
ICAO
Aeronautical Telecommunication Network (ATN)
Manual for the ATN using IPS Standards and
Protocols (Doc 9896)
AugustApril 3026, 20092011
Draft Version 1819

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
i
FOREWORD
This document defines the data communications protocols and services to be used for
implementing the International Civil Aviation Organization (ICAO) Aeronautical
Telecommunications Network (ATN) using the Internet Protocol Suite (IPS). The
material in this document is to be considered in conjunction with the relevant Standards
and Recommended Practices (SARPs) as contained in Annex 10, Volume III, and Part I
Chapter 3.
Editorial practices in this document.
The detailed technical specifications in this document that include the operative verb
―shall‖ are essential to be implemented to secure proper operation of the ATN.
The detailed technical specifications in this document that include the operative verb
―should‖ are recommended for implementation in the ATN. However, particular
implementations may not require this specification to be implemented.
The detailed technical specifications in this document that include the operative verb
―may‖ are optional. The use or non use of optional items shall not prevent
interoperability between ATN/IPS nodes.
The Manual for the ATN using IPS Standards and Protocols is divided into the following
parts:
Part I – Detailed Technical Specifications
This part contains a general description of ATN/IPS. It covers the network, transport and
security requirements for the ATN/IPS.
Part II – Application Support
This part contains a description of applications supported by the ATN/IPS. It includes
convergence mechanisms and application services that allow the operation of legacy
ATN/OSI applications over the ATN/IPS transport layer.
Part III – Guidance
This part contains guidance material on ATN/IPS communications including information
on architectures, and general information to support ATN/IPS implementation.

ICAO
Aeronautical Telecommunication Network (ATN)
Manual for the ATN using IPS Standards and
Protocols (Doc 9896)
Part I
Detailed Technical Specifications

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
1
PART 1 TABLE OF CONTENTS
1.0 INTRODUCTION....................................................................................................... 2
1.1 GENERAL OVERVIEW ...............................................................................................2
2.0 REQUIREMENTS ...................................................................................................... 4
2.1 ATN/IPS ADMINISTRATION .....................................................................................4
2.1.1 The ATN/IPS ..................................................................................................... 4
2.1.2 ATN/IPS Mobility .............................................................................................. 4
2.2 LINK LAYER REQUIREMENTS ................................................................................5
2.3 INTERNET LAYER REQUIREMENTS ......................................................................5
2.3.1 General IPv6 Internetworking .......................................................................... 5
2.3.2 Mobile IPv6 ....................................................................................................... 5
2.3.3 Network Addressing .......................................................................................... 5
2.3.4 Inter-Domain Routing ....................................................................................... 6
2.3.5 Error Detection and Reporting ......................................................................... 7
2.3.6 Quality of Service (QoS) ................................................................................... 7
2.3.7 IP Version Transition ........................................................................................ 7
2.4 TRANSPORT LAYER REQUIREMENTS ...................................................................8
2.4.1 Transmission Control Protocol (TCP) ............................................................. 8
2.4.2 User Datagram Protocol (UDP) ...................................................................... 8
2.5 SECURITY REQUIREMENTS ....................................................................................8
2.5.2 Ground-Ground Security .................................................................................. 8
2.5.2.1 Ground-Ground IPsec/IKEv2 ........................................................................ 8
2.5.3 Air-Ground Security.......................................................................................... 9
2.5.3.1 Air-Ground Access Network Security ............................................................ 9
2.5.3.2 Air-Ground IPsec/IKEv2 ............................................................................... 9
2.5.3.3 Air-Ground Transport Layer Security ......................................................... 11
2.5.3.4 Air-Ground Application Layer Security....................................................... 11
2.6 PERFORMANCE ..............................................................................................................11
3.0 ATN APPLICATIONS ............................................................................................. 12
3.1 GROUND APPLICATIONS ................................................................................................12
3.1.1 Telephony (VoIP) ............................................................................................ 12
3.2 AIR-GROUND APPLICATIONS ........................................................................................12
3.2.1 Radio ............................................................................................................... 12
3.3 PERFORMANCE ..............................................................................................................12
3.3.1 Telephony (VoIP) ............................................................................................ 12
3.3.2 Radio (VoIP) ................................................................................................... 12
APPENDIX A – AS NUMBERING PLAN ................................................................... 13

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
2
1.0 INTRODUCTION
1.1 GENERAL OVERVIEW
This manual contains the minimum communication protocols and services that will
enable implementation of an ICAO Aeronautical Telecommunication Network (ATN)
based on the Internet Protocol Suite (IPS), referred to as the ATN/IPS. The scope of this
manual is on interoperability across Administrative Domains in the ATN/IPS
internetwork, although the material in this manual may also be used within an
Administrative Domain. Implementation of the ATN/IPS, including the protocols and
services included in this manual, will take place on the basis of regional air navigation
agreements between ICAO contracting States in accordance with Annex 10, Volume III,
Part I, Chapter 3, and Paragraph 3.3.2. Regional planning and implementation groups
(PIRG‘s) coordinate such agreements.
The ATN/IPS protocol architecture is illustrated in Figure 1. The ATN/IPS has adopted
the same four layer model as defined in Internet Society (ISOC) internet standard
STD003.
Note. — STD003 is a combination of Internet Engineering Task Force (IETF) RFC 1122
and RFC 1123.
Transport Layer
(TCP, UDP)
Internet Layer
(IPv6)
Link Layer
Internet Layer
(IPv6)
Link Layer
Transport Layer
(TCP, UDP)
Application
Layer
Internet Layer
(IPv6, BGP4+)
Application
Layer
Inter-Domain
Subnetwork
Inter-Domain
Router
Inter-Domain
Router
Local or
Intra-Domain
Subnetwork
Local or
Intra-Domain
Subnetwork
OSI/IPS
Convergence
OSI/IPS
Convergence
Peer-to-Peer Connections
Internet Layer
(IPv6, BGP4+)
Link Layer Link Layer
Figure 1 – ATN/IPS Protocol Architecture

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
3
This model has four abstraction layers called the link layer, the internet or IP layer, the
transport layer and the application layer.
As depicted in Figure 1, this manual does not adopt any specific link layer protocol as
this is a local or bi-lateral issue which does not affect overall interoperability.
This manual adopts the Internet Protocol version 6 (IPv6) for internet layer
interoperability. Implementation of IPv4 in ground networks, for transition to IPv6 (or as
a permanent network) is not addressed in this manual. IPv6 is to be implemented in air-
ground networks. The Border Gateway Protocol 4 with extensions is adopted for inter-
domain routing.
The Transmission Control Protocol (TCP) and User Datagram Protocol (UDP) are
adopted for connection-oriented and connectionless services at the transport layer.
Part II of this document includes convergence mechanisms and application services that
allow the operation of legacy ATN/OSI applications over the ATN/IPS transport layer.
Part III of this document includes guidance material to support ATN/IPS implementation.

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
4
2.0 REQUIREMENTS
2.1 ATN/IPS ADMINISTRATION
2.1.1 The ATN/IPS
2.1.1.1 The ATN/IPS internetwork consists of IPS nodes and networks operating in a
multinational environment in support of Air Traffic Service Communication (ATSC) as
well as Aeronautical Industry Service Communication (AINSC), such as Aeronautical
Administrative Communications (AAC) and Aeronautical Operational Communications
(AOC).
2.1.1.2 In this manual an IPS node is a device that implements IPv6. There are two types
of IPS nodes.
An IPS router is an IPS node that forwards Internet Protocol (IP) packets not
explicitly addressed to itself.
An IPS host is an IPS node that is not a router.
2.1.1.3 From an administrative perspective, the ATN/IPS internetwork consists of a
number of interconnected Administrative Domains. An Administrative Domain can be
an individual State, a group of States (e.g., an ICAO Region), an Air Communications
Service Provider (ACSP), an Air Navigation Service Provider (ANSP), or any other
organizational entity that manages ATN/IPS network resources and services.
2.1.1.4 Each Administrative Domain participating in the ATN/IPS internetwork shall
operate one or more IPS routers which execute the inter-domain routing protocol
specified in this manual.
2.1.1.5 From a routing perspective, inter-domain routing protocols are used to exchange
routing information between Autonomous Systems (AS), where an AS is a connected
group of one or more IP address prefixes. The routing information exchanged includes
IP address prefixes of differing lengths. For example, an IP address prefix exchanged
between ICAO regions may have a shorter length than an IP address prefix exchanged
between individual States within a particular region.
2.1.1.6 Administrative Domains should coordinate their policy for carrying transit traffic
with their counter parts.
2.1.2 ATN/IPS Mobility
2.1.2.1 ATN/IPS mobility is based on IPv6 mobility standards, operated by Mobility
Service Providers (MSP).

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
5
Note. — A MSP in the ATN/IPS is an instance of an Administrative Domain which may
be an ACSP, ANSP, Airline, Airport Authority, government or other aviation
organization.
2.1.2.2 ATN/IPS Mobility Service Providers (MSP) shall operate one or more home
agents (HA).
2.2 LINK LAYER REQUIREMENTS
2.2.1 The specification of the link layer characteristics for an IPS node is a local issue.
2.3 INTERNET LAYER REQUIREMENTS
2.3.1 General IPv6 Internetworking
2.3.1.1 IPS nodes shall implement IPv6 as specified in RFC 2460.
2.3.1.2 IPS nodes shall implement IPv6 Maximum Transmission Unit (MTU) path
discovery as specified in RFC 1981.
2.3.1.3 IPS nodes shall set the flow label field of the IPv6 header to zero, as it is not used
in the ATN/IPS.
2.3.2 Mobile IPv6
2.3.2.1 IPS mobile nodes shall implement Mobile IPv6 as specified in RFC 3775.
2.3.2.2 IPS home agents shall implement Mobile IPv6 as specified in RFC 3775.
2.3.2.3 IPS mobile nodes and home agents may implement extensions to Mobile IPv6 to
enable support for network mobility as specified in RFC 3963. enhancements to MIPv6
listed in PartIII section 5.2.
2.3.2.4 IPS nodes that implement Mobile IPv6 route optimization should allow route
optimization to be administratively enabled or disabled with the default being disabled.
Note. — The use of Mobile IPv6 route optimization is not mandated by this specification
until further standard RFCs have been developed by the IETF.
2.3.3 Network Addressing
2.3.3.1 IPS nodes shall implement IP Version 6 Addressing Architecture as specified in
RFC 4291.
2.3.3.2 IPS nodes shall use globally scoped IPv6 addresses when communicating over the
ATN/IPS.
Comment [Q1]: Action13-05

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
6
2.3.3.3 Administrative Domains shall obtain IPv6 address prefix assignments from their
Local Internet Registry (LIR) or Regional Internet Registry (RIR).
2.3.3.4 MSPs shall obtain a /32 IPv6 address prefix assignment for the exclusive use of
IPS Mobile Nodes or mobile networks.
2.3.3.5 MSPs should use the following IPv6 address structure for aircraft assignments.
Mobility Service Provider
Subnet
ID
Interface IDICAO Aircraft Address
RIR/LIR
32 bits 24 bits 8 bits
64 bits
Note 1. — Under this structure each aircraft constitutes a /56 IPv6 end site, which is
based on the ICAO 24-bit aircraft address as defined in Annex 10, Volume III, Appendix
to Chapter 9.
Note 2. — For onboard services (ATS, AOC, AAC, etc.), an aircraft may have either
multiple subnets interconnected to a mobile router, multiple MSPs or a combination of
both.
2.3.3.6 Mobility Service Providers (MSPs), shall advertise their /32 aggregate prefix to
the ATN/IPS.
2.3.4 Inter-Domain Routing
Note 1. — Inter-domain routing protocols are used to exchange routing information
among ASs.
Note 2. — For routing purposes, an AS has a unique identifier called an AS number.
Note 3. — A single Administrative Domain may be responsible for the management of
several ASs.
Note 4. — The routing protocol within an AS is a local matter determined by the
managing organization.
2.3.4.1 IPS routers which support inter-domain dynamic routing shall implement the
Border Gateway Protocol (BGP-4) as specified in RFC 4271.
2.3.4.2 IPS routers which support inter-domain dynamic routing shall implement the
BGP-4 multiprotocol extensions as specified in RFC 2858.
2.3.4.3 Administrative Domains shall use AS numbers for ATN/IPS routers that
implement BGP-4.

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
7
2.3.4.4 Administrative Domains that use private AS numbers shall follow the AS
numbering plan described in Part I of this document.
Note. — Administrative Domains that require additional private AS numbers should
coordinate through ICAO.
2.3.4.5 IPS routers which support inter-domain dynamic routing should authenticate
routing information exchanges as specified in RFC 2385.
2.3.5 Error Detection and Reporting
2.3.5.1 IPS nodes shall implement Internet Control Message Protocol (ICMPv6) as
specified in RFC 4443.
2.3.6 Quality of Service (QoS)
2.3.6.1 Administrative Domains shall make use of Differentiated Services (DiffServ) as
specified in RFC 2475 as a means to provide Quality of Service (QoS) to ATN/IPS
applications and services.
2.3.6.2 Administrative Domains shall enable ATN/IPS DiffServ class of service to meet
the operational and application requirements.
2.3.6.3 Administrative Domains supporting Voice over IP services shall assign those
services to the Expedited Forwarding (EF) Per-Hop Behavior (PHB) as specified by RFC
3246.
2.3.6.4 Administrative Domains shall assign ATN application traffic to the Assured
Forwarding (AF) PHB as specified by RFC 2597.
Note. — Assured forwarding allows the ATN/IPS operator to provide assurance of
delivery as long as the traffic does not exceed the subscribed rate. Excess traffic has a
higher probability of being dropped if congestion occurs.
2.3.6.5 Administrative Domains that apply measures of priority to the AF PHBs shall
assign relative measures based on the ATN mapping of priorities defined in Annex 10,
Volume III, Part I, Chapter 3, Table.3-1.
2.3.7 IP Version Transition
2.3.7.1 Administrative Domains should use the dual IP layer mechanism for IPv6 to IPv4
compatibility as described in RFC 4213.
Note. — This provision ensures that ATN/IPS hosts also support IPv4 for backward
compatibility with local IPv4 applications.
DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
8
2.4 TRANSPORT LAYER REQUIREMENTS
2.4.1 Transmission Control Protocol (TCP)
2.4.1.1 IPS nodes shall implement the Transmission Control Protocol (TCP) as specified
in RFC 793.
2.4.1.2 IPS nodes may implement TCP Extensions for High Performance as specified in
RFC 1323.
2.4.2 User Datagram Protocol (UDP)
2.4.2.1 IPS hosts shall implement User Datagram Protocol as specified in RFC 768.
2.4.3 Transport Protocol Port Numbers
2.4.3.1 IPS nodes shall support and make use of the TCP and/or UDP port numbers
defined in Part II of this document.
2.5 SECURITY REQUIREMENTS
Note. — The use of the following security requirements for communications in the
ATN/IPS should be based on a system threat and vulnerability analysis.
2.5.1 This section defines IPS node security requirements and capabilities but does not
impose their use for communications in the ATN/IPS.
2.5.2 Ground-Ground Security
Note. — IP layer security in the ground-ground ATN/IPS internetwork is implemented
using Internet Protocol security (IPsec) and the Internet Key Exchange (IKEv2) protocol.
2.5.2.1 Ground-Ground IPsec/IKEv2
2.5.2.1.1 IPS nodes in the ground-ground environment shall comply with the Security
Architecture for the Internet Protocol as specified in RFC 4301.
2.5.2.1.2. IPS nodes in the ground-ground environment shall implement the IP
Encapsulating Security Payload (ESP) protocol as specified in RFC 4303.
2.5.2.1.3 IPS nodes in the ground-ground environment may implement the IP
Authentication Header (AH) protocol as specified in RFC 4302.
2.5.2.1.4 IPS nodes in the ground-ground environment shall implement the Internet Key
Exchange (IKEv2) Protocol as specified in RFC 4306.
Comment [Q2]: Not in directories

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
9
2.5.2.1.5 IPS nodes in the ground-ground environment shall implement the Cryptographic
Algorithm Implementation Requirements for the Encapsulating Security Payload (ESP)
and Authentication Header (AH) if AH is implemented as specified in RFC 4835.
2.5.2.1.6 IPS nodes in the ground-ground environment shall implement the Null
Encryption Algorithm as specified in RFC 4835, but not the Null Authentication
Algorithm, when establishing IPsec security associations.
2.5.2.1.7 IPS nodes in the ground-ground environment shall implement the Cryptographic
Algorithms for Use in the Internet Key Exchange Version 2 (IKEv2) as specified in RFC
4307, when negotiating algorithms for key exchange.
2.5.2.1.8 IPS nodes in the ground-ground environment should use the Internet X.509
Public Key Infrastructure Certificate and Certificate Revocation List (CRL) Profile as
specified in RFC 5280, when digital signatures are used as the IKEv2 authentication
method.
2.5.2.1.9 IPS nodes in the ground-ground environment should use the Internet X.509
Public Key Infrastructure Certificate Policy and Certificate Practices Framework as
specified in RFC 3647, when digital signatures are used as the IKEv2 authentication
method.
Note. – The Air Transport Association (ATA) Digital Security Working Group (DSWG)
has developed a Certificate Policy (ATA Specification 42) for use in the aviation
community. ATA Specification 42 includes certificate and CRL profiles that are suitable
for aeronautical applications and interoperability with an aerospace industry PKI
bridge. These profiles provide greater specificity than, but do not conflict with, RFC
5280.
2.5.3 Air-Ground Security
2.5.3.1 Air-Ground Access Network Security
2.5.3.1.1 IPS mobile nodes shall implement the security provisions of the access network,
to enable access network security.
Note. – For example, the WiMAX, 3GPP, and 3GPP2 access networks have
authentication and authorization provisions.
2.5.3.2 Air-Ground IPsec/IKEv2
2.5.3.2.1 IPS nodes in the air-ground environment shall comply with the Security
Architecture for the Internet Protocol as specified in RFC 4301.
2.5.3.2.2 IPS nodes in the air-ground environment shall implement the IP Encapsulating
Security Payload (ESP) protocol as specified in RFC 4303.

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
10
2.5.3.2.3 IPS nodes in the air-ground environment shall implement
AUTH_HMAC_SHA2_256-128 as the integrity algorithm for ESP authentication as
specified in RFC 4868, when establishing IPsec security associations.
2.5.3.2.4 IPS nodes in the air-ground environment which implement encryption shall
implement AES-GCM with an 8 octet ICV and with a key length attribute of 128 bits for
ESP encryption and authentication as specified in RFC 4106.
2.5.3.2.5 IPS nodes in the air-ground environment shall implement the Internet Key
Exchange (IKEv2) Protocol as specified in RFC 4306.
2.5.3.2.6 IPS nodes in the air-ground environment shall implement IKEv2 with the
following transforms:
a) PRF_HMAC_SHA_256 as the pseudo-random function as specified in RFC 4868.
b) 256-bit random ECP group for Diffie-Hellman Key Exchange values as specified
in RFC 4753.
c) ECDSA with SHA-256 on the P-256 curve as the authentication method as
specified in RFC 4754.
d) AES-CBC with 128-bit keys as the IKEv2 encryption transforms as specified in
RFC 3602.
e) HMAC_SHA_256-128 as the IKEv2 integrity transform as specified in RFC
4868.
2.5.3.2.7 IPS nodes in the air-ground environment should use the Internet X.509 Public
Key Infrastructure Certificate and Certificate Revocation List (CRL) Profile as specified
in RFC 5280, when digital signatures are used as the IKEv2 authentication method.
2.5.3.2.8 IPS nodes in the air-ground environment should use the Internet X.509 Public
Key Infrastructure Certificate Policy and Certificate Practices Framework as specified in
RFC 3647, when digital signatures are used as the IKEv2 authentication method.
Note. – The Air Transport Association (ATA) Digital Security Working Group (DSWG)
has developed a Certificate Policy (ATA Specification 42) for use in the aviation
community. ATA Specification 42 includes certificate and CRL profiles that are suitable
for aeronautical applications and interoperability with an aerospace industry PKI
bridge. These profiles provide greater specificity than, but do not conflict with, RFC
5280.
2.5.3.2.9 IPS nodes in the air-ground environment, shall implement Mobile IPv6
Operation with IKEv2 and the Revised IPsec Architecture as specified in RFC 4877.

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
11
2.5.3.3 Air-Ground Transport Layer Security
2.5.3.3.1 IPS mobile nodes and correspondent nodes may implement the Transport Layer
Security (TLS) protocol as specified in RFC 5246.
2.5.3.3.2 IPS mobile nodes and correspondent nodes shall implement the Cipher Suite
TLS_ECDH_ECDSA_WITH_AES_128_CBC_SHA as specified in RFC 4492 when
making use of TLS.
2.5.3.4 Air-Ground Application Layer Security
2.5.3.4.1 IPS mobile nodes and correspondent nodes may implement application layer
security at the IPS Dialogue Service Boundary, which is specified in Part II of this
document.
2.5.3.4.2 IPS mobile nodes and correspondent nodes shall append a keyed-hashed
message authentication code (HMAC) as specified in RFC 2104 using SHA-256 as the
cryptographic hash function, when application layer security is used.
2.5.3.4.3 An HMAC tag truncated to 32 bits shall be computed over the User Data
concatenated with a 32-bit send sequence number for replay protection, when application
layer security is used.
2.5.3.4.4 IKEv2 shall be used for key establishment as specified in section 2.5.2.2, when
application layer security is used.
2.6 PERFORMANCE
2.6.1 IPS nodes may implement RFC 2488 in order to improve performance over satellite
links.
2.6.2 IPS nodes may implement the RObust Header Compression Framework (ROHC) as
specified in RFC 4995 in order to optimize bandwidth utilization.
2.6.3 If ROHC is supported, then the following ROHC profiles shall be supported as
applicable:
a. the ROHC profile for TCP/IP specified in RFC 4996
b. the ROHC profile for RTP/UDP/ESP specified in RFC 3095
c. the IP-Only ROHC profile specified in RFC 4843
d. the ROHC over Point-to-Point Protocol (PPP) profile specified in RFC 3241
DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
12
3.0 ATN Applications
Detailed information for the development and deployment of ATN applications for use in
ICAO Regions. Refer to the following sections for the applicable standard.
3.1 GROUND APPLICATIONS
Refer to the following sections for detailed specifications for ground applications.
3.1.1 Telephony (VoIP)
Telephony ground applications shall be governed by EUROCAE document ED-137A,
Interoperability Standards for VoIP ATM Components, Part 2 – Telephone, edition
September 2010.
Note: – ED-137A - Interoperability Standards for VoIP ATM Components, edition
September 2010 is available for download on the EUROCAE website at:
http://www.eurocae.net/
3.2 AIR-GROUND APPLICATIONS
Refer to the following sections for detailed specifications for air-ground applications
3.2.1 Radio
Radio air-ground applications on the ground component shall be governed by
EUROCAE document ED-137A, Interoperability Standards for VoIP ATM Components,
Part 1 – Radio, edition September 2010.
3.3 PERFORMANCE
3.3.1 Telephony (VoIP)
Telephone performance specification shall be governed by EUROCAE document, ED-
138, Part 1.
3.3.2 Radio (VoIP)
Radio performance specification shall be governed by EUROCAE document, ED-138,
Part 1.
Note – ED138 is available for download on the EUROCAE website at:
http://www.eurocae.net/

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
13
APPENDIX A – AS Numbering Plan
Note: This numbering plan covers ICAO Contracting and Non-Contracting States, and
Territories.
ICAO
Region
Country/Organisation/Location
AS
Number
ICAO
Region
Country/Org./Loc.
AS
Number
MID
Afghanistan
64512
EUR/NAT
Ireland
64688
APAC
American Samoa
64513
EUR/NAT
Italy
64692
ESAF
Angola
64514
EUR/NAT
Kazakhstan
64696
NACC
Anguilla I. (U.K.)
64515
EUR/NAT
Kyrgyzstan
64700
NACC
Antigua and Barbuda
64516
EUR/NAT
Latvia
64704
SAM
Argentina
64517
EUR/NAT
Liechtenstein
64706
NACC
Aruba (Netherlands)
64518
EUR/NAT
Lithuania
64708
WACAF
Ascension and St Helena Is.
(U.K.)
64519
EUR/NAT
Luxembourg
64712
APAC
Australia
64520
EUR/NAT
The former
Yugoslav Republic
of Macedonia
64716
NACC
Bahamas
64521
EUR/NAT
Malta
64720
APAC
Bangladesh
64522
EUR/NAT
Monaco
64728
NACC
Barbados
64523
EUR/NAT
Montenegro
64820
NACC
Belize
64524
EUR/NAT
Morocco
64824
WACAF
Benin
64525
EUR/NAT
Netherlands
64732
NACC
Bermuda (U.K.)
64526
EUR/NAT
Norway
64736
APAC
Bhutan
64527
EUR/NAT
Poland
64740
SAM
Bolivarian Republic of Venezuela
64528
EUR/NAT
Portugal
64744
SAM
Bolivia
64529
EUR/NAT
Republic of
Moldova
64724
ESAF
Botswana
64530
EUR/NAT
Romania
64748
SAM
Brazil
64531
EUR/NAT
Serbia
64756
ESAF
British Indian Ocean Territory
64532
EUR/NAT
Russian Federation
64752
APAC
Brunei Darussalam
64533
EUR/NAT
San Marino
64828
WACAF
Burkina Faso
64534
EUR/NAT
Slovak Republic
64760
ESAF
Burundi
64535
EUR/NAT
Slovenia
64764
APAC
Cambodia
64536
EUR/NAT
Spain
64768
WACAF
Cameroon
64537
EUR/NAT
Sweden
64772
NACC
Canada
64538
EUR/NAT
Tajikistan
64776
WACAF
Cape Verde
64539
EUR/NAT
Switzerland
64780
NACC
Cayman Is. (U.K.)
64540
EUR/NAT
The Holy See
64782
WACAF
Central African Republic
64541
EUR/NAT
Tunisia
64832
WACAF
Chad
64542
EUR/NAT
Turkey
64784
SAM
Chile
64543
EUR/NAT
Turkmenistan
64788

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
14
APAC
China
64544
EUR/NAT
Ukraine
64792
SAM
Colombia
64545
EUR/NAT
United Kingdom
64796
WACAF
Congo
64546
EUR/NAT
Uzbekistan
64800
APAC
Cook Islands
64547
EUR/NAT
Regional - Europe
65108
NACC
Costa Rica
64548
EUR/NAT
Regional - Europe
65112
WACAF
Côte d'Ivoire
64549
EUR/NAT
EUROCONTROL
65208
NACC
Cuba
64550
EUR/NAT
EUROCONTROL
65212
APAC
Democratic People's Republic of
Korea
64551
EUR/NAT
EUROCONTROL
65216
WACAF
Democratic Republic of the
Congo
64552
EUR/NAT
EUROCONTROL
65220
APAC
Democratic Republic of Timor-
Leste
64553
EUR/NAT
EUROCONTROL
65224
ESAF
Djibouti
64554
EUR/NAT
EUROCONTROL
65228
NACC
Dominica
64555
EUR/NAT
EUROCONTROL
65232
NACC
Dominican Republic
64556
EUR/NAT
EUROCONTROL
65236
APAC
Easter Island (Chile)
64557
WACAF
Mauritania
65237
SAM
Ecuador
64558
ESAF
Mauritius
65238
MID
Egypt
64559
NACC
Mexico
65239
NACC
El Salvador
64560
APAC
Micronesia,
Federated States of
65240
WACAF
Equatorial Guinea
64561
APAC
Midway Is. (U.S.)
65241
ESAF
Eritrea
64562
APAC
Mongolia
65242
ESAF
Ethiopia
64563
NACC
Montserrat I. (U.K.)
65243
SAM
Falklands Is. (U.K.)
64564
ESAF
Mozambique
65244
NACC
French Antilles
64565
APAC
Myanmar
65245
WACAF
Gabon
64566
ESAF
Namibia
65246
WACAF
Gambia
64567
APAC
Nauru
65247
WACAF
Ghana
64568
APAC
Nepal
65248
NACC
Grenada
64569
NACC
Netherlands
Antilles
65249
APAC
Guam (U.S.)
64570
APAC
New Caledonia
65250
NACC
Guatemala
64571
APAC
New Zealand
65251
WACAF
Guinea
64572
NACC
Nicaragua
65252
WACAF
Guinea-Bissau
64573
WACAF
Niger
65253
SAM
Guyana
64574
WACAF
Nigeria
65254
SAM
Guyane Francaise
64575
APAC
Niue Island (New
Zealand)
65255
NACC
Haiti
64576
MID
Oman
65256
SAM
Honduras
64577
MID
Pakistan
65257
APAC
Hong Kong Special
Administrative Region of China
64578
APAC
Palau
65258
APAC
Iles Wallis Et Futuna (France)
64579
Palestinian
Territory, occupied
65259
APAC
India
64580
APAC
Palmyra Is. (U.S.)
65260

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
15
APAC
Indonesia
64581
SAM
Panama
65261
MID
Iran, Islamic Republic of
64582
APAC
Papua New Guinea
65262
MID
Iraq
64583
SAM
Paraguay
65263
MID
Israel
64584
SAM
Peru
65264
NACC
Jamaica
64585
APAC
Philippines
65265
APAC
Japan
64586
APAC
Pitcairn Island
(U.K.)
65266
APAC
Johnston I. (U.S.)
64587
APAC
Polynesie
Francaise
65267
MID
Jordan
64588
NACC
Puerto Rico
65268
ESAF
Kenya
64589
MID
Qatar
65269
MID
Kingdom of Bahrain
64590
APAC
Republic of Korea
65270
APAC
Kingman Reef (U.S.)
64591
APAC
Republic of the Fiji
Islands
65271
APAC
Kiribati
64592
ESAF
Rwanda
65272
MID
Kuwait
64593
NACC
Saint Kitts and
Nevis
65273
ESAF
La Reunion (France)
64594
NACC
Saint Lucia
65274
APAC
Lao People's Democratic
Republic
64595
NACC
Saint Vincent and
the Grenadines
65275
MID
Lebanon
64596
APAC
Samoa
65276
ESAF
Lesotho
64597
WACAF
Sao Tome and
Principe
65277
WACAF
Liberia
64598
MID
Saudi Arabia
65278
MID
Libyan Arab Jamahiriya
64599
WACAF
Senegal
65279
APAC
Macao Special Administrative
Region of China
64600
ESAF
Seychelles
65280
ESAF
Madagascar
64601
WACAF
Sierra Leone
65281
ESAF
Malawi
64602
APAC
Singapore
65282
APAC
Malaysia
64603
APAC
Solomon Islands
65283
APAC
Maldives
64604
ESAF
Somali Republic
65284
WACAF
Mali
64605
ESAF
South Africa
65285
APAC
Mariana Is. (U.S.)
64606
APAC
Sri Lanka
65286
APAC
Marshall Islands
64607
MID
Sudan
65287
EUR/NAT
Albania
64608
SAM
Suriname
65288
EUR/NAT
Algeria
64804
ESAF
Swaziland
65289
EUR/NAT
Andorra
64808
MID
Syrian Arab
Republic
65290
EUR/NAT
Armenia
64612
APAC
Thailand
65291
EUR/NAT
Austria
64616
WACAF
Togo
65292
EUR/NAT
Republic of Azerbaijan
64620
APAC
Tonga
65293
EUR/NAT
Belarus
64624
NACC
Trinidad And
Tobago
65294
EUR/NAT
Belgium
64628
NACC
Turks And Caicos
Islands (U.K.)
65295
EUR/NAT
Bosnia and Herzegovina
64632
APAC
Tuvalu
65296

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
16
EUR/NAT
Bulgaria
64636
ESAF
Uganda
65297
EUR/NAT
Croatia
64640
ESAF
Union of the
Comoros
65298
MID
Cyprus
64644
MID
United Arab
Emirates
65299
EUR/NAT
Czech Republic
64648
ESAF
United Republic of
Tanzania
65300
EUR/NAT
Denmark
64652
NACC
United States of
America
65301
EUR/NAT
Estonia
64656
SAM
Uruguay
65302
EUR/NAT
Finland
64660
APAC
Vanuatu
65303
EUR/NAT
France
64664
APAC
Viet Nam
65304
EUR/NAT
Georgia
64668
NACC
Virgin Islands
(U.K.)
65305
EUR/NAT
Germany
64672
NACC
Virgin Islands
(U.S.)
65306
EUR/NAT
Gibraltar
64812
APAC
Wake I. (U.S.)
65307
EUR/NAT
Greece
64676
Western Sahara
65308
EUR/NAT
Greenland
64816
MID
Yemen
65309
EUR/NAT
Hungary
64680
ESAF
Zambia
65310
EUR/NAT
Iceland
64684
ESAF
Zimbabwe
65311

ICAO
Aeronautical Telecommunication Network (ATN)
Manual for the ATN using IPS Standards and
Protocols (Doc 9896)
Part II
IPS Applications

Part II Table of Contents
1.0 INTRODUCTION .................................................................................................... 36
1.1 OBJECTIVE ...................................................................................................................36
2.0 LEGACY ATN APPLICATIONS .......................................................................... 36
2.1 GROUND APPLICATIONS ...............................................................................................36
2.1.1 ATSMHS ......................................................................................................... 36
2.1.2 AIDC .............................................................................................................. 36
2.2 AIR-GROUND APPLICATIONS .........................................................................................47
2.2.1 Dialogue Service ............................................................................................ 47
2.2.2 CPDLC, ADS and FIS .................................................................................... 58
2.2.3 CM .................................................................................................................. 58
2.2.4 ATN IPS Dialogue Service Primitives ........................................................... 58
2.2.5 Dialogue Service Definition ......................................................................... 610
2.3 TRANSPORT LAYER ..................................................................................................2326
2.3.1Overview ..................................................................................................... 2326
2.3.2 Port Numbers ............................................................................................. 2427
2.3.3 Providing Dialogue Service over UDP ...................................................... 2427
2.3.4 Connection-ids ........................................................................................... 2528
2.3.5 Detecting Lost Datagrams ......................................................................... 2629
2.3.6 Connection Timeout ................................................................................... 2730
2.3.7 ―More‖ Indicator ....................................................................................... 2730
2.3.8 DS-Provider Parameters ........................................................................... 2831
2.4 IPS DIALOGUE SERVICE STATE TABLES ...................................................................2932
2.4.1 IPS Dialogue Service TCP State Tables .................................................... 2932
2.4.2 IPS Dialogue Service UDP State Tables ................................................... 3134
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
3
1.0 INTRODUCTION
1.1 OBJECTIVE
Note. – This part indicates how legacy ATN applications can make use of the ATN/IPS.
2.0 LEGACY ATN APPLICATIONS
Note. – Legacy ATN applications are defined in Doc 9705 and/or Doc 9880. The ATN
applications described in Doc 9705/9880 specify the use of the ATN/OSI layers for
communication services. This section indicates how those applications make use of the
ATN/IPS with minimal impact on the applications themselves.
2.1 GROUND APPLICATIONS
2.1.1 ATSMHS
Note 1. – The ATS Message Handling Services (ATSMHS) application aims at providing
generic message services over the Aeronautical Telecommunication Network (ATN).
Note 2. – IPS hosts that support the ATSMHS application shall comply with Doc 9880
Part IIB.
2.1.1.1 To operate ATSMHS over ATN/IPS, IPS hosts shall:
a) make use of RFC 2126 to directly provide TCP/IPv6 interface; or,
b) make use of RFC 1006 to provide a TCP/IPv4 interface combined with
IPv4/IPv6 protocol translation device(s).
2.1.1.2 IPS hosts that support the ATSMHS application shall make use of TCP port
number 102 as specified in RFC 1006 and RFC 2126.
2.1.2 AIDC
Note 1. – The AIDC application, as defined in Doc 9694, exchanges information between
ATS Units (ATSUs) for support of critical Air Traffic Control (ATC) functions, such as
notification of flights approaching a Flight Information Region (FIR) boundary,
coordination of boundary conditions and transfer of control and communications
authority.
Note 2. – AIDC as defined in Doc 9880, Part IIA is currently not planned for
implementation in the ATN/IPS environment.
2.1.2.1 IPS hosts in the ATN that support the AIDC application exchanges may make use
of the equivalent operational application described in the EUROCONTROL
Specifications for On-Line Data Interchange (OLDI).

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
4
2.1.2.2 IPS hosts in the ATN that support the OLDI application shall make use of
EUROCONTROL Specifications for the Flight Message Transfer Protocol to operate the
application over IPv6.
2.1.2.3 IPS hosts in the ATN that support the EUROCONTROL Flight Message Transfer
Protocol shall make use of TCP port number 8500.
2.2 AIR-GROUND APPLICATIONS
2.2.1 Dialogue Service
2.2.1.1 The Dialogue Service (DS), as documented in Doc 9880 Part III, serves as an
interface between the ATN applications and the ATN/OSI upper layer protocols via the
control function. In order to minimize the impact on the ATN applications a new
dialogue service was developed to support application implementation over the ATN/IPS.
This section specifies a replacement for the ATN/OSI DS interface to the upper layers,
and is named the IPS DS.
2.2.1.2 The IPS DS maps TCP/UDP primitives to the ATN application DS interface as
depicted in Figure 1.
Figure 1. ATN IPS Upper Layers Diagram
2.2.1.3 Primitives from the ATN/OSI DS will be mapped as detailed in the following
sections. This mapping is used as a substitute for the Upper Layer Communications
Service (ULCS) specification of ICAO Doc 9880 Part III.
2.2.1.4 The ATNPKT header format defined below describes a dedicated format designed
to accommodate the passing of ATN application data over the ATN/IPS. Either TCP or
UDP may be used with the ATNPKT header format.
Application User
ATN-App ASE
IPS DS
TCP/UDP
DP

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
5
2.2.2 CPDLC, ADS and FIS
2.2.2.1 IPS hosts that support ATN/OSI Controller-Pilot Data Link (CPDLC), Automatic
Dependent Surveillance (ADS) and Flight Information Services (FIS) applications shall
use the IPS DS instead of the DS defined in Doc 9880.
2.2.3 CM
2.2.3.1 IPS hosts that support the ATN Context Management (CM) application shall
support extensions of its abstract syntax notation (ASN) as described in Part III of this
document.
Note 1. – This is in order to allow passing the new IPS addressing information contained
in the updated CM application ASN.1.
Note 2. – The CM application is also known as the Data Link Initiation Capability
(DLIC) service.
Note 3. – It is expected that a later edition of Doc 9880 will include these extensions
taking precedence over those specified in this document.
2.2.4 ATN IPS Dialogue Service Primitives
Note. – In order to retain commonality with the ULCS dialogue service primitives
described in Doc 9880, the IPS DS uses the same primitive names.
2.2.4.1 IPS nodes that support the DS functionality shall exhibit the behaviour defined by
the service primitives in Table 1.
Table 1. Dialogue Service Primitives
Service
Description
D-START
This is a confirmed service used to establish the binding
between the communicating DS-Users.
D-DATA
This unconfirmed service is used by a DS-User to send a
message from that DS-User to the peer DS-User.
D-END
This is a confirmed service used to provide the orderly
unbinding between the communicating DS-Users, such
that any data in transit between the partners is delivered
before the unbinding takes effect.
D-ABORT
This unconfirmed service can be invoked to abort the
relationship between the communicating DS-Users. Any
data in transit between them may be lost.

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
6
Service
Description
D-P-ABORT
This unconfirmed service is used to indicate to the DS-
User that the dialogue service provider has aborted the
relationship with the peer DS-User. Any data in transit
between the communicating DS-Users may be lost.
D-UNIT-DATA
This unconfirmed service is used to send a single data item
from one peer DS-User to another. Any problem in
delivering the data item to the recipient will not be
signalled to the originator. This service is specified in 2.7.
Table 2. Parameters of the Dialogue Service Primitives
Service
Parameters
D-START
Called Peer ID
Called Sys-ID
Called Presentation Address
Calling Peer ID
Calling Sys-ID
Calling Presentation Address
DS-User Version Number
Security Requirements
Quality-of-Service
Result
Reject Source
User Data
D-DATA
User Data
D-END
Result
User Data
D-ABORT
Originator
User Data
D-P-ABORT
(no parameters)
Note. – The parameters of the DS primitives are mapped to either the IP header, a field
of the transport protocol header, or as transport data in the ATNPKT format defined in
2.2.5.2.
2.2.5 Dialogue Service Definition

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
7
2.2.5.1 Sequence of Primitives
2.2.5.1.1 IPS nodes that support the DS functionality shall allow peer communicating
DS-Users to:
a) establish a dialogue;
b) exchange user data;
c) terminate a dialogue in an orderly or abnormal fashion;
d) be informed of DS abnormal dialogue termination due to the underlying
communication failure; and
e) be consistent with the appropriate use of the corresponding service
primitives.
2.2.5.1.2 Either DS-User may send data at any time after the initial D-START exchange,
by using the D-DATA service. Under normal circumstances, a dialogue is released by a
DS-User invoking the D-END service. A dialogue is abnormally released with the D-
ABORT service. If the underlying service provider abnormally releases the dialogue, the
DS-Users are notified with the D-P-ABORT service indication.
2.2.5.1.3 It is only valid for the DS-User to issue and receive primitives for a ―dialogue‖
in the sequence specified in Table 3. The table cells containing ―Y‖ indicate valid
primitives which may follow the DS primitive columns headings. For example, only ―D-
START ind‖ can follow the ―D-END cnf‖ primitive.
Table 3. Sequence of DS primitives for one Dialogue at one DS-User
The DS primitive ->
D-START
D-DATA
D-END
D-ABORT
D-P-
ABORT
May be followed by the DS primitive Y
Req
cnf
ind
Rsp
req
ind
req
cnf
ind
rsp
req
ind
ind
1 D-START req
2 D-START cnf (accepted)
Y
3 D-START ind
Y
Y
Y
Y
Y
4 D-START rsp (accepted)
Y
5 D-DATA req
Y
Y
Y
Y
Y
6 D-DATA ind
Y
Y
Y
Y
Y
7 D-END req
Y
Y
Y
Y
8 D-END cnf (accepted)
Y
9 D-END ind
Y
Y
Y
Y

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
8
The DS primitive ->
D-START
D-DATA
D-END
D-ABORT
D-P-
ABORT
May be followed by the DS primitive Y
Req
cnf
ind
Rsp
req
ind
req
cnf
ind
rsp
req
ind
ind
10 D-END rsp (accepted)
Y
11 D-ABORT req
Y
Y
Y
Y
Y
Y
Y
Y
12 D-ABORT ind
Y
Y
Y
Y
Y
Y
Y
Y
13 D-P-ABORT ind
Y
Y
Y
Y
Y
Y
Y
Y
2.2.5.2 ATNPKT Format
2.2.5.2.1 The purpose of the ATNPKT is to convey information between peer DS-Users
during the processing of a DS primitive. It is carried in the data part of the transport
protocol (either TCP or UDP). It is used to convey parameters of the service primitives
that cannot be mapped to existing IP or transport header fields. The ATNPKT will also
convey information to indicate the Dialogue Service protocol function (e.g. the type of
DS primitive).
2.2.5.2.2 In order to provide the most efficient use of bandwidth, a variable length format
is used. The variable length format will allow optimized processing of the DS primitive.
This is an important issue when operating over narrow band or costly air ground
communication links.
2.2.5.2.3 The ATNPKT format contains two parts:
a fixed part that is present regardless of the DS primitive, and
a variable part for optional fields.
2.2.5.2.4 The presence of optional parameters is indicated by setting bits with in the fixed
part of the ATNPKT. These bits are referred to as 'Presence Flags' and form the Presence
Field. The position of an optional parameter in the variable part is determined by its
position in the Presence Field. The ATNPKT format is shown in Figure 2.
Figure 2. ATNPKT Format
2.2.5.2.5 The optional parameter representation, in the variable part of the ATNPKT, will
be determined by the parameter definition. Parameters of variable length will be

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
9
represented in the LV format (i.e. Length + Value). Fixed length parameters will be
represented by their value.
2.2.5.3 ATNPKT Fields
2.2.5.3.1 ATNPKT field formats are described using the convention ( <bits> /<provider>
/ <usage> ) where:
<bits> indicates the size in bits of the field value (excluding Length for LV
parameters),
<provider> indicates whether the value is provided by the DS-User as primitive
parameter (external) or assigned by the DS-Provider (internal),
<usage> indicates whether or not the DS-User is to submit a value when invoking
the corresponding primitive parameter (optional vs. mandatory).
2.2.5.4 Fixed Part of ATNPKT
2.2.5.4.1 ATNPKT Version
Note. – The ATNPKT version indicates the version of the ATNPKT header.
2.2.5.4.1.1 The ATNPKT version shall be set to 1 and have a format of (4 bits / internal /
mandatory).
Note 1. – The ATNPKT version is a number that will increment for any subsequent
modifications to the ATNPKT.
Note 2. – Reserving 4 bits will allow for up to 15 versions.
Note 3. – This field is not exposed at the DS-User's level; it will be set by the DS-
Provider.
2.2.5.4.2 DS Primitive
Note. – The DS Primitive field is set by the DS-Provider to indicate the type of DS
primitive of the packet.
2.2.5.4.2.1 The DS Primitive field shall take one of the values specified below and have a
format of (4 bits / internal / mandatory):
Value
Assigned DS Primitive
1
D-START
2
D-STARTCNF
3
D-END
4
D-ENDCNF

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
10
5
D-DATA
6
D-ABORT
7
D-UNIT-DATA
8
D-ACK
9
D-KEEPALIVE
Note 1. – Reserving 4 bits will give provision for up to 16 protocol elements, allowing up
to 7 additional primitives to be defined.
Note 2. – The D-P-ABORT is not listed, as it is not sent end-to-end. Upon receipt of an
abnormal event or expiration of an inactivity timer, a D-P-ABORT will be indicated to
the DS-User.
2.2.5.4.3 Application Technology Type
Note. – The Application Technology Type identifies the type of application information
that is being carried. Other applications may also take advantage of the IPS
infrastructure, e.g. FANS-1/A, ACARS, etc.
2.2.5.4.3.1 The Application Technology Type shall be set to a value of b000 to indicate
―ATN/IPS DS‖ and have a format of (3 bits / internal / optional).
Note. – The use or definition of other values is outside the scope of this manual.
2.2.5.4.4 More
Note. – The More bit will be used for segmentation and reassembly of UDP datagrams;
and is part of the reliability mechanisms further described in 2.3.
2.2.5.4.4.1 The more bit shall be set to 0 to indicate a single or last segment; it shall be set
to 1 to indicate the first or intermediate segment and have a format of (1 bit / internal /
optional).
2.2.5.4.5 Presence Field
Note. – The Presence Field is a series of Presence Flags (or bits) that indicate whether
or not optional fields are present in the variable part of the ATNPKT.
2.2.5.4.5.1 The Presence Field has a format of (12 bits / internal / mandatory).
2.2.5.4.5.2 A Presence Flag shall be set to 0 to indicate the absence of an optional field; it
shall be set to 1 to indicate the presence of an optional field.
2.2.5.4.5.3 The optional field details shall comply with Table 4.

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
11
Table 4. Presence Field Details
Bit
Optional field
Size (in bits)
Format
1
Description
0
Source ID
16
V
DS connection identifier of the sender
1
Destination ID
16
V
DS connection identifier of the recipient
2
Sequence numbers
8
V
Sequence numbers (Ns, Nr)
3
Inactivity time
8
V
Inactivity timer value of the sender (in minutes)
4
Called Peer ID
24 to 64 (+8)
LV
2
Called Peer ID (provided by the local DS-User)
5
Calling Peer ID
24 to 64 (+8)
LV
2
Calling Peer ID (provided by the local DS-User)
6
Content Version
8
V
Version of the application data carried
7
Security Indicator
8
V
Security requirements: 0 – No security (default value) 1
– Secured dialogue supporting key management 2 –
Secured dialogue 3…255 – Reserved
8
Quality of Service
8
V
ATSC Routing Class: 0 – No traffic type policy
preference 1 – "A" 5 – "E" 2 – "B" 6 – "F" 3 – "C" 7
– "G" 4 – "D" 8 – "H" 9…255 – Reserved
9
Result
8
V
Result of a request to initiate or terminate a dialogue: 0
– accepted (default value) 1 – Rejected transient 2 –
Rejected permanent 3…255 – Reserved
10
Originator
8
V
Originator of the abort: 0 – user (default value) 1 –
provider 2…255 – Reserved
11
User Data
UDP : 0 to 8184
3
(+16)
TCP: Variable size
(+16)
LV
2
User Data (provided by the local DS User)
Note 1. – An optional field is present in the variable part when the corresponding bit is
set in the Presence Field and has one of the following formats:
V = value; or
LV = length (1 or 2 byte(s)) + value
Note 2. – The additional bits required for the length part of LV parameters is indicated
between brackets in the above table.
Note 3. – Refer to 2.2.5.5.13 for details regarding the size of the User Data parameter.
2.2.5.5 Variable Parts of ATNPKT
Note. – The variable parts of the ATNPKT will be provided depending on the DS
primitive being invoked and the current state of the application using the IPS DS.

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
12
2.2.5.5.1 The position of an optional field in the variable part of the ATNPKT shall
match the relative position of its corresponding bit in the Presence Field (i.e. options are
in the same order as the presence flags).
2.2.5.5.2 Source ID
Note. – The Source ID identifies the DS connection at the sender side. This field is used
as part of the reliability mechanisms described in 2.3.
2.2.5.5.2.1 The Source ID shall be present in the D-START and D-STARTCNF
primitives, and also when D-ABORT is transmitted after D-START and before D-
STARTCNF is received and have a format of (16 bits / internal / optional).
2.2.5.5.3 Destination ID
Note. – The Destination ID identifies the connection at recipient side. This field is used
as part of the reliability mechanisms described in 2.3.
2.2.5.5.3.1 The Destination ID shall be present in the D-STARTCNF, D-DATA, D-END,
D-ENDCNF, D-ABORT, D-ACK and D-KEEPALIVE primitives and have a format of
(16 bits / internal / optional).
2.2.5.5.4 Sequence Numbers
Note. – The Sequence Numbers field contains the sequence numbers to be included in the
ATNPKT. This mechanism is used to detect the loss and the duplication of UDP
datagrams; it allows implicit (i.e. the service confirmation) or explicit acknowledgement
(D-ACK). This field is part of the reliability mechanisms described in 2.3.
2.2.5.5.4.1 The Sequence Numbers field shall be present in all DS primitives over UDP
and have the format (8 bits / internal / mandatory) as detailed in Figure 3 below:
Figure 3. Sequence Number Format
N(S) - [0…15] - sequence number of the ATNPKT sent.
N(R) - [0…15] - expected sequence number of the next ATNPKT to be received.
Note. – For D-ACK and D-KEEPALIVE, only the N(R) is meaningful on transmission.
2.2.5.5.4.2 When using Sequence Numbers with D-ACK and D-KEEPALIVE over UDP,
the current value of the send sequence number for N(S) may be used without
subsequently incrementing it after transmission.

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
13
2.2.5.5.5 Inactivity Time
Note. – The Inactivity Time indicates the time value (in minutes) of the inactivity timer at
the sender side. This field is used as part of the reliability mechanisms described in 2.3.
2.2.5.5.5.1The Inactivity Time shall be optionally present in the D-START and D-
STARTCNF Primitives and have the format (8 bits / internal / optional).
2.2.5.5.5.2 When this parameter is not provided by the DS-User, the default value of 4
minutes shall be used as inactivity timer by the source DS-Provider.
2.2.5.5.6 Called Peer ID
Note. – The Called Peer ID identifies the intended peer DS-User.
2.2.5.5.6.1 The Called Peer ID shall be either a 24-bit ICAO Aircraft Identifier or a 3 – 8
character ICAO Facility Designation and have the format (24 to 64 bits / external /
optional).
2.2.5.5.7 Calling Peer ID
Note. – The Calling Peer ID identifies the initiating peer DS-User.
2.2.5.5.7.1 The Calling Peer ID shall be either a 24 bit ICAO Aircraft Identifier or a 3 – 8
character ICAO Facility Designation and have the format (24 to 64 bits / external /
optional).
2.2.5.5.8 Content Version
Note. – The Content Version field is used to indicate the application’s version number.
2.2.5.5.8.1 The Content Version shall be the version of the ASN.1 syntax used for the
User Data field and have the format (8 bits / external / optional).
2.2.5.5.9 Security Indicator
Note 1. – The Security Indicator parameter is used to convey the level of security to be
applied to the dialogue. In Doc 9880, this field is referred as 'Security Requirements'; it
is renamed here since 'requirement' is not really appropriate in this case. It is really an
indication from the local DS-user on which kind of security procedure is to be used to
setup a secure dialogue exchange.
2.2.5.5.9.1 The Security Indicator parameter shall be one of the following values and
have a format of (8 bits / external / optional):

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
14
Value
Security Level
0
No security (default
value)
1
Secured dialogue
supporting key
management
2
Secured dialogue
3 – 255
Reserved
Note. – The absence of this parameter by the DS-User results in the security level being
set to the default value, i.e. no security.
2.2.5.5.10 Quality of Service
Note. – The Quality of Service (QoS) parameter is used to convey the DS-User quality of
service requirement which is a value corresponding to ATSC Routing Class and/or
Residual Error Rate (RER).
2.2.5.5.10.1 The QoS parameter shall have a format of (8 bits / external / optional) and
takes the following values:
1. The DS-User-provided ATSC Routing class as below:
Value
ATSC Routing Class
Description
0
No traffic type policy
preference
1
―A‖
2
―B‖
3
―C‖
4
―D‖
5
―E‖
6
―F‖
7
―G‖
8
―H‖
9 – 255
Reserved
2. The RER as defined below:
Value
RER Level
0
Low
1
Medium
2
High

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
15
3. ATN application priority may be indicated by inserting Differentiated Service
Codepoint (DSCP) values in the IPv6 header as described in Part III of this
document.
Note. – The priority is normally set by the network layer, so it is not necessary for the
application to provide it. The network layer can discern the priority by the port number
being used or IP address and set the differentiated service field accordingly. It should
also be noted that the network management procedures may lead to packet re-marking,
regardless of the initial application indications, to be consistent with local network
differentiated service definitions.
2.2.5.5.10.2 The UDP checksum may be activated for low or medium RER values and
not activated for a high RER value.
Note. – TCP checksums are always activated. The UDP checksums are activated by
default.
2.2.5.5.11 Result
Note. – The Result is set by the destination DS-User in order to indicate whether or not
the requested dialogue initiation or termination completed successfully.
2.2.5.5.11.1 The Result shall have the format of (8 bits / external / mandatory) and take
one of the values below:
Value
Definition
0
Accepted
1
Rejected (transient)
2
Rejected (permanent)
3 – 255
Reserved
2.2.5.5.12 Originator
Note. – The Originator indicates the source of a D-ABORT.
2.2.5.5.12.1 The Originator shall have the format of (8 bit / external / optional) and take
one of the values below:
Value
Definition
0
User (default)
1
Provider
2 – 255
Reserved
Note. – When this parameter is not provided by the DS-User the default value is assumed.

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
16
2.2.5.5.13User Data
Note. – The User Data contains the Packed Encoding Rules (PER) encoded application
data.
2.2.5.5.13.1 The User Data shall have the format of (UDP: 0 to 8184, TCP: variable size /
external / optional).
Note 1. – The maximum User Data size for a D-DATA service is the maximum UDP
datagram size (8192 bytes) reduced by the size of the ATNPKT header (8 bytes). For
other service primitives, the maximum User Data size needs to be adjusted based on the
size of the fixed header part plus the size of the variable length parts for that particular
service primitive.
Note 2. – The IPS DS will segment UDP datagrams with user data that exceeds 1024
bytes as described in 2.3.7 which will need to be reassembled by the receiver.
2.2.5.6 IPS DS Parameter Mapping
Note. – The IPS DS presents an identical interface of the ULCS to the ATN applications.
As such, the parameters of the IPS DS are identical to those of the ULCS. However,
there is a different mapping of the contents of those parameters. These modified
mappings are summarized in Table 5Table 5 and detailed for each primitive in Table
6Table 6.
Table 5. IPS DS - ULCS DS Parameter Mapping
DS Parameter
Visible to the DS-
User
IP Header
Transport
Protocol
Header
ATNPKT (See 00)
Comment
Called Peer ID
Called Peer ID
This can be an ICAO 24 bit aircraft
address or an ICAO Facility Designator (4
to 8 characters)
Called Sys-ID
Destination
Port Number
This is a registered port number assigned
to each ATN application (see 2.3.2)
Called Presentation
Address
Destination IP
Address
IP address of the recipient ATN
application
Calling Peer ID
Calling Peer ID
This can be an ICAO 24 bit aircraft
address or an ICAO Facility Designator (4
to 8 characters)
Calling Sys-ID
Source Port
Number
Using TCP, this port number is
dynamically assigned by the transport
protocol stack on the client side. With
UDP, this port number typically has a
static value which is the same as the
destination port number.
Calling Presentation
Address
Source IP
Address
IP address of the originator of the ATN
application
DS-User Version
Number
Content Version
This is the application‘s version number
Security
Requirements
Security
Requirements
00 – No security
01 – Secured dialogue Supporting Key
Formatted: Font: Italic
Formatted: Font: Italic

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
17
DS Parameter
Visible to the DS-
User
IP Header
Transport
Protocol
Header
ATNPKT (See 00)
Comment
Management
02 – Secured Dialogue
03 – Reserved
Quality of Service
Quality of Service
This parameter is to be transported only
when provided as ‗ATSC Routing Class‘;
the RER and Priority are not indicated
end-to-end but are optionally indicated to
the IPS DS and used locally
Result
Result
00 – Accepted
01 – Rejected (permanent)
02 – Rejected (transient)
Reject Source
00 – the remote DS-User
01 – the local DS-Provider
Provided locally in the Confirmation
primitive only; not transferred end-end
Originator
Originator
0 – User
1 – Provider (default)
2-255 – Reserved
User Data
User Data
This is the PER encoded data provided by
the application
2.2.5.6.1 The inclusion of optional ATNPKT parameters for each DS protocol message
shall comply with Table 6:
Table 6. ATNPKT Parameters for DS Protocol Messages
ATNPKT
Parameter
Protocol
message
D-START
D-
STARTCNF
D-DATA
D-UNIT-
DATA
D-END
D-ENDCNF
D-ABORT
D-ACK
D-
KEEPALIVE
Fixed part
ATNPKT Version
M
M
M
M
M
M
M
M
M
DS Primitive
M
M
M
M
M
M
M
M
M
Application Technology
Type
M
M
M
M
M
M
M
M
M
More
O
O
O
O
O
Presence Flag
M
M
M
M
M
M
M
M
M
Variable part
Source ID
M (4)
M (4)
(1)
Destination ID
M (4)
M (4)
M (4)
M (4)
M (2)
M
M
Sequence Numbers
UDP:M (4)
TCP:O(4)
UDP:M (4)
TCP:O(4)
UDP:M (4)
TCP:O(4)
UDP:M
TCP:O
UDP:M (4)
TCP:O(4)
UDP:M (4)
TCP:O(4)
UDP:M
TCP:O
UDP:M
TCP:O
UDP:M
TCP:O
Inactivity Time
O (3)
O (3)
Called Peer ID
O (3)
O
Calling Peer ID
O (3)
O
Content Version
O (3)
O (3)
O
Security Indicator
O (3)
O (3)
O
Quality Of Service
O (3)
Result
M (3)
M (3)
Originator
O
User Data
O (4)
O (4)
M (4)
M
O (4)
O (4)
O
Formatted Table
Comment [Q3]: Action 13-6

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
18
(O = optional, M = mandatory, empty = precluded to use)
(1) Source ID is present if D-ABORT is sent after D-START and before D-STARTCNF is received
(2) Destination ID is absent if D-ABORT is sent after D-START and before D-STARTCNF is received.
(3) For segmented messages this parameter is present only in the first segment.
(4) For segmented messages this parameter is present in all the segments
2.2.5.7 Dialogue Service Primitives
Note. – In order to provide the services identified in 2.2.4, the primitives listed in Table
7Table 7 are used. Each primitive may be either directly exposed to the DS-User
(request/response primitives) or reported to the DS-User by the DS-Provider
(indication/confirmation primitives).
Table 7. Dialogue Service Primitive Details
Interface Primitive
Dialogue Service Description
DS-User
DS-Provider
D-START req
Request to initiate a Dialogue with a peer DS-User
D-START ind
Inform a local DS-User that a peer DS-User requested for a
Dialogue initiation
D-START rsp
Complete a pending Dialogue initiation with either a positive or
a negative response
D-START cnf
Inform a local DS-User that the peer DS-User completed the
pending Dialogue initiation with either a positive or a negative
response
D-UNIT-DATA req
Send a datagram from the local DS-User to a peer DS-User (the
end-to-end delivery of the datagram is not guaranteed)
D-UNIT-DATA ind
Inform a local DS-User that a datagram is received from a peer
DS-User
D-DATA req
Send a datagram from the local DS-User to a peer DS-User
over an established Dialogue
D-DATA ind
Inform a local DS-User that a datagram is received from a peer
DS-User over an established Dialogue
D-END req
Request to terminate a Dialogue with a peer DS-User
D-END ind
Inform a local DS-User that a peer DS-User requested for a
Dialogue termination
D-END rsp
Complete a pending Dialogue termination with either a positive
or a negative response
D-END cnf
Inform a local DS-User that the peer DS-User completed the
pending Dialogue termination with either a positive or a
negative response
D-ABORT req
Request to abort a Dialogue with a peer DS-User
D-ABORT ind
Inform a local DS-User that the peer DS-User requested to
abort the Dialogue
D-P-ABORT ind
Dialogue aborted by the DS-Provider
2.2.5.8 Dialogue Service Time-Sequence Diagrams
Formatted: Font: Italic, English (U.S.)

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
19
Note. – The sections below illustrate the Dialogue Service protocol exchanges between
source and destination DS-Providers, including the ATNPKT user data part.
2.2.5.8.1 D-START service
Figure 4. D-START Service
2.2.5.8.2 D-DATA service
Note. – Figure 5Figure 5 shows the D-DATA service over a TCP connection. Due to the
nature of the connection, an ACK is not required. Figure 6Figure 6 shows the D-DATA
service over UDP. In order to provide explicit acknowledgment of the receipt of the
UDP packet, a D-ACK is returned by the receiver of the D-DATA ATNPKT.
Figure 5. D-DATA Service (TCP)
Formatted: Font: Italic, English (U.S.)
Formatted: Font: Italic, English (U.S.)

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
20
Figure 6. D-DATA Service (UDP)
2.2.5.8.3D-END service
Figure 7. D-END Service
2.2.5.8.4 D-ABORT service
Figure 8. D-ABORT Service

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
21
2.2.5.8.5 D-P-ABORT service
Note. – There is no ATNPKT format defined for the D-P-ABORT service, as it is a local
indication to the DS-User.
Figure 9. D-P-ABORT Service
2.2.5.8.6 D-UNIT-DATA service
Note. – Figure 10Figure 10 shows the D-UNIT-DATA service over a TCP connection.
Due to the nature of the connection, an ACK is not required. Figure 11Figure 11 shows
the D-UNIT-DATA service over UDP. In order to provide explicit acknowledgment of
the receipt of the UDP packet, a D-ACK is returned by the receiver of the D-UNIT-DATA
ATNPKT.
Figure 10. D-UNIT-DATA Service (TCP)
Formatted: Font: Italic
Formatted: Font: Italic

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
22
Figure 11. D-UNIT-DATA Service (UDP)
2.2.5.8.7 D-ACK service
Figure 12. D-ACK Service
2.2.5.8.8 D-KEEPALIVE service
Figure 13. D-KEEPALIVE Service

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
23
2.3 TRANSPORT LAYER
2.3.1Overview
2.3.1.1 The IPS DS has been designed to allow a user selection of either TCP or UDP for
the transport protocol. For simplicity, port-related operations are not considered as
primitives.
2.3.1.2 The transport layer primitives are given in Table 1.
Table 1. Transport Layer Primitives Used in the IPS DS
Transport Layer
Interface Primitive
Description
TCP
UDP
OPEN
Connection establishment (referred as 'active' on initiator side,
'passive' on the other side)
CLOSE
Connection termination (referred as 'active' on initiator side,
'passive' on the other side)
RECEIVE
Receive transport level datagram
SEND
Send transport level datagram
2.3.1.3 Table 2 gives the mapping to be applied between the Dialogue Service and the
Transport Layer primitives.
Table 2. Transport Layer - IPS DS Service Mapping
Dialogue Service
Transport Layer
Service
Interface Primitive
Interface Primitive
User Data
Protocol
Initialisation
OPEN (passive)
TCP
Dialogue Establishment
D-START
D-START req
OPEN (active)
TCP
SEND
D-START
TCP, UDP
D-START ind
RECEIVE
D-START
D-START rsp
SEND
D-
STARTCNF
D-START cnf
RECEIVE
D-
STARTCNF
Connectionless Data Exchange
D-UNIT-DATA
D-UNIT-DATA req
SEND
D-
UNITDATA
UDP
D-UNIT-DATA ind
RECEIVE
D-
UNITDATA
Connected-mode Data Exchange

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
24
Dialogue Service
Transport Layer
Service
Interface Primitive
Interface Primitive
User Data
Protocol
D-DATA
D-DATA req
SEND
D-DATA
TCP, UDP
D-DATA ind
RECEIVE
D-DATA
Orderly Dialogue Termination (user initiated)
D-END
D-END req
SEND
D-END
TCP, UDP
D-END ind
RECEIVE
D-END
D-END rsp
SEND
D-ENDCNF
CLOSE (passive)
TCP
D-END cnf
RECEIVE
D-ENDCNF
TCP, UDP
CLOSE (active)
TCP
Forced Dialogue Termination (user initiated)
D-ABORT
D-ABORT req
SEND
D-ABORT
TCP, UDP
CLOSE (active)
TCP
D-ABORT ind
RECEIVE
D-ABORT
TCP, UDP
CLOSE (passive)
TCP
Error-related Dialogue Termination (provider
initiated)
D-P-ABORT
D-P-ABORT ind
RECEIVE / SEND (failure)
TCP, UDP
Unexpected CLOSE (passive)
TCP
2.3.2 Port Numbers
2.3.2.1 The following TCP and UDP port numbers shall be used when supporting legacy
ATN applications over the ATN/IPS:
5910 Context Management
5911 Controller Pilot Data Link Communication
5912 Flight Information Services
5913 Automatic Dependent Surveillance
Note. – These port numbers are registered by IANA at
http://www.iana.org/assignments/port-numbers.
2.3.3 Providing Dialogue Service over UDP
Note. – UDP is mostly employed for applications requiring broadcast or multicast, but it
might also be used for simple "request-reply" applications provided that some reliability
is added at the highest levels. UDP does not guarantee the end-to-end service delivery of
the datagrams. For this reason, additional mechanisms are implemented in the IPS DS to
address UDP limitations; basically the truncation, loss, or duplication of UDP
datagrams. These mechanisms are specified in the following sections.

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
25
2.3.3.1 In order to add some reliability when acting over UDP, the DS-Provider shall
implement the mechanisms as described in Table 3:
Table 3. IPS DS UDP Reliability Mechanisms
Provide „dialog connection‟ over UDP
-identification of connections
- connection timeout
- termination timeout
M
O
O
Detect the loss of UDP datagrams using one-to-one acknowledgments (on a per connection
basis)
- retransmission timer + max retry count
- explicit ack nowledgment
-piggy-back ed ack nowledgment (max delay before ack )
M
M
O
Detect long-lived unpaired connections
-inactivity timer + k eep alive
M
Handle UDP datagrams truncation
- datagram segmentation / reassembly
M
(O = optional, M = mandatory)
2.3.4 Connection-ids
2.3.4.1 A pair of connection-ids, the Source ID and Destination ID, shall be assigned
during the connection phase (D-START / D-STARTCNF) by every participating DS peer
and used over any subsequent exchanges.
Note 1. – DS connection identification above UDP will be handled by the assignment of
this pair of connection-ids.
Note 2. – The 2 byte size for these identifiers was chosen because this will allow the DS-
Provider to associate a particular semantic to the dialogue-id assigned on its side
(without interference with the involved peer DS-User). In such a case, the identifier might
be an index in a context table, making it implicitly unique, but also allowing the receiving
DS-Provider to find out the context without having to use multiple search criteria and
parsing the whole table of contexts.
2.3.4.2 The Source ID and Destination ID shall be conveyed in the variable part of the
ATNPKT based on DS primitives as described in Table 4:
Table 4. Source ID and Destination ID Usage
DS Primitive field
Source ID
Destination ID
D-START
M
Identifier given by the DS-Provider
who initiates the dialogue; it will
allow him to find out the dialogue
context during the whole dialogue
duration.
-
Unassigned at this time

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
26
D-STARTCNF
M
Identifier given by the DS-Provider
who accepts the dialogue; it will
allow him to find out the dialogue
context during the whole dialogue
duration.
M
Identifier of the DS-Provider who
initiated the dialogue.
D-DATA
-
No need to transport it since it
would be meaningless for the
destination DS-Provider.
M
Identifier of the peer DS-Provider.
D-END
-
No need to transport it since it
would be meaningless for the
destination DS-Provider.
M
Identifier of the peer DS-Provider.
D-ENDCNF
-
No need to transport it since it
would be meaningless for the
destination DS-Provider.
M
Identifier of the peer DS-Provider.
D-ABORT before D-
STARTCNF
M
Identifier given by the DS-Provider
who initiated the dialogue.
-
Unknown for now.
D-ABORT other
cases
-
No need to transport it since it
would be meaningless for the
destination DS-Provider
M
Identifier of the peer DS-Provider.
(O = optional, M = mandatory)
2.3.5 Detecting Lost Datagrams
Note 1. – The loss of UDP datagrams is detected through a one-to-one acknowledgment
mechanism, on a per DS connection basis i.e. one data packet sent, one
acknowledgement to be received before more data can be sent again.
Note 2. – The acknowledgment may be piggy-backed with a dialogue message in the
reverse direction for the same dialogue; this will be possible for instance with confirmed
primitives.
2.3.5.1 For unconfirmed DS services, the receiving user shall use an explicit
acknowledgment by sending an ATNPKT with no data and with a specific value (D-
ACK) as 'DS Primitive'.
Note 1. – For acknowledgment purposes, the 'Sequence Numbers' field of the ATNPKT
variable part will be used.
Note 2. – This sequence number is required to avoid delivering duplicated data to the
peer DS-user following retransmission (i.e. if a D-ACK has been lost), and in more
exceptional circumstances, when UDP datagrams are delivered out of sequence by the
network.
2.3.5.2 The DS-Provider shall associate an incremented sequence number to outgoing
ATNPKTs and store the sequence number of the last ATNPKT received from the peer
DS-Provider in order to acknowledge it in a subsequent transmission.
2.3.5.3 Both outgoing and incoming sequence numbers shall be respectively carried by
the N(S) and N(R) subfields of the 'Sequence Numbers'.

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
27
Note 1. – N(S) corresponds to the current sequence number of the ATNPKT that has been
sent; N(R) is the next sequence number expected as N(S) from the remote DS-Provider
(i.e. in its next transmission).
Note 2. – Using sequence numbers will allow the DS-Provider to detect missing or
duplicated ATNPKTs. There is at most one unacknowledged ATNPKT; for this reason
there will be no grouped acknowledgments and there is no need to implement a selective
reject mechanism.
Note 3. – The lack of a timely acknowledgment will entail a retransmission. An excessive
number of retransmissions will break the DS connection. The timeout values and the
maximum number of retransmissions are detailed in Table 5Table 5.
2.3.6 Connection Timeout
Note. – In order to avoid long lived unpaired DS connections, a simple mechanism for
detecting inactivity is implemented. Both ends of the DS connection will transmit a
keepalive packet when the 'keepalive transmission timer' expires. The keepalive
transmission timer is restarted by the sender each time it sends data on the connection,
avoiding unnecessary keepalive transmissions.
2.3.6.1 A keepalive (an ATNPKT with no data and with a value of D-KEEPALIVE as
'DS Primitive') shall be sent at each expiry of the local keepalive transmission timer.
2.3.6.2 The keepalive transmission timer may be set to 1/3 of the inactivity timer of the
peer DS-Provider, or 1/3 of the default inactivity timer.
Note. – The lack of reception of either data or keepalive packets for an interval of time
corresponding to the inactivity time will break the DS connection. The parameter value
for this time is detailed in Table 5Table 5.
2.3.6.3 The optional ATNPKT field ‗Inactivity Time‘ may be used at dialogue
initialization time (i.e. in D-START and D-STARTCNF) so that each DS-Provider can
adjust its local keepalive transmission timer.
Note. – Absence of the Inactivity Time indicates use of the default Inactivity Time value
as in Table 5Table 5.
2.3.7 “More” Indicator
Note. – Most of the ATN application messages do not exceed 1000 bytes. Additionally the
suggested value of 1024 bytes does not exceed the IP payload (1500 bytes) in the
Ethernet frame (1518 bytes).
2.3.7.1 A D-DATA with a user data part exceeding 1024 bytes shall be segmented using
the 'MORE' bit reserved in the ATNPKT fixed part.
Formatted: Font: Italic
Formatted: Font: Times New Roman, Italic
Formatted: Font: Italic

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
28
Note. – Upon receipt of a D-DATA with the more bit set, the receiving side is responsible
for ordering and reassembling the segmented data.
2.3.8 DS-Provider Parameters
2.3.8.1 The values specified in Table 5 shall be applied to the identified DS-Provider
parameters:
Table 5. DS-Provider Parameters
Parameter
Min
Max
Default
Delay before retransmission
1 sec
60 sec
15 sec
Max number of transmissions
1
10
3
Inactivity time
3 min
15 min
4 min
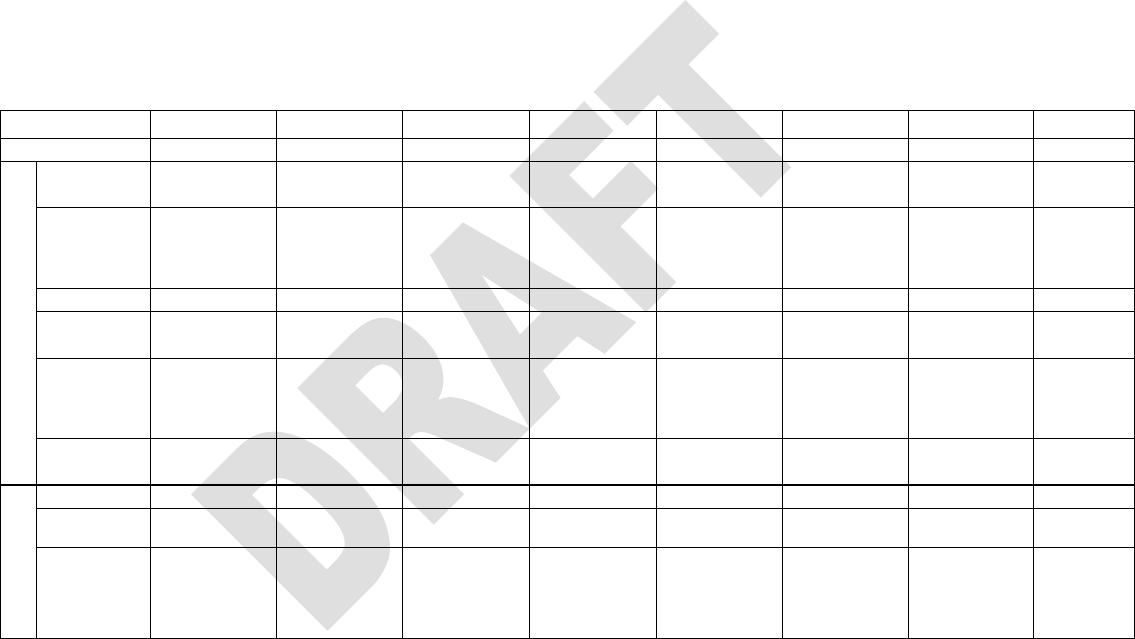
2.4 IPS DIALOGUE SERVICE STATE TABLES
2.4.1 IPS Dialogue Service TCP State Tables
Table 1. IPS DS State Table for TCP
Events State
D-IDLE
D-CONNECTED
D-START-SENT
D-START-RECEIVED
D-TRANSFER
D-END-SENT
D-END-RECEIVED
D-WAIT-CLOSE
During initialisation phase
- OPEN (passive)
DS-User events
D-START req
- OPEN (active) - Map D-
START req to D-START -
SEND (D-START) - Enter D-
START-SENT state
D-START rsp
- Map D-START cnf to D-
STARTCNF - SEND (D-
STARTCNF) - In case of
positive response : - Start tinact -
Enter D-TRANSFER state -
Otherw ise : -Enter D-WAIT-
CLOSE state
D-DATA req
- Map D-DATA req to D-DATA
- SEND (D-DATA)
D-END req
- Cancel tinact - Map D-END req
to D-END - SEND (D-END) -
Enter D-END-SENT state
D-END rsp
- Map D-END rsp to D-
ENDCNF - SEND (D-
ENDCNF) -In case of positive
response : -Enter D-WAIT-
CLOSE state - Otherw ise : -
Start tinact - Enter D-TRANSFER
state
D-ABORT req
- Map D-ABORT req to D-
ABORT - SEND (D-ABORT) -
Enter D-WAIT-CLOSE state
- Map D-ABORT req to D-
ABORT - SEND (D-ABORT) -
Enter D-WAIT-CLOSE state
- Cancel tinact - Map D-ABORT
req to D-ABORT - SEND (D-
ABORT) - Enter D-WAIT-
CLOSE state
- Map D-ABORT req to D-
ABORT - SEND (D-ABORT) -
Enter D-WAIT-CLOSE state
- Map D-ABORT req to D-
ABORT - SEND (D-ABORT) -
Enter D-WAIT-CLOSE state
TCP events
OPEN (passive)
completed
- Enter D-CONNECTED state
RECEIVE (D-START)
- Map D-START to D-START
ind - Report D-START ind to
DS-User - Enter D-START-
RECEIVED state
RECEIVE (D-
STARTCNF)
- Map D-STARTCNF to D-
START cnf - Report D-START
cnf to DS-User - In case of
positive response : - Start tinact -
Enter D-TRANSFER state -
Otherw ise : - CLOSE (active) -
Enter D-IDLE state

DRAFT ICAO Manual for the ATN using IPS Standards and Protocols (Doc 9896)
Draft Version 1819 AugustApril 3026, 201109
30
Events State
D-IDLE
D-CONNECTED
D-START-SENT
D-START-RECEIVED
D-TRANSFER
D-END-SENT
D-END-RECEIVED
D-WAIT-CLOSE
During initialisation phase
- OPEN (passive)
RECEIVE (D-DATA)
- Reset tinact - Map D-DATA to
D-DATA ind - Report D-DATA
ind to DS-User
RECEIVE (D-END)
- Cancel tinact - Map D-END to D-
END ind - Report D-END ind to
DS-User - Enter D-END-
RECEIVED state
RECEIVE (D-
ENDCNF)
- Map D-ENDCNF to D-END
cnf - Report D-END cnf to DS-
User - In case of positive
response : - CLOSE (active) -
Enter D-IDLE state - Otherw ise
: - Start tinact - Enter D-
TRANSFER state
TCP events
RECEIVE (D-ABORT)
- Map D-ABORT to D-ABORT
ind -Report D-ABORT ind to
DS-User - CLOSE (active) -
Enter D-IDLE state
- Cancel tinact - Map D-ABORT
to D-ABORT ind - Report D-
ABORT ind to DS-User -
CLOSE (active) - Enter D-IDLE
state
- Map D-ABORT to D-ABORT
ind - Report D-ABORT ind to
DS-User - CLOSE (active) -
Enter D-IDLE state
- Map D-ABORT to D-ABORT
ind - Report D-ABORT ind to
DS-User - CLOSE (active) -
Enter D-IDLE state
CLOSE (passive)
- CLOSE (active) - Enter D-
IDLE state
- Report D-P-ABORT ind to DS-
User - CLOSE (active) -Enter D-
IDLE state
- Report D-P-ABORT ind to DS-
User - CLOSE (active) -Enter D-
IDLE state
- Cancel tinact - Report D-P-
ABORT ind to DS-User -
CLOSE (active) - Enter D-IDLE
state
- Report D-P-ABORT ind to DS-
User - CLOSE (active) - Enter
D-IDLE state
- Report D-P-ABORT ind to DS-
User - CLOSE (active) - Enter
D-IDLE state
- CLOSE (active) - Enter
D-IDLE state
DS-Provider
events
tinact expires
- Report D-P-ABORT ind to DS-
User - Enter D-IDLE state

2.4.2 IPS Dialogue Service UDP State Tables
Table 2. IPS DS State Table for UDP
Events State
D-IDLE
D-START-SENT
D-START-RECEIVED
D-TRANSFER
D-END-SENT
D-END-RECEIVED
DS-User events
D-START req
-Map D-START req to D-
START - SEND (D-START) -
Start tconnect - Enter D-START-
SENT state
D-START rsp
- Map D-START cnf to D-
STARTCNF - SEND (D-
STARTCNF) -In case of positive
response : - Start tinact -Enter D-
TRANSFER state - Otherw ise : -
Enter D-IDLE state
D-DATA req
- Map D-DATA req to D-DATA
- SEND (D-DATA)
D-END req
- Cancel tinact -Map D-END req to
D-END - SEND (D-END) - start
tterm - Enter D-END-SENT state
D-END rsp
-Map D-END rsp to D-ENDCNF
- SEND (D-ENDCNF) - In case
of positive response : - Enter D-
IDLE state - Otherw ise : - Start
tinact - Enter D-TRANSFER state
D-ABORT req
- Cancel tconnect -Map D-ABORT
req to D-ABORT - SEND (D-
ABORT) - Enter D-IDLE state
- Map D-ABORT req to D-
ABORT - SEND (D-ABORT) -
Enter D-IDLE state
- Cancel tinact - Map D-ABORT
req to D-ABORT - SEND (D-
ABORT) - Enter D-IDLE state
- Cancel tterm - Map D-ABORT
req to D-ABORT - SEND (D-
ABORT) - Enter D-IDLE state
- Map D-ABORT req to D-
ABORT - SEND (D-ABORT) -
Enter D-IDLE state
UDP events
RECEIVE (D-START)
-Map D-START to D-START
ind - Report D-START ind to
DS-User - Enter D-START-
RECEIVED state
RECEIVE (D-
STARTCNF)
- Cancel tconnect -Map D-
STARTCNF to D-START cnf -
Report D-START cnf to DS-User
-In case of positive response : -
Start tinact - Enter D-TRANSFER
state - Otherw ise : - Enter D-
IDLE state
RECEIVE (D-DATA)
- Reset tinact - Map D-DATA to
D-DATA ind - Report D-DATA
ind to DS-User
RECEIVE (D-END)
- Cancel tinact -Map D-END to D-
END ind - Report D-END ind to
DS-User - Enter D-END-
RECEIVED state
RECEIVE (D-
ENDCNF)
- Cancel tterm -Map D-ENDCNF
to D-END cnf - Report D-END
cnf to DS-User - In case of
positive response : - Enter D-
IDLE state - Otherw ise : - Start
tinact - Enter D-TRANSFER state
RECEIVE (D-ABORT)
- Map D-ABORT to D-ABORT
ind - Report D-ABORT ind to
DS-User - Enter D-IDLE state
- Cancel tinact - Map D-ABORT to
D-ABORT ind - Report D-
ABORT ind to DS-User - Enter
D-IDLE state
- Cancel tterm - Map D-ABORT to
D-ABORT ind - Report D-
ABORT ind to DS-User - Enter
D-IDLE state
- Map D-ABORT to D-ABORT
ind - Report D-ABORT ind to
DS-User - Enter D-IDLE state
D S events
tconnect expires
- Report D-P-ABORT ind to DS-
User - Enter D-IDLE state
tinact expires
- Report D-P-ABORT ind to DS-
User - Enter D-IDLE state
tterm expires
-Report D-P-ABORT ind to DS-
User - Enter D-IDLE state
32
ICAO
Aeronautical Telecommunication Network (ATN)
Manual for the ATN using IPS Standards and
Protocols (Doc 9896)
Part III
Guidance Material Section

1
TABLE OF CONTENTS
1.0 INTRODUCTION ....................................................................................................... 2
1.1 BACKGROUND .............................................................................................................. 46
2.0 GENERAL GUIDANCE .......................................................................................... 57
2.1 THE ATN/IPS ............................................................................................................... 57
2.1.1 The ATN/IPS Internetwork .............................................................................. 57
2.1.2 Coordination of Policies among Administrative Domains.............................. 79
2.1.3 ATN/IPS Internetworking with Mobility .......................................................... 79
2.2 NETWORK TRANSITION MECHANISMS ..................................................................... 810
2.2.1 Tunnelling ...................................................................................................... 911
2.2.2 Dual Stack ................................................................................................... 1012
2.2.3 Translation .................................................................................................. 1012
2.2.4 Combining of the Mechanisms .................................................................... 1113
3.0 PROTOCOL STACK ........................................................................................... 1113
3.1 PHYSICAL AND LINK LAYER GUIDANCE ................................................................ 1113
3.2 NETWORK LAYER ................................................................................................... 1113
3.2.1 Address Plan ................................................................................................ 1113
3.2.2 Application interface to the network layer .................................................. 1113
3.2.3 Inter-domain routing ................................................................................... 1113
3.2.4 Multicast ...................................................................................................... 1315
3.3 TRANSPORT LAYER ................................................................................................. 1416
3.3.1 Transmission Control Protocol ................................................................... 1416
3.3.2 User Datagram Protocol (UDP) ............................................................... 1517
3.3.3 Transport Layer Addressing ........................................................................ 1517
3.3.4 Application Interface to the Transport Layer .............................................. 1517
3.3.5 Congestion Avoidance ................................................................................. 1618
3.3.6 Error Detection and Recovery .................................................................... 1618
3.3.7 Performance Enhancing Proxies (PEPs) .................................................... 1618
3.3.8 Transport Layer usage ................................................................................ 1618
3.4 APPLICATION LAYER ................................................................................................ 1820
3.4.1 ASN.1 extensions to CM ........................................................................... 1820
4.0 QUALITY OF SERVICE ..................................................................................... 2022
4.1 INTRODUCTION ......................................................................................................... 2022
4.2 CLASS DEFINITIONS .................................................................................................. 2022
4.2.1 Context ......................................................................................................... 2022
4.2.2 ATN/IPS PHBs/CoS ..................................................................................... 2123
4.2.3 DiffServ Code Point (DSCP) Values ........................................................... 2325
4.2.4 Traffic Characterisation .............................................................................. 2426
5.0 MOBILITY GUIDANCE ..................................................................................... 2426
5.1 MOBILE IPV6 ......................................................................................................... 2426
5.1.1 MIPv6 Bidirectional Tunneling ................................................................... 2527
5.1.2 MIPv6 Route Optimization .......................................................................... 2527
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed

2
5.2 ENHANCEMENTS TO MIPV6 ...................................................................................... 2628
5.2.1 Heirarchical Mobile IPv6 (HMIPv6) .......................................................... 2628
5.2.2 Fast Handovers for Mobile IPv6 (FMIPv6) ................................................ 2628
5.2.3 Proxy Mobile IPv6 (PMIPv6) ...................................................................... 2729
5.2.4 Network Mobility (NEMO) .......................................................................... 2729
6.0 SECURITY GUIDANCE ...................................................................................... 2830
6.1 REQUIRMENTS FOR IMPLEMENTATION ...................................................................... 2830
6.2 GROUND-GROUND SECURITY ................................................................................... 2830
6.2.1 Ground-Ground IPsec ................................................................................. 2830
6.2.2 Ground-Ground IKEv2 ................................................................................ 2931
6.2.3 Alternatives to IPsec/IKEv2 for Ground-Ground Security ......................... 2931
6.3 AIR-GROUND SECURITY ........................................................................................... 2931
6.3.1 Air-Ground IPsec ........................................................................................ 2931
6.3.2 Air-Ground IKEv2 ....................................................................................... 3032
6.3.3 Securing Air-Ground End-to-End Communications ................................... 3133
6.3.4 Securing Access Network and Mobile IP Signaling .................................... 3435
6.3.5 Public Key Infrastructure Profile and Certificate Policy ........................... 3536
6.3.6 General Guidance for Implementation of Security ..................................... 3536
7.0 VOICE OVER INTERNET PROTOCOL (VOIP) ............................................ 3637
7.1 EUROCAE SPECIFICATION ................................................................................ 3637
7.2 ADDITIONAL INFORMATION............................................................................ 3738
7.2.1 STANDARDS AND PROTOCOLS ............................................................................... 3738
7.2.1.1 H323 ......................................................................................................... 3738
7.2.1.2 MGCP/MEGACO ........................................................................................... 2
8.0 IPS IMPLEMENTATIONS ....................................................................................... 1
8.1 OLDI .............................................................................................................................. 1
8.2 FLIGHT MANAGEMENT TRASFER PROTOCOL (FMTP) .................................................... 1
8.2.1 Testing OLDI/FMTP ......................................................................................... 2
8.3 AMHS ............................................................................................................................ 2
APPENDIX A – REFERENCE DOCUMENTS ............................................................. 3
APPENDIX B – ABBREVIATIONS/DEFINITIONS.................................................... 1
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed
Field Code Changed

3
FOREWORD
The material contained in this document supplements the Standards and Recommended Practices
(SARPs) and the Manual for Detailed Technical Specifications. This document is to be used to assist in
the deployment of IPS systems of the Aeronautical Telecommunication Network (ATN) as defined in
Annex 10 — Aeronautical Telecommunications, Volume III — Communication Systems and Part I — Digital
Data Communication Systems.
Field Code Changed

4
1.0 Introduction
This part of the manual contains information to assist ICAO contracting States in the deployment of an
ATN/IPS network to support Air Traffic Management (ATM) services. The following minimum core
services should be provided by ATN/IPS network.
These core services enable ATN applications to provide voice and data services with the appropriate
priority and security over the ATN/IPS network.
The protocols discussed in this document are based on the open system interconnect reference model
(OSI). As the ATN/IPS uses the 4 layer model of the IETF, Figure 1.1 depicts the relationship between
OSI, ATN/OSI and the ATN/IPS protocols.
Figure 1.1 Protocol Reference Model
1.1 Background
The ICAO ATN/IPS has been established with the specific goal of providing global ATM services
based on commercial off-the-shelf technologies. According to the ICAO SARPS, ATN services can be
provided using the ISO based ICAO protocols as specified in Doc 9705/9880 or the ATN/IPS as
Application Layer 7
Session Layer 5
Transport Layer 4
Network Layer 3
Link Layer 2
Physical Layer 1
Presentation Layer 6
OSI Reference Model
ATN ISO Protocols
ATN IPS
Fast-byte
ATN Applications
(e.g., CMIP, X.400)
Transport Layer
Class 4
Fast-byte
Physical Layer (e.g.,
FDDI, 802.X)
LLC/MAC
IPv6 & ICMPv6
TCP/UDP
Consolidated
Application
Services (e.g.,
SMTP, SNMPv3,
FTP, X.400 and
Telnet)
LAP B (HDLC)
Physical Layer (e. g.,
EIA-232, V.35, X.21)
SNDCF
ES-IS/CLNP
X.25 PLP
5
specified in this manual, Doc 9896. This manual describes the technical approach for networking based
on IPS, and will enable ICAO contracting States to provide ATM services on its basis.
2.0 General Guidance
This section contains general guidance information about the implementation of ATN/IPS for ATN
applications, multicast and VoIP.
2.1 THE ATN/IPS
2.1.1 The ATN/IPS Internetwork
The ATN/IPS Internetwork is specifically and exclusively intended to provide data communications
services to air traffic service (ATS) provider organizations and aircraft operating agencies supporting
the following types of communications traffic:
ATS Communication (ATSC). Communication related to air traffic services including air
traffic control, aeronautical and meteorological information, position reporting and services
related to safety and regularity of flight. This communication involves one or more air traffic
service administrations.
Aeronautical Operational Control (AOC). Communication required for the exercise of authority
over the initiation, continuation, diversion or termination of flight for safety, regularity and
efficiency reasons.
Aeronautical Administrative Communication (AAC). Communication used by aeronautical
operating agencies related to the business aspects of operating their flights and transport
services. This communication is used for a variety of purposes, such as flight and ground
transportation, bookings, deployment of crew and aircraft or any other logistical purposes that
maintain or enhance the efficiency of over-all flight operation.
In order to support these communications types, this manual specifies a set of technical and
administrative requirements on the entities which constitute the ATN/IPS. See Figure 2.1-1.
Technical requirements in this manual are levied against an IPS router, an IPS host, or an IPS node
when the requirement applies to both. This manual adopts the RFC 2460 definition of an IPS node as a
device that implements IPv6 and distinguishes between an IPS router as a node that forwards IP packets
to others, and an IPS host as a node that is not a router.
Administrative requirements in this manual are levied against Administrative Domains. An
Administrative Domain is an organizational entity and can be an individual State, a group of States
(e.g., an ICAO Region or a regional organization), an Air Communications Service Provider (ACSP),
an Air Navigation Service Provider (ANSP), or other organizational entity that manages ATN/IPS
network resources and services.

6
The primary requirement is that each Administrative Domain participating in the ATN/IPS
internetwork must operate one or more IPS routers which execute an inter-domain routing protocol
called the Border Gateway Protocol (BGP). This is essentially so that the ATN/IPS can be formed
across the various Administrative Domains whereby any IPS host can reach any other IPS host in the
ATN/IPS internetwork.
IPS
Router
IPS
Router
IPS
Router
IPS
Host
IPS
Host
IPS
Host
IPS
Router
IPS
Router
IPS
Router
IPS
Host
IPS
Host
IPS
Host
IPS
Router
IPS
Router
IPS
Router
IPS
Host
IPS
Host
IPS
Host
ATN/IPS
Internetwork
ATN/IPS
Internetwork
ATN/IPS
Internetwork
ATN/IPS
Internetwork
AD
AD
AD
AD
AD
AD
AD
AD
AD
AD
AD
AD
Figure 2.1-1 – The ATN/IPS Internetwork
An inter-domain routing protocol is used to exchange routing information among Autonomous
Systems. An Autonomous System, as defined in RFC 1930, is a connected group of one or more IP
prefixes run by one or more network operators which has a single and clearly defined routing policy.
From this definition we see two distinct entities: one is the AS as a group of IP prefixes and the other is
the network operators, i.e., the Administrative Domains. This distinction is meaningful in the Internet
since it permits multiple organizations (i.e., Administrative Domains) to run BGP to an Internet Service
Provider (ISP) which in turn connects each of these organizations to the Internet. This manual does not
preclude using ISPs in this fashion; however, as noted above, requirements are levied directly on the
Administrative Domains.
7
2.1.2 Coordination of Policies among Administrative Domains
IPS routers will exchange information about their internal network prefixes with their immediate
neighbor routers but may also forward routing information about other network prefixes learned from
other BGP neighbors. As a result, traffic between two Administrative Domains may be relayed by a
number of intermediate Administrative Domains. Such traffic being carried on behalf of two others is
termed transit traffic.
This manual does not specify which routes are to be advertised between IPS routers nor basic traffic
management policies for a dynamically routed environment. Administrative Domains however are
required to coordinate their policy for carrying transit traffic with peer Administrative Domains.
Administrative Domains that participate in the ATN/IPS should ensure the proper handling of transit
traffic on the following basis:
An Administrative Domain should not advertise a network prefix if it is not prepared to accept
incoming traffic to that network prefix destination;
When establishing the interconnections between two Administrative domains a charging
mechanism may be agreed to support implicit corresponding transit policy;
Administrative Domains that relay transit traffic should ensure that the associated security and
QoS policies of the traffic is maintained
2.1.3 ATN/IPS Internetworking with Mobility
The fixed or ground-ground ATN/IPS described in section 2.1.1 may be extended to support mobility,
that is, it may be extended to support air-ground communications. This is accomplished through the
use of Mobile IPv6, the IETFs general mobility solution. Mobile IPv6 permits mobile nodes (MN)
(i.e., aircraft in the ATN/IPS) to communicate transparently with correspondent nodes (CN) (i.e.,
ground automation systems in the ATN/IPS) while moving within or across air-ground networks. An
Administrative Domain in the ATN/IPS which offers Mobile IPv6 service is called a Mobility Service
Provider (MSP). Thus the ATN/IPS is extended to support mobility through the addition of MSPs
providing mobility service to mobile nodes. Figure 2.1-2 depicts the ATN/IPS with a Mobility Service
Provider. As is shown in this figure in order to provide mobility service, the MSP must operate one or
more home agents. The home agent provides a key role in that on one side it provides location
management to keep track of the movement of a mobile node and to locate the mobile node for data
delivery, while on the other side it operates as an inter-domain router providing connectivity to the rest
of the ATN/IPS (Note that this is a logical view. Different physical configurations are possible in
actual implementations.). It should be noted that Mobile IPv6 RFC 3775 is being updated by the IETF
(RFC 3775bis). Implementation of RFC 3775 should take those updates into account.
Figure 2.1-2 shows the minimal configuration, e.g., for ATSC, where the MSP might be an ACSP.
However, this is not the only possible configuration. An ANSP may choose to become its own MSP
and obtain access service from an ACSP. To support AOC and AAC an Airline may likewise become
an MSP. Similarly, an Airport Authority may decide to become a MSP and offer service to the
ATN/IPS. In this case IP layer mobility service may be offered along with or in addition to link layer

8
mobility. As noted in section 2.1.1, the ATN/IPS is intended to support ATSC, AAC, and AOC.
However, the mobility approach may be used by other aviation organizations. These organizations may
become MSPs and support other types of communications such as Airline Passenger Communications
(APC). In this case an enhanced form of Mobile IP service called Network Mobility (NEMO) may be
offered. The enhanced forms of Mobile IP listed in section 5.2 may be offered to support all types of
communications traffic.
Home
Agent
Access
Router
Access
Router
Correspondent
Node
Correspondent
Node
Correspondent
Node
Correspondent
Node
Correspondent
Node
Correspondent
Node
ATN/IPS
Internetwork
AD
AD
Mobility
Service
Provider
(MSP)
MIPv6
Mobile Node
2.2 Network Transition Mechanisms
IPv6 has been adopted by the IETF and the internet authorities to cope with the ever increasing growth
rate of the global internet. IPv6 solves many of the technical problems associated with IPv4, in
particular the limited IPv4 address space.
Comment [Q4]: Action 13-05
9
The global implementation of IPv6 has already begun, and even within ICAO regions to support Air
Traffic Management applications. It is the building block of the next generation internet which will
enable a flexible means to roll-out new technologies and services. For this reason, the ATN/IPS is
based on IPv6 to take immediate advantage of new commercial off-the-shelf products and technologies.
The implementation of the ATN/IPS will be gradual over a significant period of time. Many
organizations will be required to go through multiple steps to ensure that ATN/IPS end-systems and
routers are integrated into their existing environment in particular for those that have deployed legacy
AFTN, AFTN/CIDIN, X.25, ATN/OSI CLNP (primarily CLNP over Ethernet or ―X.25‖) and IPv4
systems.
Three transitions mechanisms can assist organisations deploying the ATN IPS in a heterogeneous
environment:
o Tunnelling: one protocol being encapsulated in another
o Dual stack: an environment in which multiple protocols operate simultaneously
o Translation: the conversion from one protocol to another
An in-depth description of the first two mechanisms can be found in RFC 4213 (Basic Transition
Mechanisms for IPv6 Hosts and Routers). The applicability of above three mechanisms to the ATN/IPS
are further described.
2.2.1 Tunnelling
IPv6 has been specified to operate over a variety of lower layer interfaces such as Frame Relay, ATM,
HDLC, PPP and LAN technologies. Tunneling implies that a given protocol is encapsulated into
another, meaning that IPv6 would be encapsulated into another functionally equivalent network
protocol. With regard to the ATN/IPS, the key benefit of this mechanism would be for aeronautical
organizations that already operate IPv4 networks to allow the ATN/IPS hosts and routers communicate
between each other over such an underlying IPv4 network. Furthermore, if the interconnecting
infrastructure between two ATN/IPS administrative domains is limited to IPv4, this mechanism can be
applied.
It is recalled that IPv6 cannot operate over X.25; an IPv6 tunnel over IPv4 can be in turn tunneled over
an X.25 network. A specific tunneling mechanism termed IP SNDCF is defined for ATN/OSI
applications, it is to be noted that this enables interoperability between ATN/OSI applications over an
IP network but does not enable interoperability with ATN/IPS applications.
Tunneling mechanisms lead to an increase of protocol overhead and the segregation of the two routed
domains creates additional network management e.g. an IPv6 routed domain over an underlying IPv4
routed domain that needs to be managed in terms of QoS, security, and route optimization. In addition,
this mechanism only foresees interoperability between ATN/IPS systems as it does not enable
interoperability between ATN/OSI systems nor other IPv4 systems within the organization.
Nevertheless, it may provide an effective way to enable the ATN/IPS within and between two
administrative domains.
10
The tunneling mechanism is best suited to resolve lower layer communication issues between ATN/IPS
IPv6 hosts and routers but does not provide interoperability with non-compliant ATN/IPS systems.
2.2.2 Dual Stack
The dual stack mechanism implies that an implementation handles more than one communications
protocol for a given application or function. Within the internet domain a significant number of
communication applications have been dual stacked e.g. HTTP, FTP, SSH, DNS, SMTP etc. by
supporting both IPv4 and IPv6 protocols. However, in the context of the ATN/IPS the purpose of dual
stacking is to resolve similar yet different issues.
The concept of dual stacking is ideally suited for systems that need to support ATN applications for
both OSI and IPS. In such environments, the applications are designed in an abstract fashion to be
independent of the lower layers, in other words they are unaware which lower layer communications
protocol (OSI or IP) is being used to communicate with their peer. X.400 vendors have taken this
approach to support both OSI and IP environments avoiding the need to develop complex ad-hoc lower
layer communication gateways. Usually such implementations rely on some form of directory or
lookup table associating a high-level address with a specific communications protocol address.
The concept of dual stack can be extended to multiple stack, e.g. IPv4, IPv6, X.25. ATN AMHS
manufacturers usually support operation over multiple protocols such as OSI, TCP/IP and X.25.
The dual stack mechanism is best suited to provide the maximum level of interoperability with peers
while reducing the complexity of lower layer communication protocol gateways and additional single
points of failure. It is ideally suited for applications such as AMHS whereby some systems have
already been implemented on the basis of OSI and others on TCP/IP. A dual stack approach can be a
valid for air-ground data link ground systems to support CPDLC over multiple data link services such
as ATN/OSI and ATN/IPS.
2.2.3 Translation
Translation mechanisms imply the conversion from one protocol to another. This mechanism can be
interpreted as a lower layer communications gateway between two protocols that share a high degree of
commonality. Several translators such as RFC 2766 - Network Address Translation - Protocol
Translation (NAT-PT), have been developed in the context of the transition from IPv4 to IPv6 as both
versions share a number of common features.
Within the overall transition from IPv4 to IPv6, it was envisaged that some systems may be only
capable of communicating with IPv4 and others with IPv6. Considering global internet scalability
issues and the fact that most internet applications and systems have become dual stacked, the need for
translators has declined.
However, translators may play an important short-term role in the case of the ATN/IPS. For example,
although existing AMHS systems operate on dual stack operating systems, none of them have upgraded
their application code to make use of IPv6. In other words, RFC 1006 is supported but not RFC 2126.
In such particular cases and in view of the limited number of systems, the deployment of translators
11
provides a short-term measure for such systems to comply with the ATN/IPS and inter-work with RFC
2126 enabled systems.
IPv4/IPv6 translators increase the complexity of the IP infrastructure and its management. A dual stack
approach is to be preferred but in specific cases translators may be the only short-term measure to
provide compliance with the ATN/IPS.
2.2.4 Combining of the Mechanisms
As the ATN/IPS implementation will be gradual it is understandable that a combination of the above
three mechanisms will be applied.
Specific combinations of the above mechanisms can be deployed to better fit within the environment of
the administrative domain environment.
3.0 PROTOCOL Stack
3.1 Physical and Link Layer Guidance
Physical and link layer issues will be determined by the required service and member state connections.
The physical and link layer issues will be on service need basis and should be contained in a
memorandum of agreement (MOA).
3.2 Network Layer
The ATN/IPS makes use of IPv6, which uses 128 bit addresses versus 32 in IPv4. IPv6 prefixes are
exchanged between Administrative Domains using static routes or BGP to ensure global ATN/IPS
routing.
3.2.1 Address Plan
Unlike IPv4, there is no notion of private addresses within IPv6. Similar to existing practices for X.25,
each Administrative Domain will require to develop an IPv6 addressing plan, refer to Part I, 2.3.3
Network Addressing. This will involve the receipt of a unique IPv6 prefix and assignment procedures
to networks and hosts.
3.2.2 Application interface to the network layer
Although applications generally interface to the communication service at the transport layer, it is
sometime necessary to transmit and receive datagrams at the network level. This is granted by some
socket API extensions specified in: RFC 3542 - Advanced Sockets Application Program Interface
(API) for IPv6.
3.2.3 Inter-domain routing
12
Inter-domain routing allows the exchange of IPv6 prefixes between Administrative Domains. These
exchanges are supported by the configuration of static routing or the border gateway protocol (BGP)
between ATN/IPS routers to ensure global ATN/IPS routing.
Depending on the scale of the Administrative Domain, further internal levels of inter- and intra-domain
routing or BGP federations may exist.
3.2.3.1 AS numbering plan
AS numbers need to be assigned and configured in ATN/IPS routers to announce their autonomous
systems within the routed domain. The AS numbering plan is presented in Part I, Appendix A.
3.2.3.2 ATN/IPS Router Ids
In order to establish BGP between two neighbours, each BGP peer must define a router id. If two
routers make use of the same router-id value, BGP sessions cannot be established. As the router id is a
32 bit field, it is usually on the IPv4 address of the router.
As ATN/IPS routers may not have IPv4 interfaces or unique IPv4 addresses, a scheme needs to be
recommended. Although global uniqueness of these values is not a pre-requisite, to ease
implementation of the ATN/IPS the following scheme is recommended (based on draft-dupont-durand-
idr-ipv6-bgp-routerid-01.txt):
o 4 bits set to one, 16 bits set to the AS number (the global AS number plan is in Part I, Appendix A)
o 12 bits manually allocated within the domain. (allows for 4096 different router IDs in each routing
domain)
3.2.3.2.1 Routing Advertisement
ATN/IPS routers should advertise network prefixes based on consistent prefix lengths or aggregate
route prefixes;
3.2.3.2.2 Traffic type segregation
BGP-4 does not natively allow setting up different set of routes for different traffic to the same
destination. ATN/IPS requirement on traffic type segregation may be fulfilled by appropriate
provisions in the ATN addressing plan: if the ATN address incorporates an indication of the traffic
type, BGP-4 will transparently flood segregated route information for the various traffics.
3.2.3.2.3 Traffic Priority and Differentiated Service
Historically, network layer priority was selected explicitly by the sending application through the TOS
field. Although Differentiated Service (RFC 2474) preserves the IP precedence semantic of the TOS
field, this approach is now deprecated. This is partly because the IP precedence has been superseded by
the Per-Hop-Behaviour (PHB) strategy of Differentiated service, but also because network
administrators usually don‘t trust application settings.

13
Differentiated Service (RFC 2474) provides a mean for specifying and implementing QOS handling
consistently in the ATN/IPS network. This specification is made on a per node basis, specifying
behaviour of individual nodes concerning QOS (Per Hop behaviour). The general framework / current
practices is depicted in details in: RFC 2475 - Architecture for Differentiated Services.
Refer to the QoS section 4.
3.2.4 Multicast
The need to send the same information to multiple receivers is one of the main requirements of
surveillance data distribution. This requirement can be supported by the Internet Protocol versions 4
and 6 (IPv4 and IPv6 respectively) multicast services. Other networking techniques that achieve the
same multicast objective are not further considered within the scope of this document.
A limited number of ICAO Contracting States have deployed national IPv4 multicast services for
surveillance data distribution. However, the limited range of the IPv4 multicast address space and the
absence of gateways between IPv4 and IPv6 multicast inhibits a scalable deployment for the ATN/IPS.
In recent years, significant technical progress has been made in the field of IP multicast, namely source
specific multicast (SSM). Contrary to existing deployments on the basis of PIM-SM (Protocol
Independent Multicast—Sparse Mode), SSM provides added simplicity and resiliency to the routing of
IP multicast traffic and is ideally suited for surveillance needs.
It‘s use over IPv6 is recommended in a Eurocontrol guideline entitled ―EUROCONTROL Guidelines
for Implementation Support (EGIS) Part 5: Communication & Navigation Specifications, Chapter 12,
Surveillance Distribution over IP Multicast Profile Requirement List (PRL)‖ available at
http://www.eurocontrol.int/communications/public/standard_page/com_network.html.
A source specific multicast (SSM) data channel is defined by the combination of destination multicast
address and source unicast address. This corresponds to a single surveillance data flow made available
from a specific source in the ATN/IPS.
Figure 4.1 SSM Multicast IPv6 address with global scopeIPv6
| 8 | 4 | 4 | 8 | 8 | 64 | 32 |
+--------+----+----+--------+--------+----------------+----------+
|11111111|0011|1110|00000000|00000000| 000……………………000 | group ID |
+--------+----+----+--------+--------+----------------+----------+
The IPv6 multicast group ID shall be in the range 0x8000000 to 0xFFFFFFFF allowed for dynamic
assignment by a host, as specified in RFC 3307 section 4.3 and RFC 4607 section 1.
The resulting available IPv6 SSM address range is FF3E::8000:0/97 (FF3E:0:0:0:0:0:8000:0 / 97).
Assuming the appropriate access to the service, to receive a SSM (source specific multicast) stream one
requires the following three parameters:
1. Source-address (unicast address)
Field Code Changed
14
2. Multicast address (as indicated by the source application)
3. Port (default is 8600 for ASTERIX surveillance data in Europe)
3.3 Transport Layer
The transport layer protocols are used to provide reliable or unreliable communication services over the
ATN/IPS. There are two mandatory transport protocols, TCP and UDP. TCP is used to provide reliable
transport services and UDP is used to provide best effort service. Other transport protocols may be
used but can not affect ATN/IPS communications or services.
3.3.1 Transmission Control Protocol
The Internet Protocol (IP) works by exchanging groups of information called packets. Packets are short
sequences of bytes consisting of a header and a body. The header describes the packet's routing
information, which routers on the Internet use to pass the packet along in the right direction until it
arrives at its final destination. The body contains the application information. TCP is optimized for
accurate delivery rather than timely delivery, TCP sometimes incurs long delays while waiting for out-
of-order messages or retransmissions of lost messages, and it is not particularly suitable for real-time
applications like Voice over IP (VoIP). Real time applications will require protocols like the Real-time
Transport Protocol (RTP) running over the User Datagram Protocol (UDP).
TCP is a reliable stream delivery service that guarantees to deliver a stream of data sent from one host
to another without duplication or losing data. Since packet transfer is not reliable, a technique known as
positive acknowledgment with retransmission is used to guarantee reliability of packet transfers. This
fundamental technique requires the receiver to respond with an acknowledgment message as it receives
the data. The sender keeps a record of each packet it sends, and waits for acknowledgment before
sending the next packet. The sender also keeps a timer from when the packet was sent, and retransmits
a packet if the timer expires. The timer is needed in case a packet becomes lost or corrupt.
In the event of congestion, the IP can discard packets, and, for efficiency reasons, two consecutive
packets on the internet can take different routes to the destination. Then, the packets can arrive at the
destination in the wrong order.
The TCP software library use the IP and provides a simpler interface to applications by hiding most of
the underlying packet structures, rearranging out-of-order packets, minimizing network congestion, and
re-transmitting discarded packets. Thus, TCP very significantly simplifies the task of writing network
applications.
TCP provides a connection-oriented service with a reliable semantic. It operates above the network
layer which does not necessarily detect and report all errors (e.g. corruption, misrouting). For this
purpose, it provides:
· Error detection based on a checksum covering the transport header and payload as well as some
vital network layer information.
· Recovery from error based on retransmission of erroneous or lost packets.
15
TCP is also designed to detect and manage end-to-end network congestion and maximum user data
segment sizes. This is essential for operation over heterogeneous sub networks with some low
bandwidth and high latency trunks, such as the actual ATN/IPS Air/Ground sub networks.
3.3.2 User Datagram Protocol (UDP)
UDP provides a connectionless service with limited error detection and no recovery, nor congestion
management mechanisms. It is naturally dedicated for light data exchanges, where undetected
occasional loss or corruption of packets is acceptable, and when simplicity of use is a goal.
3.3.3 Transport Layer Addressing
Transport layer addressing relies on port numbers (16 bits integer values) that are associated with
source and destinations endpoints to identify separate data streams.
Ports are classified in three categories with associated range of values:
· Well-known ports are those from 0 through 1023 and are assigned by IANA. On most systems
these ports can only be used by system (or root) processes or by programs executed by
privileged users. Such pre-defined well-known port numbers associated to distinct TCP and/or
UDP applications makes them visible (―well-known‖) to client applications without specific
knowledge or configuration.
· Registered ports are those from 1024 through 49151 and are registered by IANA following user
request. Essentially such ports play the same role as well-known ports but for less critical or
widespread applications. The use of such ports does not require specific privileges.
· Dynamic and/or private ports are those from 49152 through 65535. They may be used freely by
applications.
Port assignment is obtained on request to IANA. An up-to-date image of the port registry is available
at:
http://www.iana.org/assignments/port-numbers
This assignment plan is compulsory over the public Internet. It should be made applicable to ATN/IPS
(at least concerning well-known ports) in order to avoid any conflict.
Furthermore, ATN/IPS hosts are required to supporting the following registered port numbers:
· tcp 102 for ATSMHS
· tcp 8500 for FMTP
· tcp/udp 5910 for CM
· tcp/udp 5911 for CPDLC
· tcp/udp 5912 for FIS
· tcp/udp 5913 for ADS
3.3.4 Application Interface to the Transport Layer
16
The application interface to the TCP and UDP transport layers is provided consistently on a wide range
of platform/operating systems according to the specification made in: RFC 3493 - Basic Socket
Interface Extensions for IPv6. This RFC extends the socket interface (originally developed by the
Berkeley University for supporting IPv4 in their BSD Unix distribution) to IPv6.
3.3.5 Congestion Avoidance
In order to adapt to variables conditions for draining traffic in sub networks, TCP implements basically
4 mechanisms: slow-start, congestion-avoidance, fast-retransmit and fast-recovery. These are specified
in: RFC 2581 - TCP Congestion Control. The two first mechanisms aim at preventing important loss of
packets when congestion occurs, while the two others attempt to shorten the delay for retransmitting the
lost packets. These mechanisms are implemented independently in every end system; they don‘t
completely avoid loss of packets.
In the case of low bandwidth sub networks (e.g. ATN Air/Ground sub networks), TCP applications
may make use of the Explicit Congestion Notification mechanism will more likely provide a significant
benefit. It is specified by: RFC 3168 - The Addition of Explicit Congestion Notification (ECN) to IP.
This feature anticipates congestion, significantly reducing packet loss. However, it impacts the
transport and network layers, and requires participation of a significant number of routers in the
networks (preferentially, the routers at the edge of low speeds / high latency sub networks).
3.3.6 Error Detection and Recovery
TCP error detection relies on lack of timely received acknowledgement. Recovery is performed through
retransmission of (supposed) lost packets. Loss of a large numbers of packets in a short period of time
may heavily incur the TCP connection throughput (hence performance). This may become critical for
high latency sub networks (e.g. ATN Air/Ground sub networks). Support of TCP selective
acknowledge option may mitigate this problem by allowing selective retransmission of lost packets
only (instead of the whole sequence from the first to the last packet lost). This option is specified in:
RFC 2018 - TCP Selective Acknowledgment Options.
3.3.7 Performance Enhancing Proxies (PEPs)
Performance Enhancing Proxies (PEPs) are often employed to improve severely degraded TCP
performance caused by different link characteristics in heterogeneous environments, e.g. in wireless or
satellite environments that are common in aeronautical communications. Transport layer or application
layer PEPs are applied to adapt the TCP parameters to the different link characteristics. RFC 3135
―Performance Enhancing Proxies Intended to Mitigate Link-Related Degradations‖ is a survey of PEP
performance enhancement techniques, and describes some of the implications of using Performance
Enhancing Proxies. Most implications of using PEPs result from the fact that the end-to-end semantics
of connections are usually broken. In particular, PEPs disable the use of end-to-end IPsec encryption
and have implications on mobility and handoff procedures.
3.3.8 Transport Layer usage
17
The way how transport layer connections are used has great impact on the quality of service
experienced by the application. Application messages may have different Classes of Service (CoS) and
may require to be delivered reliably and/or in correct order. Four options exist to use the TCP transport
layer service:
I. Re-/establishing of a TCP connections for each transmission and for each service
Each service instance uses a dedicated TCP connection. At the time where the application
service data is generated, the transport layer connection is opened and the data transmitted.
After successful transmission the connection is closed.
II. Establishing a TCP connection once for each service and keeping it open
Each service uses a dedicated TCP connection. The connection is opened at the time of logon or
first use and closed at time of log off or handover.
III. Re-/establishing of a TCP connection for each transmission of a multiplexed set of services
A shared TCP connection is established for all services in the set (one application may host
several services). Datagrams produced by these applications are transmitted over this shared
connection. The connection is opened at time of service datagram generation and closed after
successful transmission.
Note: All services of the multiplexed set should require the same CoS and be produced by the same
application.
IV. Establishing a TCP connection once for a multiplexed set of services and keeping it open.
A shared TCP connection is opened for all services in the set (one application may host several
services). Datagrams produced by these applications are transmitted over this shared
connection. The connection is opened at time of logon or first use and is closed at time of log
off or handover.
Note: All applications of the multiplexed set should require the same CoS and be generated by the same
application.
Multiplexing services generated by the same application but with different CoS requirements in option
III and IV is not advised, as network layer QoS is performed per TCP connection. TCP has no means to
provide differentiated QoS within one connection, so any CoS information would at least be partially
lost. Multiplexing services generated by the same application and with the same CoS requirements does
not create this problem.
It is recommended to use at least one dedicated transport connection for each service (options I, II). The
connection may be established either per service or per application.
18
If different services of one application are multiplexed to a shared TCP connection, all services must
require the same CoS (options III, IV).
For air-ground applications, it is recommended to open the connection at the time of first use and to
keep it open until logoff or handover (II, IV).
3.4 APPLICATION LAYER
3.4.1 ASN.1 extensions to CM
3.4.1.1 The ATN Context Management application requires ASN.1 adaptations to operate over the
ATN/IPS.
Note .- It is expected that a future edition of Doc 9880 will contain these extensions.
3.4.2 CM ASN.1 Definition
In order to support the conveyance of address information specific to IPS, the CM application ASN.1
needs to be updated. While there are other possible methods of obtaining application addressing
information, CM also provides additional information intended to facilitate correlation of aircraft
information with flight plan information.
New definitions of ASN.1 were added with a goal to retain backwards compatibility with previous CM
implementations. When exchanging application information, the OSI ATN CM used an
AEQualifierVersionAddress element. This would be supplemented with an
AEEnhancedQualifierVersionAddress element, with a specific new element of
APEnhancedAddress. This is shown below:
AEEnhancedQualifierVersionAddress ::= SEQUENCE
{
aeQualifier AEQualifier,
apVersion VersionNumber,
apAddress APEnhancedAddress
}
The APEnhancedAddress element would allow the carriage of either a TSAP for OSI network usage
or an IP address for IPS usage. The APEnhancedAddress is shown below:
APEnhancedAddress ::= CHOICE
{
longTsap [0] LongTsap,
shortTsap [1] ShortTsap,
ipAddress [2] IPAddress,
19
...
}
The IPAddress element is new, and is used to convey the actual IPv6 address. A specific IPv4
definition was not included in this definition. This was done to simplify definitions and to encourage
IPv6 migration. If IPv4 addresses are required by some implementations, they can still be represented
in IPv6 format using the common IPv4 mapping procedure, i.e. the first 80 bits set to zero, the next 16
set to 1, and the last 32 as the representation of the IPv4 address.
Also, an optional Port element is included. The intention was to allow the specification of a port for
the IP address that pertains to a particular application. The port would not be needed if the
implementation will use the standard IANA port numbers assigned to the IPS applications. The
IPAddress element is shown below:
IPAddress ::= SEQUENCE
{
ipHostOrAddr IPHostOrAddress,
port Port OPTIONAL,
...
}
The IPHostOrAddress element provides further flexibility in that a hostname or an IPv6 address can be
used. The hostname is further defined as an IA5 String of size between 2 and 255 characters, the port
as an integer from 0 to 65536, and the IPv6 address as an octet string of size 16. These are shown
below:
IPHostOrAddress ::= CHOICE
{
hostname [0] Hostname,
ipv6Address [1] IPv6Address,
…
}
IPv6Address ::= OCTET STRING(16)
Port ::= INTEGER(0..65536)
Hostname ::= IA5String(SIZE(2..255))
3.4.3 CM ASN.1 Usage
The usage of the IPv6 ASN.1 will be similar as for the OSI version. This means that when CM wants
to provide address information for supported applications, it needs to identify the application, version
number of the application, and address of the application for each of the applications that can be
supported. This needs to be done regardless of the network technology being used.
For an ATN application running over the IPS, the IPv6 address will be used for the addressing of each
supported application. Currently, no usage of hostname is defined, so only the IPv6Address element
20
will be used in the IPHostOrAddress. The IPv6Address element will take the value of the IPv6
address of the application.
The port number will not need to be provided, since port numbers are already defined for the
applications and therefore do not need to be conveyed end-to-end. Therefore the IPAddress element
will only contain the IPHostOrAddress.
The APEnhancedAddress element will use the IPAddress choice, as the TSAP definitions have no
relevance to the IPS. And finally, the AEQualifier and VersionNumber elements would need to be
provided as part of the AEEnhancedQualifierVersionAddress. The AEQualifier and
VersionNumber elements will be filled out in the same manner as for OSI applications, i.e. the
AEQualifier would reference an integer, defined in Doc 9705 Sub-volume IX, from 0 to 255 that
identifies the application (e.g. ADS is value ―0‖) and the VersionNumber would be an integer from 0
to 255 that identifies the version of the application.
Once exchanged, the application information would be made available to other systems or processes on
the air and ground systems as necessary in order to allow operation of the applications. This is
unchanged from OSI CM.
4.0 Quality of Service
4.1 INTRODUCTION
The IETF defined DiffServ Per Hop Behaviours (PHB) as a means to describe, classify and manage
network traffic to support the provision of QoS on IP networks. The RFCs do not dictate how PHBs are
implemented within a network and this is typically vendor dependent.
In practice, private and public IP network operators provide services based on a limited number PHBs:
o EF (Expedited Forwarding) – defined in RFC 3246, intended as a low loss, low delay, low jitter
service. This would typically be used for voice applications.
o AF (Assured Forwarding) – defined in RFC 2597 and updated in RFC 3260. Assured
forwarding allows the operator to provide assurance of delivery as long as the traffic does not
exceed some subscribed rate. These classes would be used for delay sensitive data applications
usually labelled AFx with a drop precedence. Typically each specific customer applications
would be matched to a specific AF class and usually one AF class is associated to multimedia
applications e.g. video. AF classes are independent of each other and benefit of individual
guaranteed bandwidth. This prevents one critical application to take all the available bandwidth
and block other critical applications.
o Default – A best effort class which would be used for non mission-critical, non-delay sensitive
applications.
4.2 CLASS DEFINITIONS
4.2.1 Context
21
ATN/IPS communication service providers are likely to make use of the same IPS infrastructure for
ATN and other non-ATN defined applications; for example, ATSMHS and surveillance data. Sharing
of resources can be at different levels, ATN/IPS applications can use the same type of class of service
as other non-ATN applications over the same IP routed infrastructure. Alternatively, ATN/IPS
communication service providers may only wish to share the same physical infrastructure and operate a
VPN per service; in this case a separate CoS model can be applied to each VPN service, one being the
ATN/IPS. Fundamentally, ATN/IPS communication service providers have flexibility in how they
enable CoS for the ATN/IPS over their infrastructure.
For CoS definitions, it is essential that ATN/IPS traffic is sufficiently qualified in order to properly
mark ingress traffic. As the IP packet enters the network core, PHBs are enforced, depending on the
packet marking. ATN/IPS communication service providers will need to handle un-marked or pre-
marked ingress traffic and be prepared to mark or re-mark the traffic before it is routed over their
infrastructure. The internal techniques, mechanisms and policies to enforce the PHB within the
communications service provider networks are considered out of scope of the ATN/IPS.
4.2.2 ATN/IPS PHBs/CoS
The ATN/IPS is to support legacy ATN applications over the IPS. Currently, this intended support
covers CM(DLIC), FIS(ATIS), CPDLC, ADS-C, ATSMHS. Indeed, DIR is only specified for
ATN/OSI and it is foreseen that AIDC will be implemented through regional solutions.
As each ATN application is mapped to a given CoS, the dynamic support of different priorities per user
message category is not considered.
Table 1 provides an example of an Administrative Domain that supports several applications and
Classes of Service labelled Very High, High, Normal and Best Effort.

22
Priority/Application Mapping
Traffic Identification (Ingress)
Class
(CoS
Type)
Drop
Precedence
ATN
Priority
ATN
Application
TCP/UDP
Port
IP Address
Very High
(EF)
Voice (VoIP)
RTP
numbers
16384-
32767
-
High
(AF)
1
0
-
-
-
1
-
-
-
2
-
-
-
3
ADS-C
TCP 5913
UDP 5913
The source or
destination
address will be
part of a reserved
address space
assigned to
mobile service
providers
CPDLC
TCP 5911
UDP 5911
Normal
(AF)
1
4
AIDC
TCP
8500
1
FIS(ATIS)
TCP 5912
UDP 5912
The source or
destination
address will be
part of a reserved
address space
assigned to
mobile service
providers
2
5
METAR
-
-
3
6
CM(DLIC)
TCP 5910
UDP 5910
The source or
destination
address will be
part of a reserved
address space
assigned to
mobile service
providers
ATSMHS
TCP 102
7
Best Effort
(Default)
8 - 14
-
-
Table 153 - ATN/IPS Priority mapping to Classes
1
This is applicable when OLDI/FMTP is used as a means to enable AIDC services.

23
In order to mark ingress traffic, the ATN/IPS provider has several means to identify the traffic:
destination transport port number, IP source address, IP destination address.
Note- Making use of the DSCP/ToS value set by the application or prior communication service
provider may not be the optimum approach as the value may be incorrectly configured or unknown.
4.2.3 DiffServ Code Point (DSCP) Values
The Per-Hop Behavior (PHB) is indicated by encoding a 6-bit value—called the Differentiated Services
Code Point (DSCP)—into the 8-bit Differentiated Services (DS) field of the IP packet header. The
DSCP value of the field is treated as a table index to select a particular packet handling mechanism.
This mapping must be configurable and Administrative Domains may choose different values when
mapping codepoints to PHBs. However, it is widely accepted that DSCP value 101110 refers to EF
(Expedited Forwarding).
Table 2 provides an example of mapping DSCP values to ATN/IPS PHBs where a number of
applications share the same IP network infrastructure. In this table, air ground applications have been
assigned with the special Class Selector codepoints for as specified in Document 9880 for the ATN IP
SNDCF but within the ATN/IPS it would be better to make use of AF PHBs to avoid any interaction
with legacy applications that make use of IP precedence.
Table 2 – Example of DSCP to PHB mapping
DSCP Value
PHB
Application
000000
CS0
Best effort
001000
CS1
001010
AF11
AIDC
001100
AF12
001110
AF13
010000
CS2
CM
010010
AF21
ATSMHS
010100
AF22
010110
AF23
011000
CS3
FIS
011010
AF31
Voice
Recording
011100
AF32
011110
AF33
100000
CS4
CPDLC,
ADS-C
100010
AF41
Voice
Signalling
100100
AF42
100110
AF43
101000
CS5
101110
EF
Voice

24
110000
NC1/CS6
111000
NC2/CS7
4.2.4 Traffic Characterisation
Traffic characterisation is a means to express the type of traffic patterns, integrity and delay
requirements. It provides further information to the communication service provider in order to fully
meet the user requirements within a specific network operation. Typically, traffic characterisation
information is part of the contracted service level agreement in which further parameters are defined
such as service delivery points, service resilience, required bursting in excess of committed bandwidth,
service metric points, MTTR, port speeds.
The below table 3 provides an example of traffic characterisation for ground-ground services are
derived from the Pan-European Network Services (PENS) specifications.
ATN
Application
Average
Message
Lenght
Expressed
Integrity
Jitter
Typical
Bandwidth
(point-to-point)
Network
Delay
(1-way)
Voice (VoIP
using G.729)
70
(bytes)
-
<15ms
12kbps
<100ms
OLDI/FMTP
(Regional AIDC)
150
(bytes)
1 user
corrupt
message in
2000
N/A
10kbps
<1s
ATSMHS
3 kbytes
10
-6
(in terms
of 1000bytes
message blocks)
N/A
20kbps
<5s
Table 3 – Example of Traffic Characterisation
5.0 MOBILITY GUIDANCE
5.1 MOBILE IPV6
This manual specifies that the IP mobility solution for the ATN/IPS is Mobile IPv6 (MIPv6) as
specified in RFC 3775.,with optional extensions listed in section 5.2. With Mobile IP a mobile node
(MN) has two addresses: a home address (HoA), which is a permanent address, and a dynamic care-of
address (CoA), which changes as the mobile node changes its point of attachment (See figure 5.1-1).
The fundamental technique of Mobile IP is forwarding. A correspondent node (CN), which is any peer
node with which a mobile node is communicating, sends packets to the home agent (HA) of the mobile
node. The CN reaches the HA through normal IP routing. Upon receipt of a packet from the CN, the
HA will forward these packets to the MN at its current CoA. The HA simply tunnels the original
packet in another packet with its own source address and a destination address of the current CoA. This
is possible because of the Mobile IP protocol whereby the MN sends ―binding update‖ messages to the
Comment [Q5]: Actioin13-05

25
HA whenever its point of attachment changes. The binding update associates the mobile nodes HoA
with its current CoA. The HA maintains a Binding Cash that stores the current CoA of the MN.
Foreign Network
Home Network
Remote Network
MN
HA
CN
AR
AR
HoA
CoA1
CoA2
movement
Figure 5.1-1: Mobile IP
5.1.1 MIPv6 Bidirectional Tunneling
In the reverse direction, the MN could simply send packets directly to the CN using normal IP routing.
However, this results in triangular routing and depending on the relative location of the HA, there can
be a situation where the path in one direction (e.g. CN to HA to MN) is significantly longer than the
path in the reverse direction (e.g., MN to CN). A further consideration in this case occurs if the MN
uses its home address as a source address. The problem here is that many networks perform ingress
filtering of incoming packets and will not accept packets that are topologically incorrect. This would be
the case with packets from the MN because they actually originate from the care-of-address but the
source address in the IP packet is the home address. Because of these issues, MIPv6 allows the MN to
follow the same path back to the CN via the HA using bidirectional tunneling whereby in addition to
the HA tunneling packets to the MN, the MN reverse tunnels packets to the HA. The HA will
decapsulate a tunneled IP packet and forward it to the CN. With bidirectional tunneling the CN is not
required to support Mobile IP.
5.1.2 MIPv6 Route Optimization
Bidirectional tunneling solves the problems of triangular routing and ingress filtering; however, there
still can be suboptimal routing since the path from the MN to the CN via the HA may be relatively long
even when the MN and CN are in close proximity. With MIPv6 the situation where the path through
the HA is longer than a direct path to the CN may be addressed using a technique called route
optimization. With route optimization the MN sends binding updates to both the HA and the CN. In
this case the MN and CN can communicate directly and adapt to changes in the MN‘s CoA. RFC 3775
defines the procedures for route optimization. It requires that the MN initiate the return routability
26
procedure. This procedure provides the CN with some reasonable assurance that the MN is addressable
at its claimed care-of address and its home address.
It is generally acknowledged that there are drawbacks to route optimization. RFC 4651 presents a
taxonomy and analysis of enhancements to MIPv6 route optimization. This document notes that the
two reachability tests of the return routability procedure can lead to a handoff delay unacceptable for
many real-time or interactive applications, that the security and that the return-routability procedure
guarantees might not be sufficient for security-sensitive applications, and periodically refreshing a
registration at a correspondent node implies a hidden signaling overhead. Because of the overhead and
delay associated with the return routability procedure and because at least for ATSC it is expected that
the CN and HN will be in relative close proximity, this manual requires that IPS CNs that implement
Mobile IPv6 route optimization allow route optimization to be administratively enabled or disabled
with the default being disabled. New solutions to route optimization are expected as a result of IETF
chartered work in the Mobility Extensions for IPv6 (MEXT) working group which includes aviation-
specific requirements.
5.2 ENHANCEMENTS TO MIPV6
When a mobile node (MN) changes its point of attachment to the network, the changes may cause
delay, packet loss, and generally result in overhead traffic on the network.
5.2.1 Heirarchical Mobile IPv6 (HMIPv6)
One technology developed to address these issues is ―Heirarchical Mobile IPv6 (HMIPv6)‖ [RFC
4140]. RFC 4140 introduces extensions to Mobile IPv6 and IPv6 Neighbor Discovery to allow for
local mobility handling. HMIPv6 reduces the amount of signaling between a MN, its CNs, and its HA.
HMIPv6 introduces the concept of the Mobility Anchor Point (MAP). A MAP is essentially a local
home agent for a mobile node. A mobile node entering a MAP domain (i.e., a visited access network)
will receive Router Advertisements containing information about one or more local MAPs. The MN
can bind its current location, i.e., its On-link Care-of Address (LCoA), with an address on the MAP's
subnet, called a Regional Care-of Address (RCoA). Acting as a local HA, the MAP will receive all
packets on behalf of the mobile node it is serving and will encapsulate and forward them directly to the
mobile node's current address. If the mobile node changes its current address within a local MAP
domain (LCoA), it only needs to register the new address with the MAP. The RCoA does not change
as long as the MN moves within a MAP domain. RFC 4140 notes that the use of the MAP does not
assume that a permanent HA is present, that is, a MN need not have a permanent HoA or HA in order
to be HMIPv6-aware or use the features of HMIPv6. HMIPv6-aware mobile nodes can use their RCoA
as the source address without using a Home Address option. In this way, the RCoA can be used as an
identifier address for upper layers. Using this feature, the mobile node will be seen by the
correspondent node as a fixed node while moving within a MAP domain. This usage of the RCoA does
not have the cost of Mobile IPv6 (i.e., no bindings or home address options are sent back to the HA),
but still provides local mobility management to the mobile nodes with near-optimal routing. Although
such use of RCoA does not provide global mobility.
5.2.2 Fast Handovers for Mobile IPv6 (FMIPv6)
27
A further enhancement to MIPv6 is ―Fast Handovers for Mobile IPv6 (FMIPv6)‖ [RFC 4068].
FMIPv6 attempts to reduce the chance of packet loss through low latency handoffs. FMIPv6 attempts
to optimize handovers by obtaining information for a new access router before disconnecting from the
previous access router. Access routers request information from other access routers to acquire
neighborhood information that will facilitate handover. Once the new access router is selected a tunnel
is established between the old and new router. The previous Care-of Address (pCoA) is bound to a
new Care-of Address (nCoA) so that data may be tunneled from the previous Access Router to the new
Access Router during handover. Combining HMIPv6 and FMIPv6 would contribute to improved
MIPv6 performance but this comes at the cost of increased complexity.
5.2.3 Proxy Mobile IPv6 (PMIPv6)
In MIPv6 as described above the MN updates the HA with binding updates messages. This mode of
operation is called node-based mobility management. A complimentary approach is for access network
service providers to provide network-based mobility management using Proxy Mobile IPv6 (PMIPv6)
on access links that support or emulate a point-to-point delivery. This approach to supporting mobility
does not require the mobile node to be involved in the exchange of signaling messages between itself
and the home agent to potentially optimize the access network service provision. A proxy mobility
agent in the network performs the signaling with the home agent and does the mobility management on
behalf of the mobile node attached to the network. The core functional entities for PMIPv6 are the
Local Mobility Anchor (LMA) and the Mobile Access Gateway (MAG). The local mobility anchor is
responsible for maintaining the mobile node's reachability state and is the topological anchor point for
the mobile node's home network prefix(es). The mobile access gateway is the entity that performs the
mobility management on behalf of a mobile node and it resides on the access link where the mobile
node is anchored. The mobile access gateway is responsible for detecting the mobile node's
movements to and from the access link and for initiating binding registrations to the mobile node's local
mobility anchor. An access network which supports network-based mobility would be agnostic to the
capability in the IPv6 stack of the nodes which it serves. IP mobility for nodes which have mobile IP
client functionality in the IPv6 stack as well as those nodes which do not, would be supported by
enabling Proxy Mobile IPv6 protocol functionality in the network. The advantages of PMIPv6 are
reuse of home agent functionality and the messages/format used in mobility signaling and common
home agent would serve as the mobility agent for all types of IPv6 nodes. PMIPv6 like HMIPv6 is a
local mobility management approach which further reduces the air-ground signaling overhead.
5.2.4 Network Mobility (NEMO)
Mobile IPv6 supports movement of an individual network node. However, there are scenarios in which
it would be necessary to support movement of an entire network in the ATN/IPS. One case is for APC
where is would be wasteful of bandwidth to have mobility signaling for every individual passenger.
Another case may when there is a common airborne router supporting multiple traffic types provided
proper security issues can be addressed. The extension to Mobile IPv6 which supports these scenarios
is called Network Mobility (NEMO). This manual lists NEMO in accordance with RFC 3963 as an
option for implementation. The NEMO operational model introduces a new entity called a Mobile
Network Node (MNN) which is any node in the network that moves as a unit. It can be a host moving
with other MNNs or a Mobile Router. The Mobile Router operates like any Mobile IP host on the
egress interface (to a fixed access router). The Mobile Router also negotiates a prefix list with the

28
home agent. The home agent uses this list to forward packets arriving for the MNNs that share the
common prefix to the Mobile Router. On the ingress interface (to the mobile network) the Mobile
Router advertises will advertise one or more prefixes to the MNNs. Although on the surface NEMO
appears to be a straight-forward extension to Mobile IP there are several considerations that are still
being investigated in IETF working groups. These issues include how to do NEMO route optimization
and several considerations with prefix delegation and management.
One possible implementation of NEMO mimics Proxy Mobile IPv6 in that it is the network access points that
implement the mobility support. When a mobile node attaches to the access link, the ground access point will
set up a virtual Mobile Router that registers the relevant network prefixes with the Home Agent. All traffic
received by this virtual Mobile Router for the registered mobile network prefixes will be forwarded across the air-
ground link to the connected mobile node. The mobile node need not support any Mobile IPv6 or Network
Mobility signalling and can also auto-configure the IPv6 address if the virtual Mobile Router sends Router
Advertisements for the mobile network prefixes across the air-ground link. When the mobile node connects to
another ground access point, the virtual router is moved by the ground access network to the new access point
with updates to the Home Agent as if the router was physically present on the mobile node.
This implementation model allows for mobile nodes with IPv6 stacks that are agnostic of the fact that they reside
on a mobile link and also reduces the protocol overhead for each message that is sent across the air-ground
link.”
6.0 SECURITY GUIDANCE
This section of the Manual for the ATN using IPS Standards and Protocols contains a description of the
rational for the requirements in section 2.5 of Part I of the manual with background information when
additional clarification is warranted and general guidance for implementation of security.
6.1 REQUIRMENTS FOR IMPLEMENTATION
This ATN/IPS Manual contains certain security provisions that are required to implement. The
requirement to implement security is intended to be consistent with the Security Architecture for IPv6,
which requires that all IPv6 implementations comply with the requirements of RFC 4301. Although all
ATN/IPS nodes are required to implement Internet Protocol security (IPsec) and the Internet Key
Exchange (IKEv2) protocol, the actual use of these provisions is to be based on a system threat and
vulnerability analysis.
6.2 GROUND-GROUND SECURITY
6.2.1 Ground-Ground IPsec
The baseline for ground-ground security is to require network layer security in the ATN/IPS
internetwork implemented using IPsec. IPsec creates a boundary between unprotected and protected
interfaces. IPsec is typically used to form a Virtual Private Network (VPN) among gateways (NIST
800-77). A gateway may be a router or another security device such as a firewall. In this context other
security devices are considered to be ATN/IPS nodes. The gateway-to-gateway model protects
Comment [Q6]: Action13-05
29
communications among ATN/IPS networks between regions or between states or organizations in a
particular region. IPsec may also be used in a host-to-gateway environment, typically to allow hosts on
an unsecure network to gain access to protected resources. IPsec may also be used in a host-to-host
environment where end-to-end protection of applications is provided.
To achieve interoperability across the ATN/IPS internetwork, this manual specifies support for the
IPsec security architecture, the Encapsulating Security Payload (ESP) protocol and a common set of
cryptographic algorithms. The architecture is as specified in RFC 4301. ESP is as specified in RFC
4303 and the cryptographic algorithms which may be used are specified in RFC 4835. This ATN/IPS
manual further specifies that ESP encryption is optional but authentication is always performed.
This manual specifies that ATN/IPS nodes in the ground-ground environment may implement the IP
Authentication Header (AH) protocol as specified in RFC-4302. This is in recognition that while AH
may exist in certain products, it‘s use in IPsec has been downgraded. RFC 4301 states, ―Support for
AH has been downgraded to MAY because experience has shown that there are very few contexts in
which ESP cannot provide the requisite security services. Note that ESP can be used to provide only
integrity, without confidentiality, making it comparable to AH in most contexts‖.
6.2.2 Ground-Ground IKEv2
The IPsec architecture [RFC 4301] specifies support for both manual and automated key management.
As the ATN/IPS evolves use of manual key management will not scale well. Therefore this manual
specifies that nodes in the ground-ground environment shall implement the Internet Key Exchange
(IKEv2) Protocol as specified in RFC 4306 for automated key management. IKEv2 is the latest version
of this protocol. The IKEv2 specification is less complicated than the first version of the protocol
which should contribute to better interoperability among different implementations.
As is the case for ESP, the IKEv2 protocol requires a set of mandatory-to-implement algorithms for
interoperability. This manual requires that nodes in the ground-ground environment implement the
Cryptographic Algorithms specified in RFC 4307.
6.2.3 Alternatives to IPsec/IKEv2 for Ground-Ground Security
Alternatives to network security may be appropriate in certain operating environments. Alternatives to
IPsec may be applied at the Data Link, Transport, or Applicaiton Layer. NIST SP 800-77 describes
the main alternatives, characterizes the alternatives in terms or strengths and weaknesses, and identifies
potential cases where they may be used as alternatives to IPsec.
6.3 AIR-GROUND SECURITY
6.3.1 Air-Ground IPsec
Similar to the ground-ground environment, to achieve interoperability in the air-ground environment
this manual specifies that ATN/IPS nodes support the IPsec security architecture and the Encapsulating
Security Payload (ESP) protocol. As in the ground case, the architecture is as specified in RFC 4301
and ESP is as specified in RFC 4835. However rather than implement all of the the cryptographic
30
algorithms which are identified in RFC 4835, specific default algorithms are identified for
authentication and for encryption and authentication together. This is in consideration of bandwidth-
limited air-ground links and so as not to have unused code in the avionics platform.
The authentication algorithm selected for use when confidentiality is not also selected is
AUTH_HMAC_SHA2_256-128 as specified in RFC 4868. This algorithm uses a 256-bit key to
compute a HMAC tag using the SHA-256 hash function. The tag is truncated to 128 bits. The same
algorithm is used for integrity in IKEv2 as described below.
If ESP encryption is used, this manual specifies that the Advanced Encryption Standard (AES) be used
in Galois/Counter Mode (GCM). AES-GCM is used with an 8 octet Integrity Check Value (ICV) and
with a key length attribute of 128 as specified in RFC 4106. AES-GCM is a ―combined mode‖
algorithm which offers both confidentiality and authentication in a single operation. Combined mode
algorithms offer efficiency gains when compared with sequentially applying encryption and then
authentication. When AES-GCM is used the ICV consists solely of the AES-GCM Authentication Tag
and a separate HMAC tag is not applied.
6.3.2 Air-Ground IKEv2
Because manual key management is not practical in the air-ground environment, this manual requires
that ATN/IPS nodes implement the Internet Key Exchange (IKEv2) Protocol as specified in RFC 4306.
As is the case of ESP in consideration of bandwidth limitations and so that there will not be unused
code in the avionics platform, this manual specifies a set of default algorithms for use in IKEv2. The
selection of transforms is intended to be compatible with the selections of the ATA DSWG and AEEC
DSEC working groups to the extent possible; however, this manual only uses transforms that have been
registered with IANA. Five transforms are used by IKEv2.
1. There is a pseudo-random function (PRF) which is used in IKEv2 for generation of keying
material and for authentication of the IKE security association. This manual requires the use of
PRF_HMAC_SHA_256 as specified in RFC 4868 as the PRF.
2. IKEv2 uses the Diffie-Hellman key exchange protocol to derive a shared secret value used by
the communicating peers. The Diffie-Hellman calculation involves computing a discrete
logarithm using either finite field or elliptic curve arithmetic. When elliptic curve cryptography
is used, the conventional choices are to use either prime characteristic or binary curves. This
manual selects a prime characteristic curve and requires the use of the 233-bit random ECP
group as specified in RFC 4753.
3. When public key certificates are used in IKEv2 for entity authentication certain data must be
signed in the IKEv2 exchange. This manual requires that signing be performed using the
Elliptic Curve Digital Signature Algorithm (ECDSA) using SHA-256 as the hash algorithm on
the 256-bit prime characteristic curve as specified in RFC 4754.
4. The authentication exchange of IKEv2 has a payload that is encrypted and integrity protected.
This manual specifies that AES CBC with 128-bit keys as specified in RFC 3602 be used as the
IKEv2 encryption transform.
31
5. This manual specifies that the encrypted payload be integrity protected using HMAC-SHA-256-
128 as specified in RFC 4868.
The above suite of algorithms together with the use of AES-GCM for ESP encryption is the ―Suite-B-
GCM-128‖ set specified in RFC 4869. This suite is expected to be available as a Commercial-Off-The-
Shelf implementation and should provide adequate cryptographic strength beyond 2030. See NIST SP
800-57 for additional guidance on cryptographic algorithm and key size selection.
The use of IKEv2, while offering the advantage of COTS availability and flexibility in signaling
algorithms, authentication mechanisms, and other parameters, will result in more overhead than might
otherwise be incurred in a custom aviation-specific solution. IKEv2 requires at least 4 messages to be
exchanged to establish a session key for air-ground communications. In addition, the encryption
algorithms in IKEv2 and ESP result in message expansion. While this expansion may be negligible for
large messages, it will represent a more significant percentage for small messages. While this is a
significant consideration for bandwidth-constrained data links, it is expected to be less of an issue when
there is a high-speed data link approved for safety services.
6.3.3 Securing Air-Ground End-to-End Communications
Figure 6.3.3-1 depicts the options for securing end-to-end communications in the ATN/IPS air-ground
environment. IKEv2 and ESP of IPsec are required to be implemented. This manual also defines
options for TLS and for IKEv2 with Application-level security. In all cases this manual defines a
default set of cryptographic algorithms.

32
Home
Agent
Access
Router
Access
Router
Correspondent
Node
Mobility
Service
Provider
(MSP)
IKEv2/IPsec(ESP),
TLS,
IKEv2/Appl-Scty
Mobile Node
PKI
Certificate
Server
Figure 6.3.3-1 – Options for Air-Ground End-to-End Security
6.3.3.1 Air-Ground End-to-End Network Layer Security
As described in sections 6.3.1 and 6.3.2, for air-ground end-to-end network layer security this manual
requires that ESP be implemented along with IKEv2 for key establishment. Figure 6.3.3-1 depicts the
CN interfacing to a PKI Certificate Server. The interface method is considered a local matter. This
may be an LDAP interface to a database of X.509 Certificates and Certificate Revocation Lists (CRLs)
or another certificate management protocol. As noted above a ―Suite-B‖ set of algorithms as specified
in RFC 4869 is being used for ESP and IKEv2. The US National Security Agency Suite B Certificate
and CRL Profile identifies the Certificate Management Messages over CMS protocol as specified in
RFC 2797 as the preferred protocol. The actual authentication method used in an Administrative
Domain is a local matter and will depend on the application. IKEv2 permits pre-shared keys or Digital
Certificates to be used with Digital Certificates considered to be a stronger method. It would be
possible to use pre-shared keys in the downlink direction and to use Digital Certificates in the uplink
direction. Since there is no practical way for the MN to independently check a CRL, short-lived
certificates could be used in the uplink direction. In the downlink direction if Digital Certificates are
used it is recommended that rather than the MN sending an actual certificate, the MN should use the
IKEv2 ―Hash and URL‖ method. With method the MN sends the URL of a PKI certificate server
where the CN can retrieve its certificate. Section 6.3.5 contains more guidance on PKI profiles and
certificate policy. This section has described using certificates for authentication when strong
33
authentication is required. This is the preferred approach in the end-to-end environment even though it
would be possible to use IKEv2 and the Extensible Authentication Protocol (ESP) with an
authentication, authorization, and accounting (AAA) infrastructure as will be described for access
networks and mobility service providers. It is expected that PKI bridge concept being developed by the
Air Transport Association (ATA) Digital Security Working Group (DSWG) will facilitate operating a
PKI on a global basis. Under the PKI Bridge each Administrative Domain may certify to a central
bridge rather than each Administrative Domain cross-certifying with every other Administrative
Domain.
6.3.3.2 Air-Ground End-to-End Transport Layer Security
This manual permits ATN/IPS mobile nodes and correspondent nodes to implement the Transport
Layer Security (TLS) protocol as specified in RFC 5246. This will permit applications that already use
TLS to operate in the ATN/IPS air-ground environment. If TLS is used, then the following cipher suite
as defined in RFC 4492 is required:
TLS_ECDH_ECDSA_WITH_AES_128_CBC_SHA
This cipher suite is for:
1. The Transport Layer Security (TLS) protocol. Version 1.0 or 1.1 may be used
2. Elliptic Curve Diffie Hellman (ECDH) key agreement
3. Elliptic Curve Digital Signature Algorithm (ECDSA) for client authentication
4. The Advanced Encryption Standard (AES) with 128 block size in Cipher Block Chaining
(CBC) mode for confidentiality
5. The Secure Hash Algorithm (SHA) version 1 for integrity (i.e., for HMAC)
This cipher suite is selected because it has algorithms in common with those identified for air-ground
IPsec and IKEv2. Note that this cipher suite a required implementation for servers and one of the suites
that clients may implement to be compliant with RFC 4492.
6.3.3.3 Air-Ground End-to-End Application Layer Security
This manual permits ATN/IPS mobile nodes and correspondent nodes to implement application layer
security at the IPS Dialogue Service Boundary. This alternative is intended to be for legacy ATN
applications which may already implement application layer security in the ATN/OSI environment. In
this case mobile nodes and correspondent nodes shall append an HMAC-SHA-256 keyed message
authentication code to application messages. HMAC-SHA-256 is already required for ESP and IKEv2
so there is essentially no additional cryptography for this option. The HMAC tag truncated to 32 bits is
computed over the User Data concatenated with a send sequence number for replay protection. Since

34
IKEv2 is required in any case, if application layer security is used for air-ground security, IKEv2 is
again used for key establishment.
6.3.4 Securing Access Network and Mobile IP Signaling
Figure 6.3.4-1 depicts options for securing Access Service Provider (ASP) or Mobility Service Provider
(MSP) signaling. The distinction between an ASP and MSP has become useful in IETF working
groups examining the use of AAA back end infrastructures for mobility security. According to RFC
4640 an ASP is a network operator that provides direct IP packet forwarding to and from the end host.
An MSP is a service provider that provides Mobile IPv6 service. In the figure the AAA-NA service is
used for network access and the AAA-MIP server is used for access to Mobile IP service.
Home
Agent
Mobility
Service
Provider
(MSP)
Network Access
Security
Mobile Node
AAA-NA Server
AAA-MIP Server
MIPv6
Security
Access
Service
Provider
(ASP)
Figure 6.3.4-1 – ASP or MSP Security
6.3.4.1 Securing Mobile IP Signaling
Consistent with RFC 3775 this manual requires that IPsec be used specifically for protection of Mobile
IP signaling in conformance to RFC 4877. RFC 4877 is an update to RFC 3776 and describes how
IKEv2 is to be used for automated key management. RFC 4877 in particular describes how IKEv2
with EAP as the authentication method may be used. When extensible authentication is used in IKEv2
there is an additional exchange after the IKE_SA_INIT and IKE_SA_AUTH exchanges. In this case
the MN will not include an authentication payload in the IKE_SA_AUTH exchange but rather will
include an EAP payload in the next message. The HA then interacts with the AAA-MIP server to
complete the authentication exchange and if successful completes the IKEv2 exchange.
35
6.3.4.2 Air-Ground Access Network Security
This ATN/IPS Manual requires that mobile nodes implement the security provisions of the access
network. The security provisions of an access network are those associated with access control to the
network itself and are typically implemented using an AAA infrastructure.
The IETF mobility working groups and other standards development organizations have recognized
that although Mobile IPv6 and Proxy Mobile IPv6 were originally designed without integration with an
AAA infrastructure, it may be more efficient to authenticate users using credentials stored at the AAA
server. Furthermore, use of an AAA infrastructure may facilitate other bootstrapping functions such as
dynamic configuration of other parameters such as the home address and home agent address in order
to accomplish mobility registration. EAP between the MN and Authenticator may operate over the
access network link level protocol or in conjunction with IKEv2 as described for securing Mobile IP
signaling. EAP between the Authenticator and AAA server operates over RADIUS [RFC 2865] or
DIAMETER [RFC 3588].
6.3.5 Public Key Infrastructure Profile and Certificate Policy
This manual requires that ATN/IPS nodes use the Internet X.509 Public Key Infrastructure Certificate
and Certificate Revocation List (CRL) Profile as specified in RFC 5280 and the Internet X.509 Public
Key Infrastructure Certificate Policy and Certificate Practices Framework as specified in RFC 3647.
This manual notes that the Air Transport Association (ATA) Digital Security Working Group (DSWG)
has developed a Certificate Policy (ATA Specification 42) for use in the Aviation community. ATA
Specification 42 includes certificate and CRL profiles that are suitable for aeronautical applications.
These profiles provide greater specificity than, but do not conflict with, RFC 5280. The ATA
Specification 42 profiles are interoperable with an aerospace industry PKI bridge. Interoperability with
an operational aerospace and defense PKI bridge will provide the opportunity to leverage existing
infrastructure rather than develop an infrastructure unique to the ATN/IPS and will more readily
achieve interoperability and policy uniformity in a multi-national, multi-organizational aerospace and
defense environment.
6.3.6 General Guidance for Implementation of Security
Many government agencies have developed additional guidance and profiles for implementing security.
In the US the NIST 800 series of recommendations is an example of general security implementation
guidance covering a broad range of topics.
In the IETF there have been many Internet Drafts dealing with security. Two informational RFCs of
particular interest are RFC 4942 AND RFC 4864. RFC 4942 gives an overview of security issues
associated with IPv6. The issues are grouped into three general categories: issues due to the IPv6
protocol itself; issues due to transition mechanisms; and issues due to IPv6 deployment. RFC 4864
notes that Network Address Translation (NAT) is not required in IPv6 and describes how Local
Network Protection (LNP) mechanisms can provide the security benefits associated with NAT. In
particular, RFC 4864 describes how the IPv6 tools for Privacy Addresses, Unique Local Addresses,
DHCPv6 Prefix Delegation, and Untraceable IPv6 Addresses may be used to provide the perceived
security benefits of NAT including the following: Gateway between the Internet and an Internal
Network; Simple Security (derived from stateful packet inspection); User/Application Tracking;

36
Privacy and Topology Hiding; Independent Control of Addressing in a Private Network; Global
Address Pool Conservation; and Multihoming and Renumbering. RFC 4864 describes the addition
benefits of native IPv6 and universal unique addressing including the following: Universal Any-to-
Any Connectivity, Auto-Configuration, Native Multicast Services, Increased Security Protection,
Mobility and Merging Networks.
7.0 Voice over Internet Protocol (VoIP)
7.1 EUROCAE SPECIFICATION
EUROCAE published a series of documents which define the Voice over Internet Protocol
specification as related to the foreseen implementation of VoIP ATM services in Europe.
These documents are numbered ED 136, ED 137A, ED 138 and consist of:
•ED-136 - VoIP ATM System Operational and Technical Requirements, edition February 2009
(ED136)
•ED-137A - Interoperability Standards for VoIP ATM Components with the following parts:
(ED137)
ED-137A Part1 – Radio, edition September 2010
ED-137A Part 2 – Telephone, edition September 2010
ED-137A Part 2A - Telephone Legacy Interworking SIP/ATS-R2, edition September 2010
ED-137A Part 2B - Telephone Legacy Interworking SIP/ATS-NO.5, edition September
2010
ED-137A Part 2C - Telephone Legacy Interworking SIP/ATS-QSIG, edition September
2010
ED-137A Part 3 – Recording, edition February 2009
ED-137A Part 4 – Supervision, edition February 2009
•ED-138 - Network Requirements and Performances for VoIP ATM Systems with the following
parts:
ED-138 Part1 – Network Specification, edition February 2009
ED-138 Part 2 – Network Design Guideline, edition February 2009 (ED138)
Formatted: Indent: Before: 0.75"
Formatted: Indent: Before: 0.75"
Formatted: Indent: Before: 0.75"
Formatted: Indent: Before: 0.75"
Formatted: Indent: Before: 0.75"
Formatted: Indent: Before: 0.75", Hanging:
0.5"
Formatted: Indent: Before: 0.75"
Formatted: Indent: Before: 0.75"
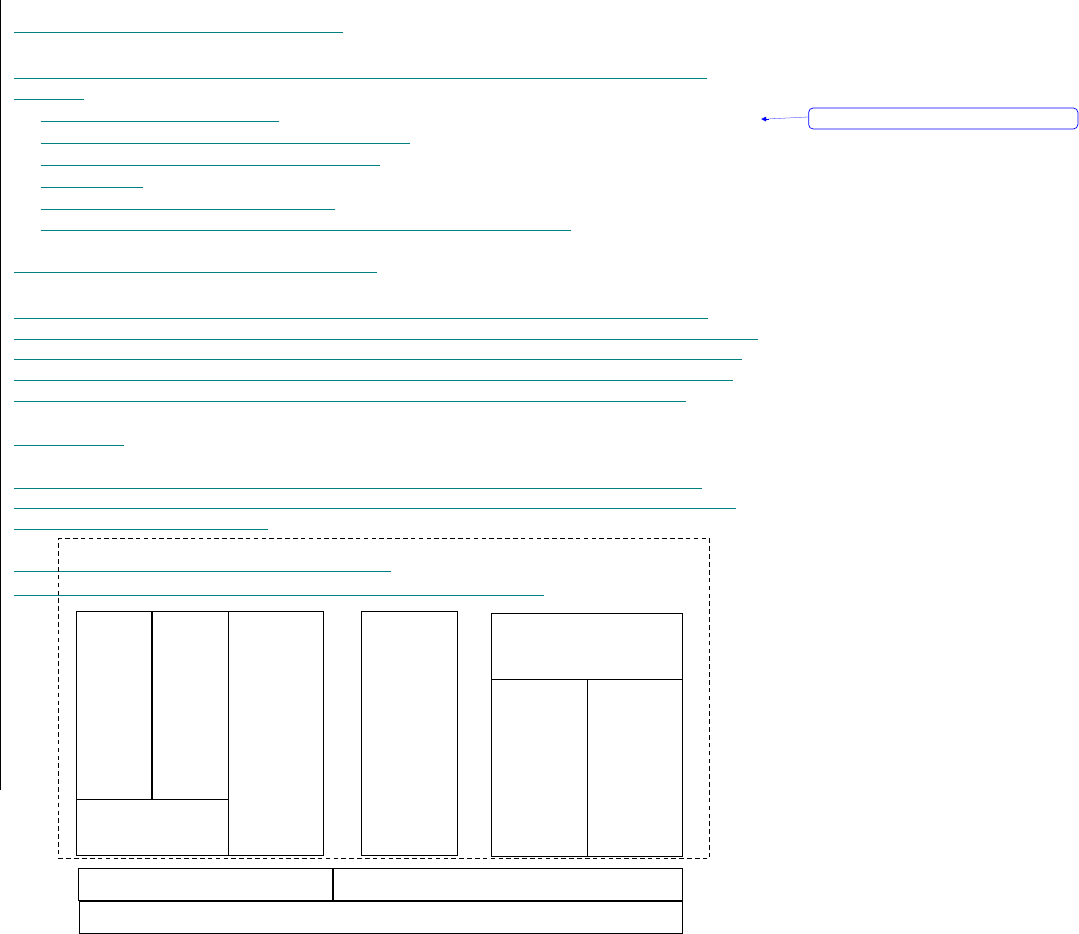
37
They are available for download on the EUROCAE website at:
http://www.eurocae.net/
7.2 ADDITIONAL INFORMATION
The key advantages associated with the use of a packet network for the transmission of digitized
voice are:
Bandwidth allocation efficiency
Ability to use modern voice compression methods
Associate economics with shared network use
Reduce costs
Enhanced reliability of packet networks
Ability to use multiple logical connections over a single physical circuit.
7.2.1 STANDARDS AND PROTOCOLS
There are two standardized frame works for implementing VoIP, H.323 and SIP. Although both
protocols may be used for VoIP applications, the original focus of each protocol is different. The focus
of H.323 has been to handle voice and multimedia calls, including supplementary services, while SIP
was designed as a generic transaction protocol for session initiation not bound to any specific media
(e.g., audio or video). Details of relevant protocols are described in the following subsection:
7.2.1.1 H323
As shown in Figure 7.1, H.323 operates in the application layer to support multimedia, data and
signaling protocols. Also depicted in Figure 7.1 are the various protocols used to convey multimedia
traffic over TCP/UDP/IP networks.
Multimedia Data Transfer Signaling
Audio
Codecs
G.711
G.728
G.729
RTCP
(Real Time
Transport
Control
Protocol)
RTP
T.120
(Real
Time)
T.130
(Audio-
Visual
Control)
H.225.0
RAS
Q.931
(Call
Signalling)
H.235
(Security)
H.245
(Control
Signalling)
UDP (User Datagram Protocol)
TCP (Transfer Control Protocol)
IP (Internet Protocol) v4 or v6
H.450.1 Series
(Supplementary
Services)
Video
Codecs
H.261
H.263
Formatted: Bullets and Numbering

38
Figure 7.1 H.323 Core Architecture

1
7.2.1.1.1 Multimedia
This group of protocols converts between analog (e.g., voice) and digital signals, which
are fed into, or picked from, the UDP/IP network. Some of these protocols include:
Audio codecs – These compress digital voice for low bandwidth transmission, and
decompress digital voice received from the network for feeding to the user audio
device (e.g., speaker, headphone).
Video codecs – These compress digital video for constrained bandwidth, and
decompress digital video received from the network for feeding to the user video
device.
RTP (Real-Time Transport Protocol) and RTP Control Protocol (RTCP) – These
are control protocols for the payloads fed into the network. RTP regulates the end-
to-end delivery of audio and video in real time over IP networks. RTCP regulates
the control services in multimedia transmissions, and monitors the quality of its
distribution, including synchronization of receivers.
7.2.1.1.2 Data Transfer
This class of protocols provides real-time, multi-point data communications and
application services over IP networks (e.g., collaborative decision making with video,
voice, and data exchange). Data transfers between generic applications and the IP
network are processed by the T.120 protocol, which can operate over various transports,
including PSTN and ISDN.
T.130 is a protocol still under development for controlling audiovisual sessions for real-
time multimedia conferencing, and ensure high QoS.
7.2.1.1.3 Signalling
H.225.0 call signaling is used to set up connections and exchange call signalling
between H.323 endpoints (terminals and gateways), which are transported as real-
time data and carried over the TCP/UDP/IP network. H.225.0 uses Q.931 for call
setup and teardown.
H.245 control signaling is used to exchange end-to-end messages between
H.323 endpoints. The control messages are carried over H.245 logical control
channels, which are relayed between conference session endpoints.
H.235 provides security services within the H.323 framework, such as
authentication, encryption, integrity and no-repudiation.
H.450.1 deals with the procedures and signaling protocol between H.323 entities for the
control of supplementary services. Other protocols within the H.450 series
(i.e. H.450.2-12) provide specific supplementary services (e.g., call transfer, call hold,
call waiting, and call priority).
Formatted: Bullets and Numbering
Formatted: Bullets and Numbering

2
7.2.1.2 MGCP/MEGACO
Shown in Figure 3 is the SIP Protocol Suite. SIP is an application layer control protocol
that provides advanced signaling and control functionality for large range multimedia
communications. SIP is an alternative to H.323, which establishes, modifies, and
terminates multimedia sessions, which can be used for IP telephony. SIP is an important
component in the context of other protocols to enable complete multimedia architecture,
as shown in Figure 4. These include RTP for real time data transport and QoS assurance,
RTSP for controlling streaming media, MEGACO for controlling gateways to the PSTN,
and SDP for describing multimedia sessions. These sessions include Internet multimedia
conferences, Internet telephone calls, and multimedia distribution over TCP/UDP/IPv4,
or IPv6, as shown in Figure 5.
Figure 3 SIP Protocol Suite
SIP Suite
Application and system control
Call Transfer/Conferences/Call
Hold/ Call Monitoring and other
Supplementary Services
SIP
Extension
Headers
Methods
Message Body (e.g. SDP)
Data
Services
e.g.,
using
RTSP
RTP
Audio Video
AV I/O
equipment
TCP UDP
IP
PINT
(Interface
to PSTN
Signalling
e.g. SS7,
ATS-
QSIG)

3
MEGACO
Gateway
IP
Network
PSTN
Figure 4. VoIP Interface to PSTN via MEGACO
SIP
Server
Figure 5. VoIP with SIP
IP
Network
IP
Network
IP
Network
RTP/UDP
SIP/TCP or UDP

4
8.0 Directory Service
8.1 INTRODUCTION
8.1.1 OVERVIEW
8.1.1.1 The ATN directory service (ATN DIR) application allows ATN users to obtain
directory information about ATN users, applications and services participating in the
ATN. The ATN DIR is composed of three parts: a directory information base, directory
system agents (DSAs) and directory user agents (DUAs).
8.1.1.2 The ATN DIR provides generic directory services over the ATN internet. It may
also be used as a directory system supporting user applications communicating over the
ATN. This may be achieved, for example, by means of application programmme
interfaces.
8.1.1.3 The ATN DIR is provided by the implementation over the ATN internet
communication services of the directory services specified in ISO/IEC 9594 and CCITT
or ITU-T X.500, and complemented by the additional requirements specified in this
manual. The ISO/IEC directory services international standards and the ITU-T X.500
series of recommendations (1993 or later) are in principle aligned with each other.
However, there are a small number of differences. In this manual, reference is made to
the relevant ISO International Standards and ISPs where applicable.
8.1.2 TERMINOLOGY
8.1.2.1 The classifications defined in the referenced ISPs and PICS in the base standards
are used to express conformance requirements — i.e. static capability — in this manual.
These classifications include the following elements, of which the complete definition
may be found in each referenced document:
a) mandatory (full) support (M). The support of the feature is mandatory for all
implementations;
b) optional support (O). The support of the feature is left to the implementer;
c) conditional support (C). The requirement to support the item depends on a specified
condition. The condition and the resulting support requirements are stated separately;
d) excluded (X). This feature is not allowed in implementation;
e) out of scope (I). Support of this feature is outside of the scope of this part of the
Formatted: Heading 1
Formatted: Left

5
specification; and
f) not applicable (-). The item is not defined in the context where it is mentioned. There is
no support requirement. The occurrence of “not applicable” is mainly due to the format of
the tables in the profile or PICS requirements list.
8.1.3 ATN DIR MODEL
8.1.3.1 A directory is a collection of systems that cooperate to hold a logical database of
information about a set of objects in the real world. The users of a directory, including
people and computer programs, can read or modify the information, or parts of it, subject
to having permission to do so. Each user accesses the information using a DUA which is
considered to be an application process. These concepts are illustrated in Figure 1-1.
Figure 8-1. Access to the ATN DIR
8.1.3.2 The information held in the ATN directory is collectively known as the directory
information base (DIB). The DIB contains an entry for each real-world object (person,
application, locality, etc.) represented in the directory. Entries are organized in such a
way as to be directly identified using the directory name of the real-world object that
represents them.
8.1.3.3 The structure of the DIB, called the directory information tree (DIT), defines a
hierarchy of entries contained in the directory. The position of an entry in the DIT
hierarchy determines that entry‘s directory name. The information content of each entry
is defined by one or more object classes to which the entry belongs. An object class
defines the information content of an entry as a set of attributes. Each attribute is a piece
of information about the real world object or its entry. Attributes are defined by an
attribute type (defining the semantics of the attribute) and an attribute syntax that enables
extraction and testing of the value of the attribute. A number of matching rules are
defined for each attribute syntax to enable testing of attributes values during the
execution of directory operations. This allows users to select one or more directory
entries based on the entry‘s content. A directory schema defines the object classes,
attribute types, attribute syntaxes and matching rules of a part of the DIB.
The Directory
Access Point
DUA
Formatted: Font: (Default) Times New
Roman, (Asian) +Body Asian, 12 pt, Not Bold,
Complex Script Font: Angsana New

6
8.1.3.4 The functional model of the ATN DIR is shown in Figure 1-2.
Figure 8-2. Functional model of the ATN DIR
8.1.3.5 A DSA is an ATN application process which is a part of the directory and whose
role is to hold, and to provide access, to the DIB for DUAs and/or other DSAs. A DSA
may store fragments of the DIB in its local database. It may also interact with other DSAs
to carry out requests concerning other fragments of the DIB. This is called ―chaining‖.
Alternatively, the DSA may direct a user (or another enquiring DSA) to a further DSA
which can help carry out the request. This is called ―referral‖.
8.1.3.6 A set of one or more DSAs and zero or more DUAs managed by a single
organization may form a Directory Management Domain (DMD). The DSAs and DUAs
of different DMDs interconnect in various ways to resolve user requests. DSAs of
different DMDs may connect with each other to resolve chained directory operation on
behalf of a user. Alternatively, a DMD may respond to one of its user‘s requests by
referring the user to connect directly with the DSA of another DMD. The particular
choice is made on the basis of operational requirements.
8.1.3.7 The DUA interacts with the ATN DIR by communicating with one or more
DSAs. A DUA need not be bound to any particular DSA and it may interact directly with
various DSAs to make requests. For administrative reasons, it may not always be possible
to interact directly with the DSA that is to carry out the request, e.g. to return directory
information. It is also possible that the DUA may be able to access the entire DIB
through a single DSA. For this purpose, DSAs may need to interact with each other by
using chained operations.
8.1.3.8 A DSA is concerned with carrying out the requests of DUAs and with obtaining
the information from other DSAs when it does not have the necessary information. It may
take the responsibility to obtain the information by interacting with other DSAs on behalf
of the DUA.
8.1.3.9 The ATN directory is supported by several different protocols: the directory
access protocol (DAP); the directory system protocol (DSP); the directory information
shadowing protocol (DISP); and the directory operational binding protocol (DOP). This
The Directory
DSA
DSA
DSA
DSA
Formatted: Font: (Default) Times New
Roman, (Asian) +Body Asian, 12 pt, Not Bold,
Complex Script Font: Angsana New

7
manual provides specifications of DAP and DSP for use in the ATN. DISP is not
profiled, but indications as to when it should be used are given. DOP is not profiled.
8.1.3.10 The DAP and DSP profiles are based on the requirements of ISO/IEC
13248-1 (Directory Access Protocol — Protocol Implementation Conformance
Statement) which is equivalent to ITU-T Rec. X.583 and ISO/IEC 13248-2 (Directory
System Protocol — Protocol Implementation Conformance Statement) which is
equivalent to ITU-T Rec. X.584, and ISO/IEC 9594:1995. The high-level ATN directory
protocol requirements expressed in this manual are:
a) conformance to the base standards by reference to ITU-T Recommendation X.583 |
ISO/IEC 13248-1 and ITU-T Recommendation X.584 | ISO/IEC 13248-2 – PICS;
Note.— These are withdrawn standards but are available from the ITU-T website.
b) conformance to certain protocol extensions defined in ISO/IEC 9594:1995;
c) mandatory conformance to referral and distributed operations; and
d) conditional conformance to strong authentication and signed directory operations
dependent on configuration and the availability of other security provisions.
8.1.3.11 Security
8.1.3.11.1 An overall strong security requirement is specified because some of the
ATN directory data is highly critical to the operation (such as AMHS<>AFTN address
translation data of ATSMHS) which must be protected against corruption or modification
by unauthorised entities (e.g. by a masquerade attack). For this reason, strong
authentication and signed operations, as specified by the [StrongSec] functional group or
some other equivalent measures, need to be implemented depending on the configuration
of DUAs and DSAs, and the relative security of the operational domain.
8.1.3.11.2 This specification therefore identifies an optional strong security
functional group. Its use is dependent on a number of factors related to the directory‘s
configuration and distribution and the operational domain in which the directory system
operate. Requirements for this functional group are identified throughout this manual by
means of the [StrongSec] predicate. In certain circumstances (e.g. where distributed
operations are used) the DIB contents may be protected by the signed directory
operations and responses contained in the [StrongSec] functional group. These effectively
authenticate each operation and response individually. An alternative equivalent
protection may be implemented by local or bilaterally agreed measures.
8.1.3.11.3 Authentication based on simple password protection is required as a
minimum. Further (strong) authentication, if required, is a part of the [StrongSec]
functional group which identifies suitable strong authentication protocol elements using
standards-based techniques.
Formatted: Left

8
8.1.3.12 ATN DUA types
This section identifies three different profiles for ATN DUAs, each with access to a
different required set of Directory operations.
Administrative DUA. An administrative DUA provides the user with the full
range of directory operations, and is suitable for directory administrators of
various kinds. It needs access to all of the directory operations, and it is to be
subject to access controls for the modifying operations. It is also required to
protect the DIB‘s data integrity and accuracy.
Operational personnel DUA. An operational personnel DUA provides a (human)
operational user with the limited range of directory operations enabling query of
the directory without being granted access to the DIB modifying operations.
Typical users of operational personnel DUAs include AMHS operators, AMHS
users and users of end systems supporting ATN applications. Planners and
management personnel also belong to this profile. This DUA requires guarantees
of data integrity and accuracy.
Autonomous operational DUAs. An autonomous operational DUA (supporting,
for example, AMHS MTAs, UAs, MS and MTCUs, or other ATN applications) is
an autonomous process with limited requirements of directory operations (e.g. it
requires the read, compare and search operations only) and it operates without
human intervention to invoke directory operations and evaluate results. This DUA
requires guarantees of data accuracy.
8.2 SYSTEM LEVEL PROVISIONS
8.2.1 ATN DIR SYSTEM LEVEL REQUIREMENTS
8.2.1.1 The ATN DIR shall be implemented in conformance with provisions of this
manual.
8.2.1.2 The systems comprising the ATN DIR shall themselves be comprised of two
functional objects: DSAs and DUAs, the roles of which are described in ISO/IEC 9594-
1:1995.
8.2.1.3 ATN DIR users shall access the ATN DIR using an ATN Directory User Agent
(ATN DUA).
8.2.1.4 An ATN directory system agent shall support either the DAP the DSP or both,
and optionally the DISP as specified in Chapter 5.
Formatted: Left
Formatted: Left

9
8.2.1.5 When used in support of the AMHS, an ATN DUA shall support the DAP, as
specified in Chapter 5.
8.2.1.6 The ATN DIR shall be based on ISO/IEC 9594:1995 (ITU-T X.500:1993)
specifications.
8.2.1.7 The ATN DIB shall be organized according to the structure of the ATN DIT as
specified in Chapter 4.
8.2.1.8 The contents of the ATN DIB shall be capable of holding entries of the object
classes defined in Chapter 4.
8.2.1.9 The ATN DSA shall support the PrintableString attribute syntax in order to ensure
a minimum level of interworking.
8.2.1.9.1 The support for PrintableString attribute syntax is a mandatory
requirement of ISO/IEC ISP 15126-1.
8.2.1.10 DUAs and DSAs shall protect the integrity of the DIB contents and the
results of operations This may be achieved either by implementing the [StrongSec]
functional group specified in this manual or may be achieved alternatively by local and
bilateral arrangements appropriate to the operational domain(s).
8.2.2 DIRECTORY SERVICE DEPLOYMENT
2.2.1 A directory service implementation shall consist of one or more DSAs.
2.2.2 A user of the directory service shall make use of one or more DUAs.
2.2.3 If a DSA supports user access, it shall implement the DAP.
2.2.4 If a DSA supports access to other DSAs, it shall implement the DSP.
2.2.5 If a DSA provides or uses copies of DIB information with other DSAs, it shall
implement the DISP.
2.2.6 It shall be valid to implement an ATN DUA or ATN DSA claiming conformance
to this manual with or without the support of the strong security [StrongSec] functional
group defined in this manual.
2.2.7 A DUA shall implement simple authentication for DAP.
2.2.8 A DSA shall implement simple authentication for DAP, DSP and DISP.
Formatted: Left

10
2.2.9 DUAs and DSAs implementing strong security [StrongSec] shall also implement
strong authentication in the bind operation. This document profiles the protocol elements
for [StrongSec] including the requirements for strong authentication. The cryptographic
techniques to support the signed operations and responses of strong security are being
developed. The cryptographic processing supporting strong authentication needs to be
established by local or bilateral agreements.
2.2.10 If the [StrongSec] functional group is not implemented, then alternative,
equivalent measures (e.g. data link and/or physical security) shall be implemented to
protect the DIB content‘s integrity and accuracy, and the integrity and accuracy of the
data returned in responses to DUAs.
2.2.11 A DUA shall either support the [StrongSec] functional group for DAP, or
implement some other equivalent alternative security measures in case of local access.
2.2.12 A DSA shall either implement the [StrongSec] functional group for DAP, DSP
and DISP for any configuration where remote access from DUAs or other DSAs is
included, or implement some other equivalent alternative security measures in case of
local access.
2.2.13 Operational personnel DUAs and autonomous operational DUAs shall be
restricted to accessing the DIB using only the directory read operations — Read, Search
and Compare.
2.2.14 An ATN DUA or ATN DSA implementation claiming conformance with the
support of strong security shall implement all the associated requirements of this manual
conditional directly or indirectly on the [StrongSec] predicate.

1
98.0 IPS Implementations
98.1 OLDI
On-Line Data Interchange (OLDI) combined with the Flight Message Transfer Protocol
(FMTP) is a means to enable AIDC operational requirements for the co-ordination and
transfer of aircraft between adjacent air traffic control units. The relationship between
AIDC and OLDI messages is described in the Appendix of ICAO Document 9694, Part
VI, Chapter 1. The OLDI specification does not mandate the implementation of OLDI
messages but specifies the requirements that need to be met when implementing such
facilities. If OLDI messages are implemented as the result of regulatory provisions, or
based on bilateral agreement between Air Traffic Control Units, then the requirements
outlined as mandatory in this specification for those messages become mandatory for
implementation. This is required in order to meet the purpose of the messages and to
ensure interoperability between systems. The co-ordination procedure requires that
systems identify whether or not transfers are in accordance with Letters of Agreements
(LoAs). The process which checks such compliance is referred to in the OLDI
Specification as "the filter". The database used for the filter will include the following, if
required:
agreed co-ordination points;
eligible (or ineligible) flight levels which may also be associated with the co-
ordination points;
aerodromes of departure;
destinations;
agreed direct routes ;
time and/or distance limits prior to the COP, after which any co-ordination
message is considered non-standard;
any other conditions, as bilaterally agreed.
All items in this list may be combined to define more complex conditions. The format of
the messages (ICAO PANS/RAC 4444 or EUROCONTROL ADEXP) to be transmitted
and received has to be agreed bilaterally. The address of the ATS units providing the
services has to be agreed and has to be different from the addresses of the other units to
which the ATS units are already connected or planned to be connected. The ATS unit
addresses are part of the OLDI message.
98.2 FLIGHT MANAGEMENT TRASFER PROTOCOL (FMTP)
The Flight Message Transfer Protocol (FMTP) is a communications stack based on
TCP/IPv6 to support the transmission of OLDI messages. FMTP is a state machine that
handles connection establishment and session management. Each FMTP system requires
to be assigned with an identification value that is to be exchanged during connection
establishment. The identification values have to be bilaterally agreed and must be
different from the values of the other units to which the ATS units are already connected
or planned to be connected.
2
The FMTP specification assumes the transfer of ASCII characters, but implementations
of the protocol may wish to extend this support to other character sets or binary transfers.
Further guidance material on FMTP is available from EUROCONTROL at the following
website.
http://www.eurocontrol.int/communications/public/standard_page/com_network.html
98.2.1 Testing OLDI/FMTP
EUROCONTROL has developed a test tool named ETIC to validate OLDI/FMTP
implementations and build test scenarios. The tool can be made available to FMTP
implementation projects upon request. Request for further information on ETIC can be
addressed to etic@eurocontrol.int.
98.3 AMHS
AMHS has already achieved operational status over TCP/IP in the European region and
North American regions. It is to be noted that the European deployments make use of
IPv6 for network interconnections in line with Part II of this document.
Field Code Changed
Field Code Changed

3
APPENDIX A – REFERENCE DOCUMENTS
IETF STANDARDS AND PROTOCOLS
The following documents are available publicly at http://www.ietf.org and form part of
this manual to the extent specified herein. In the event of conflict between the documents
referenced herein and the contents of this manual, the provisions of this manual shall take
precedence.
Request for Comments (RFCs)
netlmm-mn-ar-if
Network-based Localized Mobility Management Interface between
Mobile Node and Mobility Access Gateway, May 2007
RFC 768 User Datagram Protocol, August 1980
RFC 793 Transmission Control Protocol (TCP), September 1981
RFC 1006 ISO Transport Service on top of TCP, May 1987
RFC 1122 Requirements for Internet Hosts – Communication Layers
RFC 1123 Requirements for Internet Hosts – Application and Support
RFC 1323 TCP Extensions for High Performance May 1992
RFC 1981 Path Maximum Transmission Unit (MTU) Discovery for IP Version 6,
August 1996
RFC 2126 ISO Transport Service on top of TCP, March 1997
RFC 2385 Protection of BGP Sessions via the TCP MD5 Signature Option
RFC 2460 Internet Protocol, Version 6 (IPv6) Specification, December 1998
RFC 2474 Differential Services Field, December 1998
RFC 2475 An Architecture for Differentiated Services
RFC 2488 Enhancing TCP over Satellite Channels, January 1999
RFC 2597 Assured Forwarding PHB Group
RFC 2858 Border Gateway Protocol (BGP4) Multiprotocol Extensions June 2000
RFC 3095 Robust Header Compression (ROHC): Framework and four profiles; RTP,
UDP, ESP, and uncompressed
RFC 3241 Robust Header Compresion (ROHC) over PPP
RFC 3246 An Expedited Forwarding Per-Hop Behavior (PHB)
RFC 3602 the AES-CBC Cipher Algorithm and Its Use with IPsec
RFC 3647 Internet X.509 Public Key Infrastructure Certificate Policy and
Certification Practices Framwork
RFC 3775 Mobility Support in IPv6, June 2004
RFC 3963 Network Mobility (NEMO) Basic Support Protocol
RFC 4106 The use of Galois/Counter Mode (GCM) in IPsec Encapsulating Security
Payload (ESP)
RFC 4213 Basic Transition Mechanisms for IPv6 Hosts and Routers
RFC 4271 A Border Gateway Protocol 4 (BGP-4), January 2006
RFC 4291 IP Version 6 Addressing Architecture, February 2006
RFC 4301 Security Architecture for the Internet Protocol, December, 2005
RFC 4302 Internet Protocol (IP) Authentication Header, December 2005
Field Code Changed
4
RFC 4303 IP Encapsulating Security Payload (ESP), December 2005
RFC 4306 Internet Key Exchange (IKEv2) Protocol, December 2005
RFC 4307 Cryptographic Algorithms for Use in the Internet Key Exchange Version 2
(IKEv2), December 2005
RFC 4443 Internet Control Message Protocol (ICMPv6) for the Internet Protocol
Version 6 (IPv6) Specification, March 2006
RFC 4492 Elliptic Curve Cryptography (ECC) Cipher Suites for Transport Layer
Security, May 2006
RFC 4555 IKEv2 Mobility and Multihoming Protocol (MOBIKE), June 2006
RFC 4753 Encription Control Protocol (ECP) Groups for IKE and IKEv2
RFC 4754 IKE and IKEv2 Authentication Using the Elliptic Curve Digital Signature
Algorithm (ECDSA)
RFC 4830 Problem Statement for Network-Based Localized Mobility Management
(NETLMM), April 2007
RFC 4831 Goals for Network-Based Localized Mobility Management (NETLMM),
April 2007
RFC 4835 Cryptographic Algorithm Implementation Requirements for Encapsulating
Security Payload (ESP) and Authentication Header (AH) ,April 2007
RFC 4843 An IPv6 Prefix for Overlay Routable Crytographic Hash Identifiers
(ORCHID)
RFC 4868 Using HMAC-SHA-256, HMAC-SHA-384 and HMAC-SHA-512 with
IPsec
RFC 4877 Mobile IPv6 Operation with IKEv2 and the Revised IPsec Architecture
RFC 4996 Robust Header Compression (ROHC): A Profile for TCP/IP (ROHC-TP)
RFC 5246 The Transport Layer Security (TSL) Protocol Version 1.2
RFC 5280 Internet X.509 Public Key Infrastructure Certificate and Certificate
Revocation List (CRL) Profile
RELEVANT ICAO PUBLICATIONS
In the event of a conflict between the manual and the provisions in Annex 10, the
provisions of Annex 10 shall take precedence.
ICAO Annex 2 Rules of the Air
ICAO Annex 3 Meteorological Service for International Air Navigation
ICAO Annex 10 Aeronautical Telecommunications – Volume III, Part I – Digital Data
Communication Systems
ICAO Annex 11 Air Traffic Services
ICAO Doc. 9705-AN/956 Edition 3, Manual of Technical Provisions for the ATN, 2002
ICAO Doc. 9739 Edition 1, Comprehensive ATN Manual (CAMAL), 2000
ICAO Doc. 4444 Procedures for Air Navigation Services – Air Traffic Management 14
th
Edition, 2001
ICAO Doc. 9694 Manual of Air Traffic Services Data Link Applications
ICAO Doc. 9880 Detailed Technical Specifications for the Aeronautical
Telecommunication Network (ATN) using ISO/OSI protocols

5
EUROCONTROL SPECIFICATIONS
The following documents are available publicly at http://www.eurocontrol.int/ses and
form part of this manual to the extent specified herein. In the event of conflict between
the documents referenced herein and the contents of this manual, the provisions of this
manual shall take precedence.
EUROCONTROL-SPEC-0100 EUROCONTROL Specifications of Interoperability
and Performance Requirements for the Flight
Message Transfer Protocol (FMTP), Edition 2.0,
June 2007
EUROCONTROL-SPEC-0106 EUROCONTROL Specifications for On-Line Data
Interchange (OLDI), Edition 4.0, October 2007
EUROCAE Documents
The following documents are published by Eurocae on:http://www.eurocae.net
ED-136 - VoIP ATM System Operational and Technical Requirements, edition
February 2009
ED-137A - Interoperability Standards for VoIP ATM Components. edition
September 2010. (Part 1: Radio edition September 2010- Part 2: Telephone edition
September 2010- Part 3: Recording edition February 2009- Part 4: Supervision
edition February 2009)
ED-138 - Electronic Copy - Network Requirements and Performances for Voice
over Internet Protocol (VoIP) Air Traffic Management (ATM) Systems ,edition
February 2009(Part 1: Network Specification - Part 2: Network Design Guideline)
ICAO Manuals
ICAO Document 9705 Manual of Technical Provisions for the ATN
ICAO Document 9880 Manual of Technical Provisions for the ATN
ICAO Document 9694 Manual of Air Traffic Services Data Link Applications
Field Code Changed
Comment [Q7]: Action 13-1
1
APPENDIX B – ABBREVIATIONS/DEFINITIONS
The acronyms used in this manual are defined as follows:
AAC Aeronautical Administrative Communications
AF Assured Forwarding
AOC Aeronautical Operational Communications
AS Autonomous System
AH Authentication Header
AIDC ATS Interfacility Data Communications
AINSC Aeronautical Industry Service Communication
AN Access Network
ANSP Air Navigation Service Provider
ATM Air Traffic Management
ATSMHS ATS Message Handling Services
ATN Aeronautical Telecommunication Network
ATC Air Traffic Control
ATS Air Traffic Services
ATSU ATS Unit
ATSC Air Traffic Services Communication
BGP Border Gateway Protocol
CL Connection-less
CN Correspondent Node
CO Connection-oriented
CRL Certificate Revocation List
DiffServ Differential Services
ECC Elliptic Curve Cryptography (ECC)ECP Encryption Control Protocol
EF Expedited Forwarding
ESP Encapsulating Security Protocol
FIR Flight Information Region
FMTP Flight Message Transfer Protocol
G-G Ground- to- Ground
HA Home Agent
HC Handover Control
HMAC Hash Message Authentication Code
2
H-MM Host-based Mobility Management
IANA Internet Assigned Numbers Authority
ICAO International Civil Aviation Organization
ICMP Internet Control Message Protocol
IETF Internet Engineering Task Force
IKEv2 Internet Key Exchange (version2)
IP Internet Protocol
IPS Internet Protocol Suite
IPsec IP Security
IPv4 Internet Protocol version 4
IPv6 Internet Protocol version 6
ISO International Organization for Standardization
LAN Local Area Network
LIR Local Internet Registry
LM Location Management
MM Mobility Management
MN Mobile Node
MOA Memorandum of Agreement
MSP Mobile Service Provider
MTU Maximum Transmission Unit
N-MM Network-based Mobility Management
OLDI On-Line Data Interchange
OSI Open System Interconnection
PHB Per-Hop-Behavior
PPP Point-to-Point Protocol
QoS Quality of Service
RIR Regional Internet Registry
RFC Request for Comments
ROHC Robust Header Compression
RTP Real-time Transport Protocol
TCP Transmission Control Protocol
TLS Transport Layer Security
SARPs Standards and Recommended Practices
SPI Security Parameter Index
UDP User Datagram Protocol
WAN Wide Area Network
3
DEFINITIONS
Definitions are consistent with IETF terminology.
Access Network
A network that is characterized by a specific access technology.
Administrative Domain
An administrative entity in the ATN/IPS. An Administrative Domain can
be an individual State, a group of States, an Aeronautical Industry
Organization (e.g., an Air-Ground Service Provider), or an Air Navigation
Service Provider (ANSP) that manages ATN/IPS network resources and
services. From a routing perspective, an Administrative Domain includes
one or more Autonomous Systems.
ATN/IPS Internetwork
The ATN/IPS internetwork consists of IPS nodes and networks operating
in a multinational environment.
Autonomous System
A connected group of one or more IP prefixes, run by one or more
network operators, which has a single, clearly defined routing policy.
Global Mobility
Global Mobility is mobility across access networks.
Handover Control
The handover control (HC) function is used to provide the ‗session
continuity‘ for the ‗on-going‘ session of the mobile node.
Host A host is a node that is not a router. A host is a computer connected to the
ATN/IPS that provides end users with services.
4
Host-based Mobility Management
A mobility management scheme in which MM signaling is performed by
the mobile node.
IPS Mobile node
an IPS node that uses the services of one or more MSPs.
Local Mobility
Local Mobility is network layer mobility within an access network.
Location Management
The location management (LM) function is used to keep track of the
movement of a mobile node and to locate the mobile node for data
delivery.
Mobility Service Provider (MSP)
is a service provider that provides Mobile IPv6 service (i.e. Home
Agents), within the ATN/IPS. A MSP is an instance of an AD which may
be an ACSP, ANSP, airline, airport authority, government organization,
etc.
Network-based Mobility Management
A mobility management scheme in which the MM signaling is performed
by the network entities on behalf of the mobile node.
Node A device that implements IPv6
Router A router is an node that forwards Internet Protocol (IP) packets not
explicitly addressed to itself. A router manages the relaying and routing
of data while in transit from an originating end system to a destination end
system.
Inter-Domain Routing (Exterior Routing Protocol)
5
Protocols for exchanging routing information between Autonomous
Systems. They may in some cases be used between routers within an AS,
but they primarily deal with exchanging information between Autonomous
Systems.
Intra-Domain Routing (Interior Routing Protocol)
Protocols for exchanging routing information between routers within an
AS.
