someone who can help and they
respond in a very timely manner.
•
great help desk staff
•
Helping me walk through a process that I don't understand.
•
Excellent service, in my experience they easily "diagnose" what the problem is and often fix it
quickly.
•
The help desk is typically prompt. They're quick to use the remote desktop app to "see"
what's happening on our computers.
•
Help with software installation and function. Effective helping with log/in and password
problems.
•
Help desk does a great job.
•
CATS has transformed from a hindrance to a help.
•
Service from help desk and appointments for computer repairs are both excellent.
•
Phone consultation
•
Even though I have retired, CATS has responded quickly and professionally each time I have
had a problem.

45
•
-Notifications of connection problems -Phishing emails
•
They resolve my email issues very quickly when they occur.
•
As a new hire, I had lots of issues with unlocking my computer, new software, putting
filemaker on my phone with ASD. They were so fast to respond that I often onlt waited
minutes for a return call and/or visit. Very impressive.
•
When ever I have a problem I always feel comfortable calling CatS for help.
•
service... great service just a phone call away; love remote fixes or walking through an issue.
Ordered new laptop for department and CATS was great to work with, scheduled computer
formatting with tech (we are off-site from main campus too!) He came over and took care of
it. Great people who know there stuff!
•
Great initial triage of issues
•
they have always helped me through everything and explained why they did what they did.
•
They help to the best of their ability, and I appreciate that. Their work ethic is profoundly
acceptable and I dare say that it helps their prestige grow. I wouldn't expect any less than the
best, and they have given that.
•
Addressing individual issues. Every time I call or email, I receive prompt response and a
satisfactory resolution to my problem. Thank you!!!
•
Always quick to respond to computing issues (because, hey...how many of us can work
without their computer??). CaTS is a great resource to the university. The people are friendly
and knowledgeable.
•
connectivity is always fast and pretty much available all the time.
46
Please provide feedback on activities and services you feel CaTS could
improve (maximum of 500 characters):
•
More training opportunities
•
Room scheduling and communication between entities could be improved. (For example,
between CaTS and Registrar, Department that the computer lab is housed in, and so on. The
computer lab schedules have not always been accurate with who has reserved the room
when. Furthermore, labs have randomly closed early or opened late (and people have
noticed). CaTS could also improve document cameras, SmartMonitors, and other classroom
tech sooner (and more uniformly). Some rooms are good and some aren't.
•
Possibly train some of your staff to be less nosy. When someone is doing official business on a
school computer, you should not peek on their screen.
•
Better suggestions on off-campus problems.
•
Advertising at he beginning of the school year. I never know what is new/available until
halfway through the year, typically from interactions with students
•
Wi-Fi
•
I feel like wings and wings express could have a single sign on. Kind of ridiculous that we need
two separate username and passwords for the two websites.
•
Would be nice to have 24/7 support. Maybe after WSU fixes their debt problem.
•
Have someone on site at Ellis part-time to help with all our needs (ideal world).
•
Communication of service time could be more clear, but overall, I am appreciative.
•
With the time it takes to tell about the hours Cats is open, call for classroom equipment, etc.
you could have answered a couple of calls and fixed their problem. Please get rid of it or
shorten what whomever is saying. I don't care what your hours you are open as I am here
only during regular office hours.
•
Providing that product for sale to all alumni at those discounted rates/getting the word out
about available discounts
•
I think that (and I'm not sure if they are able to) CaTS could try and improve the connection
issues in residence life. Often, the connection is slow or devices won't connect at all,
specifically in 2050 of the Village. Maybe communicating to residents why things are the way
they are in their buildings would help them understand instead of them just complaining
about it. (I was an RA for 5 semesters, so that's why I'm aware of these issues)
•
Network uptime/ speed consistency (this does not mean bottleneck everyone)
•
Improve the wifi.
•
The wifi connection could connect faster and be more reliable. The wifi could also work better
and faster specifically in Hamilton lobby.
•
Less usernames and passwords, better user experience for things like class scheduling and
leave reporting

47
•
TIMELINESS: I developed an online survey in Feb. for Power of Nursing course directors to
complete from schools of nursing in US and Taiwan that offer the PON program. I have been
unable to send the survey via email because I'm still waiting for a "link" that needs to be
completed/developed/approved - not quite sure - by CaTS. It is now April and out of
frustration I embedded the survey questions into the body of an email and sent it out. No idea
how much longer I would need to wait.
•
A dedicated web page, or pages, listing all the services that CaTS offers for Alumni would be a
nice addition (or if it already exists, additional communication on where to find it).
•
Making changes without asking for advice from several SME's and without pre-notification.
•
IT Security Newsletter: while its a good idea, there are just too many emails flowing into my
mail box on a daily basis that I delete the newsletter without reading it. Not your fault, just
reality. Not sure how you can improve this either.
•
I have had 2 emergency situations arise that I needed help with and in neither case was CaTS
able to help or apparently concerned that they could not. One was a power supply issue
wherein I needed to borrow one to get through my class, and I would have expected that
given a reasonable set of 'standard' equipment that you'd have had one. Second, and it was
my fault, that I left my computer at home and really needed to borrow one You have
machines to loan students, but not instructors.
•
The campus could use a designated "No Talking" computing lab. There are "quiet spaces" on
campus, but quiet is very subjective and open to interpretation of "quiet talking" where "no
talking" spells it out.
•
Multiple training times of workshops. Often they are offered when I teach class.
•
Help desk is most of the times very helpful. Only occasionally, I have had people that needed
more training. So, the recommendation is to train them well. Or check for their training
periodically.
•
I do not like the Office 365 Outlook mail program which seems clearly intended for business
applications and careates a lot of needless comlexity and clutter. It is not very intuitive even
if your main interest is simply sending emails. The calender has similar problems. I have
wasted a lot of time using both programs.
•
Maybe a bit more support for us Mac users at BSOM, but we know that's a challenge!
•
Not sure if CaTS is in charge of this or not, but the timing of the updates on our computers
sometimes is a little frustrating. Last Friday afternoon, I went to turn off the computer only to
get the dreaded message: "Updates being installed, please do not turn off the computer 1 of
15 updates"... After 10 minutes, I was a little frustrated as I had skipped lunch to leave a little
early. The selection of computers to purchase is limited. I thought we would have more
varieties to choose from.
•
Time taken to merge duplicate records can be improved, as it affects the business process.
•
Training
•
Better notification to the campus community regarding Phishing Scams
•
Working with departments to use technology to improve efficiency, especially now that
budgets are tight.

48
•
I attended a Powerpoint class last week and it did not cover the topics I thought it would. It
was only 40 minutes long and just covered the philosophy behind why you shouldn't put too
much on one slide. Very disappointing.
•
My only complaint is the very long message you have to listen to in order to get help. Most
people call the helpdesk to get help. Should be the first option that I can push a button for.
•
Wait times on hold
•
A lot of people do not know about all the services that are offered. I do not know how you
can expand on your marketing of services but the word does need to be spread.
•
Wifi service
•
Hire some more female employees.
•
The hotline often has long waits. There should be a system for leaving messages or callbacks.
•
Right now the services are good.
•
Send Broadcast messages or campus wide notification when there are Banner or Internet
issues.
•
Update instructions for getting campus email to work with Outlook 2016.
•
Just about any time I need my university ID for anything, I end up needing a reset; it may be
easier for current students, but I always have trouble with those systems.
•
additional training sessions
•
Computers in labs take such a long time to log in and the browser takes a while to load as
well, also I wish they had their own set of basic computer supplies on sale at a student price ;)
(I know they have flash drives but I don't know about others...)
•
Website could do with a bit of cleaning. With the Office 365 stuff under "services", even the
'what is this and how do I use it', and not under "training", I didn't even know it was there!
Have all "how to" stuff under training. Easier to find.
•
Your website has improved and has more offerings on self training that I was not aware of.
Perhaps a "Did you know" campaign to alert the campus community to what's out there.
Offer a "best habits" instruction sheet for new employees and current employees as to what
measures to take to keep systems running optimally (especially since current budgets will
mean equipment is utilized longer). Instructions on backing up work files (what is the H drive
and how to utilize it).
•
If CaTS could send 1-2 staff to notable educational technology conferences, staff could better
assist faculty on projects that involve emerging and existing technologies that enhance
instruction domestically and abroad. We need to actively think about and discuss how we
may support working adults so they may return to university to complete a degree.
•
Adding more services as tech increases. Offer training workshops to alumni on new programs.
•
NICE WORK
•
I don't know if this involves CATS but printing costs more than I would like.

49
•
Students tell me that many times when they call the help desk that the person is unable to
help them with the issue and refers the student back to the faculty member who sent the
student to the help desk.
•
I asked a CaTS technician once about why Office365 email locks student Access files and
blocks any future usage. He said if it happens again, please let him know so that he could look
into it. The next time it happened, I called the help desk, eager to get a note to that person.
The lady who answered the call had her own solution: tell the student to save the file to a
flashdrive. I guess it was good advice, but it wasn't the question which I asked, nor did it help
to resolve this issue.
•
Better communication of services you offer and things we should be aware of pertaining to
online security in our daily work.
•
Home base: provide more options and support.
•
Perhaps make students more aware of the free software licenses available through CaTS.
•
Training that moves beyond just technical how to but into how should I? For example, if
Skype for Business is available as a collaboration tool for working with students, especially in
instances where a student can't attend class due to illness but could connect via Skype, how
should professors set that up and leverage the resource in the classroom?
•
You can not improve perfect.
•
I do not like, nor have I ever liked, Office 365 email.
•
There have been several occasions when computers in the 24 hour computer lab near the
CATS help desk do not work and have a black screen with a small box in the center with
something cloud. It would be nice to not have to worry if the computers will work in the
computer lab.
•
Training has been decreased as users' abilities increase. It would be great to have a training
with exercises that users can work through, assessing for gaps in knowledge, with a
facilitator(s) who can assist/explain as needed.
•
A single point of contact from CaTS (the entire division, a holistic CaTS Project Manager) on
construction projects would be a godsend for FMS Administration.
•
Lift the password character limit. It's ironic having an IT security newsletter come out about
good password practices when we're limited to 14 characters. That's more pathetic than
Microsoft's 16 characters.
•
I have not had any problems with CaTS, but would like them to let Alumni know when their 5
years after college is up, and how to pay to keep their emails.
•
Making sure classroom technology is working, although I haven't had many breakdowns.
•
Did not know there was a monthly IT newsletter...
•
Windows 10 Deployment. Office 365 integration into the desktop user experience. Mobile
integration and BYOD not clear. Lack of clarity for users on a variety of processes such as
initial account setup and login since there are a variety of usernames and passwords.
•
Cost of doing a job
•
I personally have no qualms about CaTS. They've exceeded my expectations each time I've
needed their assistance.

50
•
Improve the reliability of the wifi on campus.
•
Explaining what was wrong
•
There is a certain irony that the "internet connectivity issues" alerts come out via the wright
state email accounts...which of course can't be accessed on campus when the internet is
down. I'm not sure what I would suggest instead, but it seems a little pointless to use the
downed service to tell people the service is down.
•
They are getting better at helping staff who have Macs! I used to feel like a redheaded step
child when I called. People seem to be getting more training!! Yes!! Go CaTS! I really don't
have any complaints!
•
being more customer friendly
•
Timeliness in their response and overall number of internet or application outages are what I
see as the two biggest areas for improvement.
•
Quality and timeliness of connection to WSU secure wifi
•
Wifi cuts in and out sometimes
•
Providing service for Apple computers!!
•
Professional demeanor of students managing helpdesk
•
Hardware purchase (esp PC) is not up to date at times, and is not competitive with what we
can buy on open market.
•
On exam nights, it would help if you were open until 1/2 hour after the exams so they could
be dropped off for Scanning Services and have assistance available for class room problems.
•
I guess just clarity within ordering parts for the technology they fix. I've bought the wrong
piece before because of a miscommunication, but that's a rare mistake with CATS.
•
If possible, an increased level of knowledge that the techs have for dealing with a wider array
of IT problems would be helpful.
•
Users have a hard time knowing when to submit a Banner Admin access application --
because it appears first in the alphabetical list, they often don't make it down to the correct
WINGS Express Finance access form.
•
Helping departments develop and implement a computer/technology replacement
policy/cycle.
•
I'm not sure the Help Desk knows who in Cats to call when there is a Wings Express Finance
issue.
•
The internet issues starting during March have not seen to been resolved
•
I did not know there was an IT security newsletter, so maybe advertise that more effectively.
•
Residential Wi-Fi speed depending on the demand. It's frustrating when taking an online
exam, which is timed, the pages take a long time to load.
•
Like all areas of the university, there seem to be too many projects and too few staff in CaTS.
We've literally waited years for some projects to be implemented.

51
•
The long wait time to get to a representative.
•
publicize programs that you support. I was only aware of one out of three. I am a commuter
and only attend night time classes.
•
I would like more support for Mac users.
•
Need more software training in computer labs instead of lecture-style
•
Sometimes response to issues in the classroom could be faster or handled better.
•
Very helpful getting a Video for the class into Pilot
•
CRM and Marketing Cloud improvements and implementation could improve. E-forms and
parental signatures would relieve EMD workloads tremendously but we can't get movement
forward on these.
•
Timeliness in scheduling support visits.
•
Provide service to Macs at the same level as PCs. CaTS techs seem to be learning how to
troubleshoot problems on Macs.
•
The only improvement I would make would allow customers the ability to skip through the
call automation and be placed directly in the queue.
•
That said, there is a wide disparity between those CaTS employees who are very good at
customer service and those who are not. I have found that I am helped 100% or poorly with
very little in between. Consistent training helps (I used to work in customer service and I was
a trainer; trust me on this please!). Also, this is going to sound harsh; fire those who are
incompetent! Use "mystery shoppers" with questions to help weed out your incompetent
staff.
•
CaTS provide professional, friendly and courteous service -- that's all I have ever experienced.
•
I have a laptop that CATS set up for me 2.5 yrs ago. Now no one knows what sort of internet
connection utility the guy put on, and can not help me with it!
•
The wi-fi and network is always slow at the Lake Campus. This needs attention. I don't rely
on CATS at the Lake for much else.
•
Your agents need further training on Mac computers and software.
•
The printers are always giving me problems. The Cisco connect no longer works. The PILOT
software gives faculty in my department issues with grade calculation and ruined the
collection Faculty and TA evaluations for one of my courses.
•
So far this year, i live in the woods on campus, every day from around 6-9 pm the wifi spikes
to around 170 ping, but it is only for those hours, every other time of the day it has been fine,
I just dont know why it is those hours, it is very inconvenient.
•
Only thing that sometimes gets in the way is the length of time either on hold or when they
take over the computer.
•
I work with AFRL extensively. I strongly recommend that any room likely to be used for guest
electronic projection MUST have the option of an HDMI or at least vga wired connection.
•
E-mails are generally poorly written, but communicate what we need to know. The phishing
e-mails are probably useful for people who don't understand e-mail, but for most of us
they're just clutter.

52
•
I understand the logistics of it, but I am not sure why you cannot send people to the Lake
Campus more often to get things completed. Waiting until you have an entire list of things to
work on at the Lake Campus sometimes could hold projects up.
•
Sometimes the student employees in the office aren't as helpful as they could be. It could be
lack of expertise or not feeling too motivated.
•
The Service Now Requests are not addressed in a timely manner. I currently have 17 in the
queue...most from back in January...and none have been addressed...nor have any I put in
during 2016 when an emailed spreadsheet was the avenue for change.
•
Training of Window 10 computers and how to properly sync them with the network so users
can access their H, K and R drives

53
Please provide any additional comments (maximum of 500
characters)
•
Appreciate the help they have given me.
•
Overall, CaTS is doing a great job! Keep up the good work! Thanks! Shout out to Paul
Downing, Craig Wooley, Jerry Hensley, Ken Nelson, Reid Allen, JJ, Larry Fox, Michael Rauch,
David Stoneburner, Brian Daniels, the HelpDesk staff, and all the CTL folks for their hard work
and help!
•
I am based at Miami Valley Hospital, not main WSU campus. Every time I've reached out to
CATS personnel they've been absolutely helpful! Never any excuses; always able to resolve
the issues. Help Desk personnel are always attentive to the customer! Our department had
an Outlook address issue for a faculty member(it's my job to provide the faculty admin
support). The help in this particular situation was excellent, most notably the assistance and
liaison efforts of Jeff Bowman.
•
Excellent resource for unpredictable problems.
•
The man I spoke to when I started was very patient and polite. Thank you!
•
Overall, I'm pleased with services received from CaTS.
•
I feel confident that my issue will be resolved when I bring laptop to CATS.
•
I wish you would let me still go directly to the MS site directly for email. Having to go through
the wings site first is a real pain! I'm not sure why this change was done but please allow
direct access to the web mail in the future..
•
Thanks for the emails of phishing scams and all the services! I would also promote the free
Microsoft word because I know that many people are unaware of this and how to obtain it.
•
All in all, I think Cats does a good job. They have always helped me and fixed whatever
problem I was having.
•
The clutter box is causing several issues for me sending very important emails to the clutter
that I may not see.
•
Not trying to be mean, but the wifi isn't good here. Why, I do not know. But we pay too much
money for the wifi to be this bad.
•
I have noticed great overall improvements in CaTS over the past few years.
•
Keep up the great service!
•
I was very dissatisfied about the update of the cable services on campus. We were not
notified that this was going to affect our signals depending on what type of TV we own. Also
some of the main channels were taken away, such as FOX and VH1. Also when I reached out
to CATS to figure out why my TV was not working and was there anything I could do to fix it I
did not get a response until almost 10 days later. This is one of the reasons why I will not be
staying on campus next school year.
•
I am satisfied with the support I receive.
•
Y'all are seriously life savers and I love you all.
•
I would value being able to bring in a computer from home for service and updates...........

54
•
CaTS is extremely supportive of all instructional faculty. Thank you... Please keep up the
excellent support of the classrooms and the faculty who are using them.
•
Thank you for reaching out to customers regarding service. I have noticed the wheels of
change move slowly in this large organization. I started my role December 12th and my
computer was not set-up until January 4th which hampered my ability to get started. I did use
my own laptop until my computer was up and running.
•
The folks from CATS are always friendly, knowledgable, and helpful.
•
I seriously disagree with the current policy of IR demanding that they know the reason why I
am requesting data. I should be able to ask for data and analyze it without having to justify to
them what I am thinking about
•
Please designate a "no talking" computing lab. This would benefit those with English as a
second language as well as others with a learning disability or simply study better when there
are no conversations (talking) going on around them.
•
Too bad we are losing Jason. What a blessing he has been to your department.
•
I don't like -- and have never liked -- Office 365 email.
•
Please improve the wifi. Sometimes it works great other times it's super slow
•
Thank you, CaTS
•
Needless to say, the Office email and calendar programs available to users share the design
deficiencies of most programs these days. I refer to the use of light gray and colored type
that contrasts poorly with the background colors used and are often very difficult for the
visually handicapped to read. Even worse are the virtually invisible lines or boxes meant for
users to fill with email addresses or passwords. It is high time the industry got off its kick of
over-designing Web sites
•
I know that there are going to be a lot of changes in CaTS and the university as a whole, but I
hope that the CIO and the directors of CaTS will be able to rally around the remaining CaTS
staff and find ways to bolster morale and encourage those who are carrying the workload to
maintain the excellent service the department has always provided.
•
I like that CaTS is willing to look at home computers for viruses. Not being an IT person and
having no one else to check for me, this is going to very valuable to me. I intend to use it!
•
CATS people are fantastic! Invaluable! Knowledgeable, fast, reliable, patient, courteous -one
of the best services (or THE best service) on campus!
•
I am very impressed with CaTS, and it's really gotten even better under the new management.
•
GREAT JOB, CaTs!
•
thank you for all you do!
•
Any chance of working with the university to develop a common help system like the Help
Desk beyond technical help and needs (not make the IT staff manage non IT support issues
but utilize the Help Desk/trouble ticket system across the university for all needs.) Perhaps
provide live chat support for IT as well as for other needs by users across campus(again, have
this for IT but use a common help system for other student, staff, faculty and facility needs...)
•
Xerox printers...I know this has nothing to do with CaTS, but I will let you know the machines
are a pain. The service we have received from CaTS on the issues with the printers has been
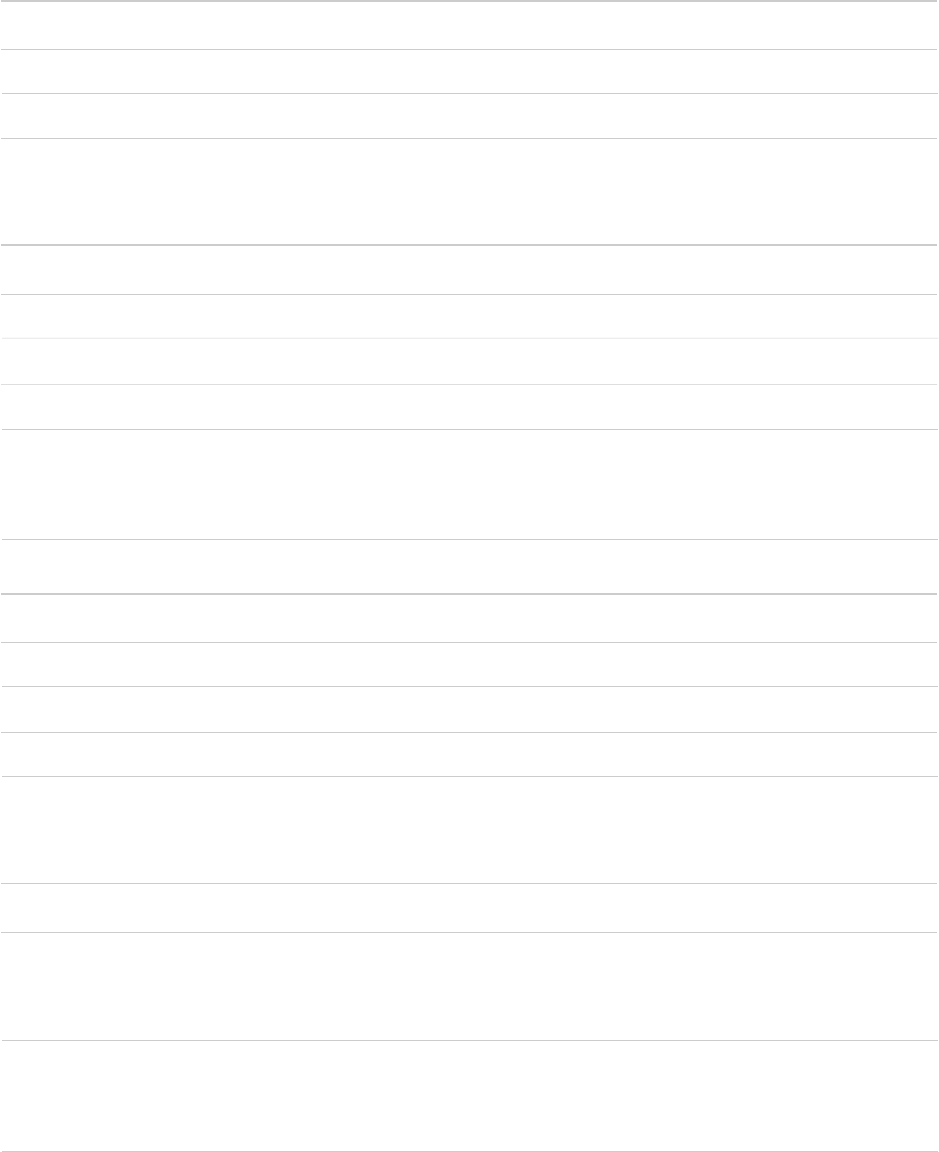
55
exceptional, unlike the service we have received from Xerox themselves. Their service people
are condescending and rude, where CaTS is helpful and understanding.
•
CaTS is terrific
•
Best IT support of any company I've ever worked at
•
Thank you for availability and knowledge.
•
I hope that none of the staff will be cut during the budget crisis. Turnover is hard for every
department but when a CaTS person leave, they take so much information and history with
them that it is like starting all over if you have to explain all the history to a new person. SAVE
THE JOBS.
•
Well done.
•
I appreciate the service I have personally received in the past 30 years.
•
They were very helpful!!
•
thank you
•
Also, what is this IT newsletter you speak of? Ah-you said it was monthly so I probably do read
it and didn't realize it was a monthly newsletter. Maybe put all resources in the newsletter
every now and then provided to students...oh! and all phone apps students should find
valuable on campus. Thanks!
•
Your department is very well run, offers the highest level of professionalism and customer
support, and is an asset to the university. Thanks for your support
•
Thank you for your support.
•
GOOD WORK
•
Keep up the great work and thanks for all you do
•
I have no idea what this stuff is about to be honest. Sorry my feedback wasn't more helpful.
•
Camtasia for PC is available but not for Macs. I only work on Macs but had to purchase my
own copy. This means I can't have Camtasia on all my machines that I use for work (some are
university provided and some are my own devices). However, I use Camtasia regularly for my
research and my teaching.
•
Wonderful
•
In many ways our systems seem very backward. For example, colleagues at other universities
have voice mail to email. I should be able to work from home, where I have a more powerful
computer, but I can't and it doesn't make sense. The current work around seems much more
wasteful.
•
This department has always been highly beneficial in providing basic assistance and individual
trouble shooting. I really could not function as well without being able to call for assistance
when needed from classrooms, borrow equipment when needed for classes or meetings, and
having someone log in to assist with glitches. Thank you!
•
I am very happy with keeping my email through Wright State University after college. I check
it everyday, and use it as my professional email account.

56
•
CaTS personnel are really reliable, friendly, and helpful!
•
Thanks for all CaTS personnel for the excellent job they do.
•
Great job!
•
CaTS is doing a very good job of being available when there is a problem. It feels like there is
not a lot of innovation taking place, and it is primarily keeping the status quo functioning.
•
Please keep CaTS!!!!!!!!
•
The partnership and service from CaTS has been terrific. We needed a phone line option for
our training room and for it to be installed quickly and they responded. The team has been
helpful in the development of Service Now for our future use and we always appreciate the
support at Open Enrollment.
•
We depend on you. CaTS delivers. Thank you.
•
Safe website, filers out all the annoying spam; and I am very pleased with CaTS.
•
I just use the e-mail that is provided as an alumni. I have yet to have any major problems with
the service. It always works well, thank you.
•
Thanks folks! What would I do without you?
•
Thanks for what you do for WSU
•
It would be great if CaTS can include OpenStack support as part of high performance
computing service/support.
•
Keep up the good work. CATS is one of the few great services offered to faculty by WSU.
•
I'm grateful for the service in general. It's comforting to know that I have that service due to
my bad luck with the technology.
•
thank you - I enjoy working with our various cats folks :)
•
The "Directories" search at the top of the WSU homepage is awful!!! If you spell the name
wrong, it won't come up without drilling down into "people.wright.edu" which you don't
know what that is. Nothing explains what that is. And then you have to click on "Advanced."
Other website searches give you names close to what you type. This one does not. It is so last
decade. This has been mentioned to the Web team with no success. Maybe CATs is the
proper place to get this fixed to save us time.
•
Thanks for all you do!
•
As a student that relies on technology working properly, I'm glad that Wright State has such a
strong IT team. It seems like even when there are issues with things like connectivity, that the
problems are resolved so quickly that I never seem to be affected by it.
•
I don't know if you guys are in charge of pilot as well, but the class dropdown needs to have
the option to hide classes. I've been here for two semesters and already the dropdown has
21 classes. Some classes have the same names as those I taught last semester. Difficult to
use; would be entirely unusable without the pin-to-top option. Please add a "hide class"
option

57
•
I know workshops are listed online, but it wouldn't hurt to send one email at the beginning of
the month (even if it is only to faculty that have frequented CTL over the past year) to
advertise the workshops of the month.
•
The fact that you attempt to prioritize my issues/needs makes me feel appreciated and not a
burden. The fact that your technicians attempt to provide additional tips and tricks also helps
persons who are not looking at this stuff everyday stay current. (Much appreciated!) Lastly,
you guys have good people throughout your organization which makes it all work well for
you.
•
Whether it is a phone call or in person help requested, we always receive good, sound advise,
help and/or instruction no matter what the situation is. All techs are very polite, very
knowlegable and come to our rescue in solving any issues we have, even the very difficult
ones. We appreciate all your time and efforts. You folks are wonderful! Thank you!
•
I am thankful that CaTS is there when needed.
•
Overall I view CaTS as being responsive and accountable for their responsibilities
•
Know that CATS has to keep faculty happy but customer service to our external prospects
should be of equal importance or at least better balanced.
•
The CaTS reps I have worked with on various issues have been very helpful and pleasant.
•
Nothing but praise for CaTS
•
Thanks for making my life easier.
•
good service any time I need help
•
there has been miscommunication with a CaTs staff in the past who was not available when
we had arranged a meeting; so efficiency can clearly be improved.
•
Although I have had customer service assistance, or attempts at assistance, that have run the
gamut from quite poor to excellent, I have not had to use CaTS in months so it's possible
those who basically sucked at their jobs no longer work there.
•
CaTS should consider doing a workshop on customer service. I never hesitate to call them or
recommend others to call them because I know all will be treated well by their team of
experts who provide quality services and support. A kind, encouraging word..."No
problem...glad I could help"...I "can" help you with that..."How can I be of assistance to you
today"...goes a very long way! -- especially when you are having a challenging time with
computer issues ; - )...Thank you.
•
Please be patient with new employees
•
Have been at larger universities, and by comparison i am very impressed with what CATS
does, how it is run, responsiveness, etc. THANKS!!
•
Thank you for being available to help in every situation and so quickly every time.
•
No complaints! You guys have been doing a good job and it's much appreciated!
•
Thank you, CATS, for your ongoing service to WSU retired community.
•
I'm finding it frustrating that Banner Admin is being run on outdated software. At this point in
time the ONLY way I can open Banner Admin in in Internet Explorer. In the last 2 years I have
had to move from Chrome and Firefox as they stop supporting the Java version due to

58
security concerns. I have to use Banner Admin to do my job. What are my options when
Internet explorer stops supporting it?
•
I seriously think CaTS is an important and valued aspect of the WSU community. You all do a
wonderful job and I appreciate you beyond words!!!!
