Berks County Inmate Handbook
Prisoners in City or County Jails Can Use This Handbook ... Berks County, 2019 WL 211568 (E. D. Pa. Jan. 15,. 2019), the court found the female “trusty ...
Prisoners in City or County Jails Can Use This Handbook ... Berks County, 2019 WL 211568 (E. D. Pa. Jan. 15,. 2019), the court found the female “trusty ...

Berks County Prison, 439. Fed. Appx. 86 (3d Cir. 2011) (disciplinary. "nutraloaf" diet did not deprive inmates of basic life necessities); Stewart v. Beard ...
Aug 27, 2012 ... to an aspect of his imprisonment, the Berks County Prison Inmate Handbook lays out a multi-tier system whereby the inmate may seek formal review ...
Jul 21, 2010 ... THE FAIR DEBT COLLECTION PRACTICES ACT. As amended by Pub. L. 111-203 ... refuse to pay debts, except to a consumer reporting agency or ...
The FDCPA defines a debt collector as any person who regularly collects, or attempts to collect, consumer debts for another person or institution or.
The Fair Debt Collection Practices Act (FDCPA), (15 USC. 1692 et seq ... 604(a)(3) of the Fair Credit Reporting Act. • Advertise a debt for sale to ...
Credit Protection Act (15 USC §1601 et seq.), such as the. Truth in Lending Act and the Fair Debt Collection Practices. Act. Congress subsequently passed the ...
Jun 4, 2004 ... This version of the FCRA includes the amendments to the FCRA set forth in the Consumer Credit Reporting Reform Act of 1996 (Public Law 104-208,.
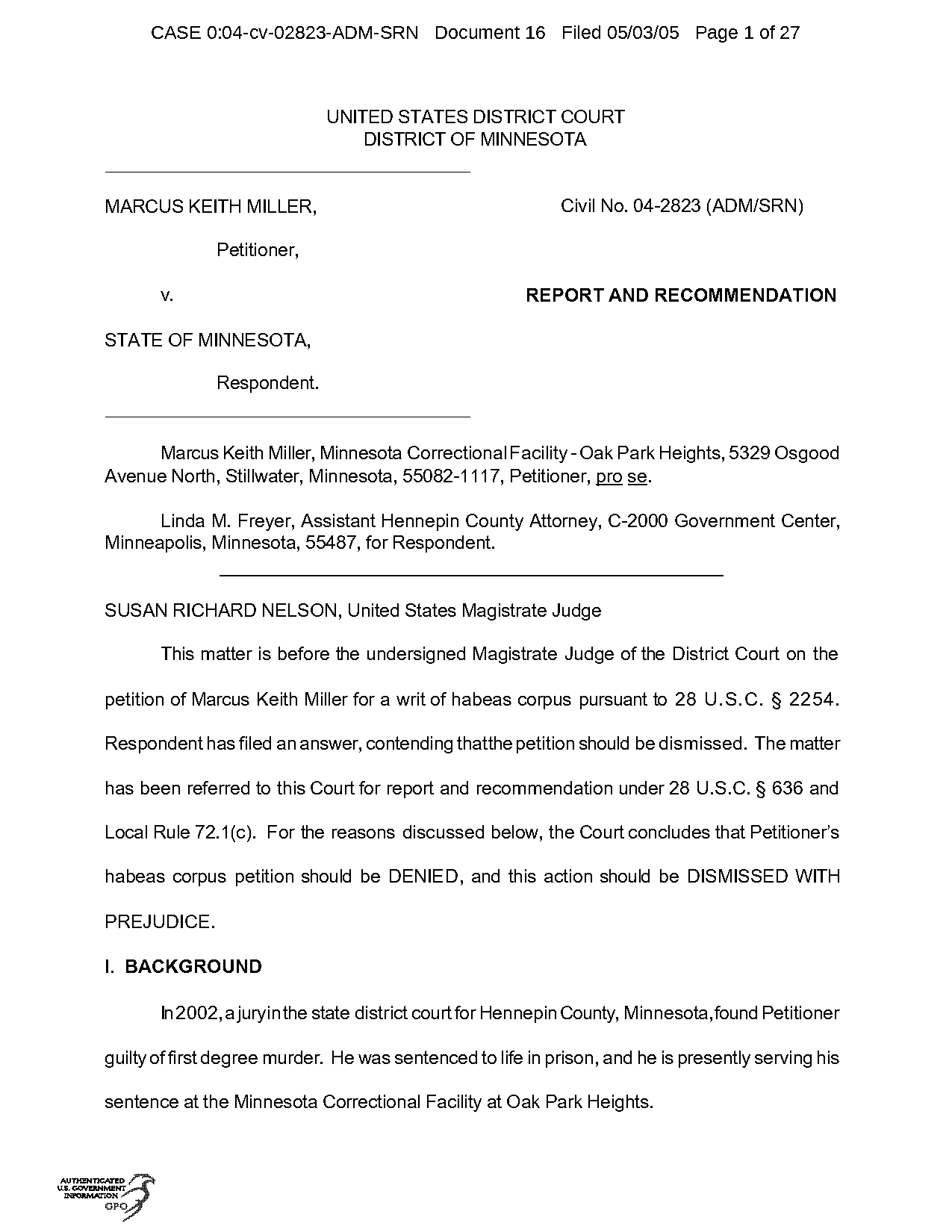
This matter is before the undersigned Magistrate Judge of the District Court on the petition of Marcus Keith Miller for a writ of habeas corpus pursuant to 28 ...
The content of this manual is furnished for informational use only, is subject to change without notice, and should not be construed as a commitment by Keith ...
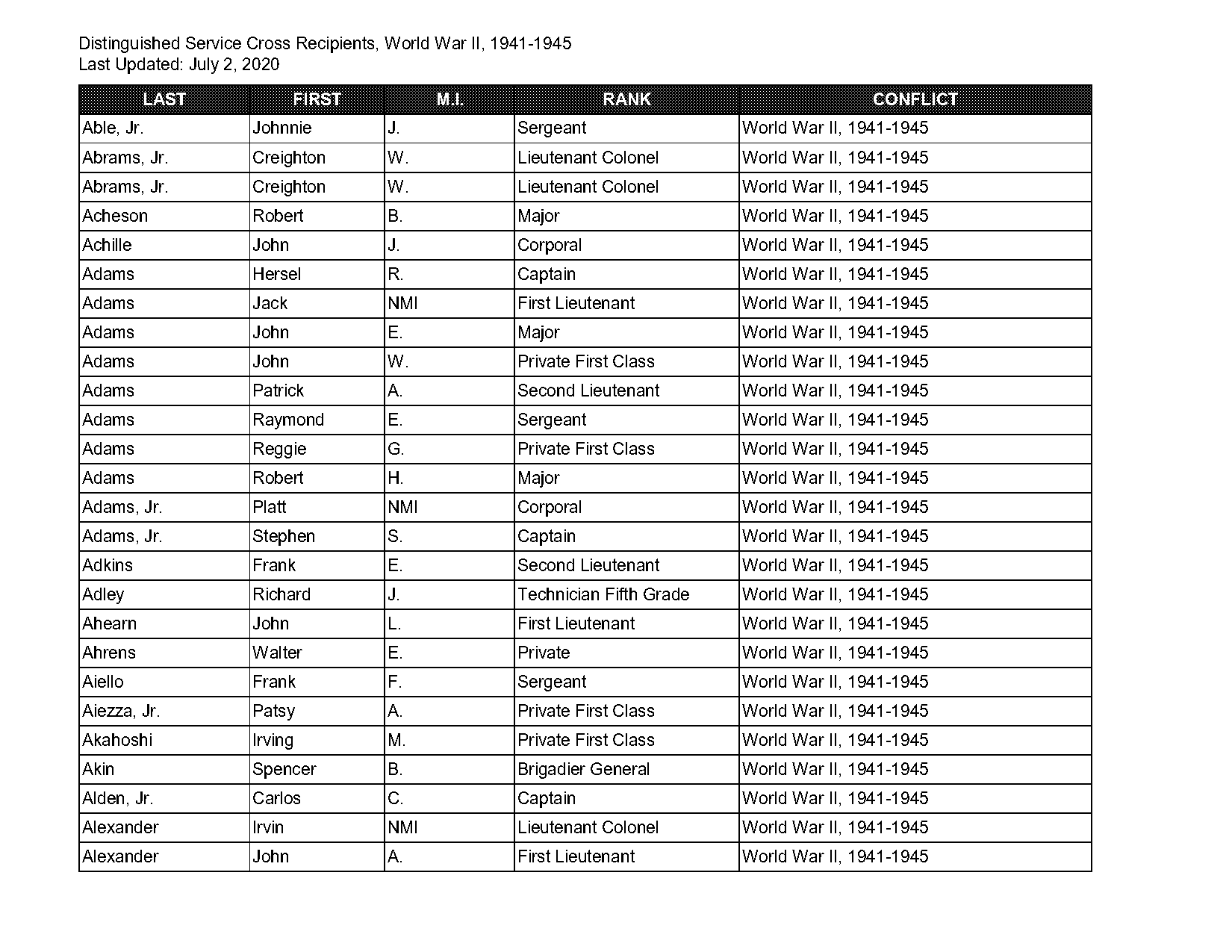
Jul 2, 2020 ... Miller, Jr. Harvey. NMI. Private. World War II, 1941-1945. Miller, Jr ... Notice: Security, privacy, and administrative reasons preclude a ...
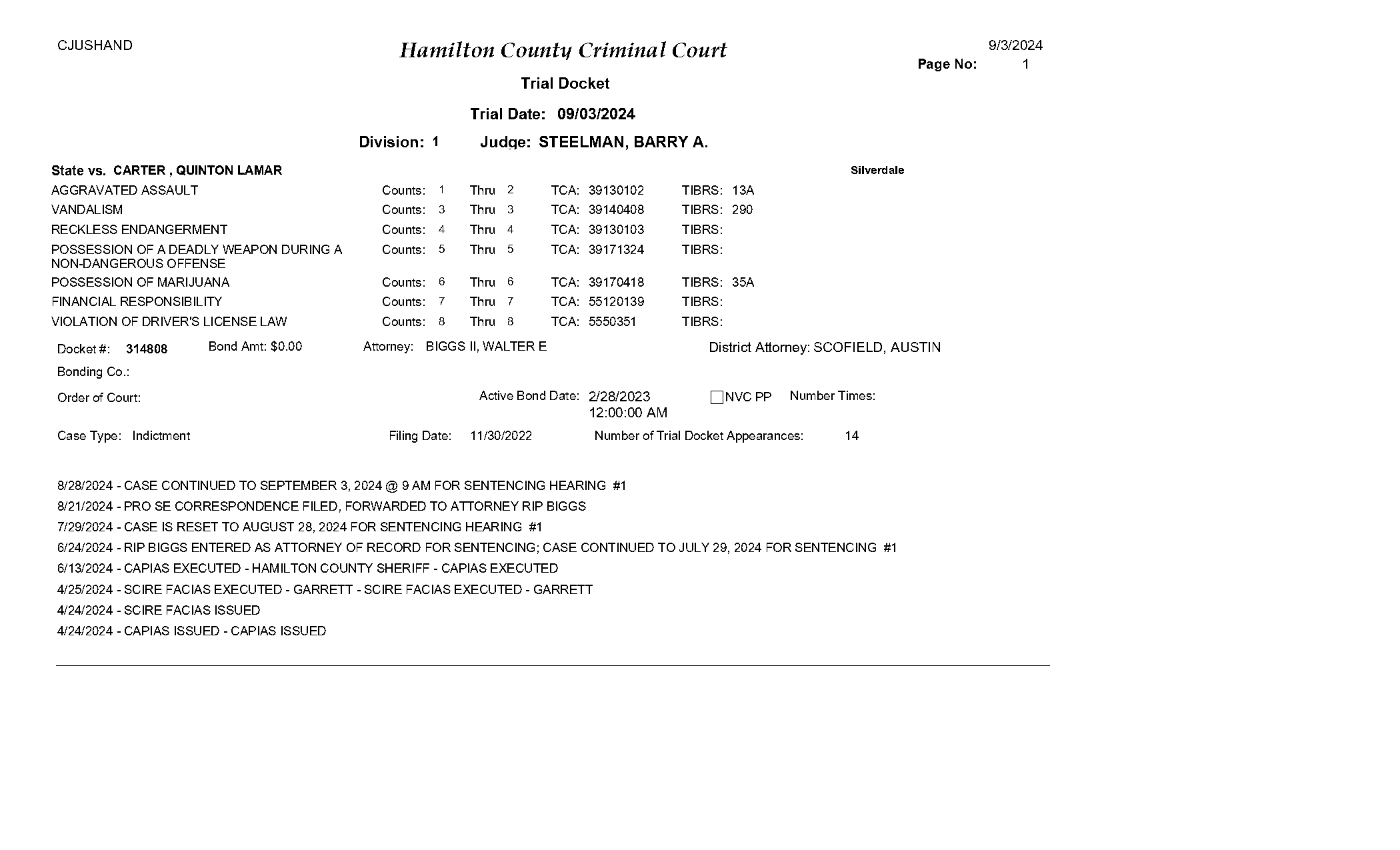
Apr 24, 2024 ... ... MILLER. DRUGS GENERAL CATEGORY FOR RESALE. Counts: 1. Thru 1. TCA ... NOTICE OF ADDITIONAL WITNESSES NOT INCLUDED IN INDICTMENT FILED. 8/15 ...
where aircraft move between the runways and the terminal building. 1 Wikipedia: https://en.wikipedia.org/wiki/Airport_terminal. 5th. Best U.S.. Domestic Airport.
Terminal. Refinery. Aircraft. Airport. Storage. Terminal. Figure A.1. Jet Fuel Distribution System. 1 Another reason to exclude avgas from multiproduct ...
https://en.wikipedia.org/wiki/Internet_of_things. Page 3. KKI I2/R2/K2. Hal ... PLC (Programmable Logic Control) alias RTU (Remote Terminal Unit). □. PLCs ...
Oct 1, 2000 ... Naval Air Station Sigonella (Italy). NATEC. Naval Air Technical Data ... Warehouse Inventory Control System (Air Force see: AWS). Wi-Fi.
Jul 16, 2018 ... 1 Air Terminal Squadron (1ATS) to form into the unit it is today. 1AOSS is currently the most diverse and dispersed unit in the RAAF, with ...
... system while offering superior comfort when compared to traditional air handler terminal units. The compact, lightweight structure within the VRV modular ...
As with singly linked lists, we can recursively define doubly linked lists as either being empty (null) or a node having a reference to a doubly linked list ...
Inserting at the Tail. • create a new node. • chain it and move the tail reference. • ... Deletions at the tail of a singly linked list cannot be done in constant ...

reference to a doubly linked list. ‣ Node: is a data type that holds any ... ‣ Item removeLast(): Retrieves and removes the tail of the doubly linked list.
Cipher Wheel templates. Make a cipher wheel, and use it to send secret messages to your friends and family. Investigate… • Could you work out the encrypted ...
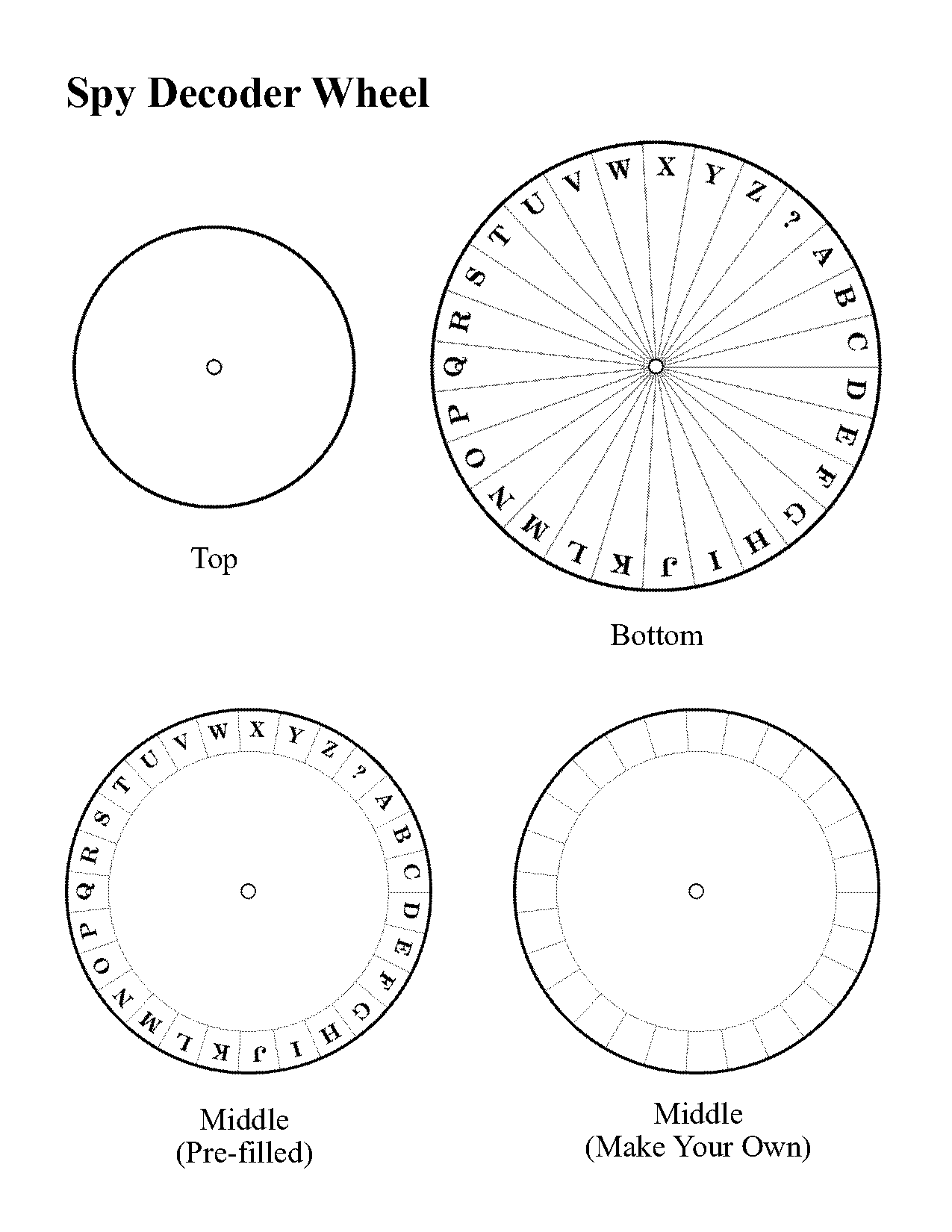
Page 1. Spy Decoder Wheel. Top. Bottom. Middle. (Pre-filled). Middle. (Make Your Own)
Since a node is specific to a linked list, we will define the Node ... first data entry and a reference named the tail points to the node with the ...
Pointer/Pointee. A "pointer" stores a reference to another variable sometimes known as its "pointee". Alternately, a pointer may be set to the value NULL which ...
It works by shifting the letters of the message. For this cipher you will need: scissors, brad fastener and the template labeled Caesar Cipher Wheel (Page 15).
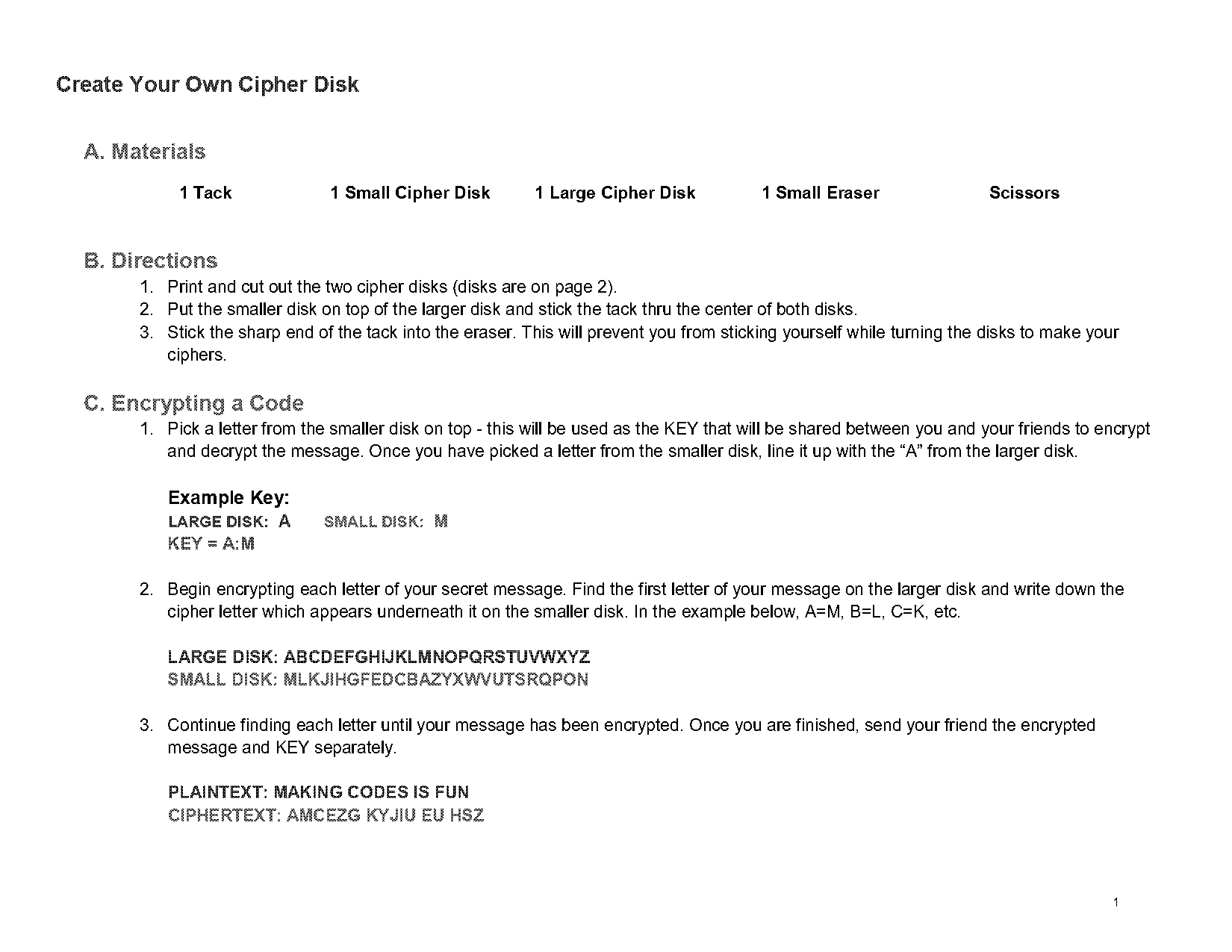
B. Directions. 1. Print and cut out the two cipher disks (disks are on page 2). 2. Put the smaller disk on top of the larger disk and stick the tack thru ...
contents unless you “approve” their request to join. Use caution when ... Any group member or approved follower can screen-shot comments, pictures, etc.
Upon account request approval, you will be able to access and request services from VUMC cores and review invoices. Page 5. 4. Lab Group Management. Accessing & ...
A BIP is intended to support children who have behaviors interfering with learning at school. If a child has an. IEP or 504 plan, the team will decide if an FBA ...